Table Of Safety Contents
ISO 27001 Organizational Qualifying Procedure Risk Assessment Worksheet Information PDF
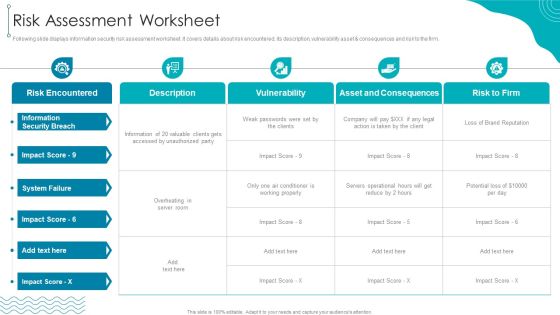
Following slide displays information security risk assessment worksheet. It covers details about risk encountered, its description, vulnerability asset consequences and risk to the firm.Deliver an awe inspiring pitch with this creative ISO 27001 Organizational Qualifying Procedure Risk Assessment Worksheet Information PDF bundle. Topics like Information Security, Risk Encountered, Asset And Consequences can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Big Data And Analytics Framework Implementation Challenges Themes PDF
This slide provide information about various challenges faced while implementing big data and analytics architecture in organization along with its solutions. It includes challenges such as complexity, skillset, technology maturity and security Pitch your topic with ease and precision using this Big Data And Analytics Framework Implementation Challenges Themes PDF. This layout presents information on Challenges, Description, Solutions . It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Information Technology Transformation Playbook Strategic IT Infrastructure Enhancement Elements PDF
This slide provides information regarding IT infrastructure enhancement roadmap tracking activities associated to testing, improvements, integrations, security, etc. Deliver and pitch your topic in the best possible manner with this information technology transformation playbook strategic it infrastructure enhancement elements pdf. Use them to share invaluable insights on required, infrastructure, security and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Convergence Strategy Information Enterprise Technical Challenges Ppt Ideas Graphic Images
This slide covers technical challenges such as environmental, compatibility, skills shortage and security in enterprise while making IT OT convergence. Deliver and pitch your topic in the best possible manner with this Convergence Strategy Information Enterprise Technical Challenges Ppt Ideas Graphic Images. Use them to share invaluable insights on Environmental, Compatibility, Skills Shortage, Security and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
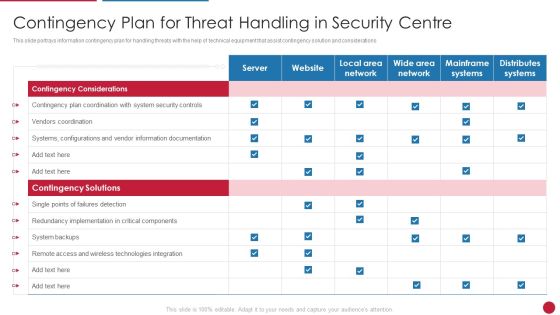
Facilitating IT Intelligence Architecture Contingency Plan For Threat Handling In Security Centre Professional PDF
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations Deliver and pitch your topic in the best possible manner with this Facilitating IT Intelligence Architecture Contingency Plan For Threat Handling In Security Centre Professional PDF Use them to share invaluable insights on Contingency Solutions, Contingency Considerations, Information Documentation and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Checklist To Ensure Secure Mobile Banking Ppt Inspiration Deck PDF
This slide shows checklist which can be used to adopt various security measure while using mobile banking. It includes tasks such as change passwords frequently, monitor transactions, avoid using public networks. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Checklist To Ensure Secure Mobile Banking Ppt Inspiration Deck PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.

Critical Challenges Related To Data Lake Data Lake Creation With Hadoop Cluster Inspiration PDF
This slide depicts the challenges of data lakes such as high cost, managed difficulty, long time-to-value, immature data security governance, and lack of skills.Do you know about Slidesgeeks Critical Challenges Related To Data Lake Data Lake Creation With Hadoop Cluster Inspiration PDF These are perfect for delivering any kind od presentation. Using it, create PowerPoint presentations that communicate your ideas and engage audiences. Save time and effort by using our pre-designed presentation templates that are perfect for a wide range of topic. Our vast selection of designs covers a range of styles, from creative to business, and are all highly customizable and easy to edit. Download as a PowerPoint template or use them as Google Slides themes.

Comparison Of Various Security Awareness Training Software Elements PDF
The purpose of this slide is to drawn comparison of multiple software which can be used to provide cyber security training to the key stakeholders. Information covered in this slide is related to phishing simulations, security reporting, individualized security training plan etc. Deliver and pitch your topic in the best possible manner with this Comparison Of Various Security Awareness Training Software Elements PDF. Use them to share invaluable insights on Individualized Security, Industry Specific, Deployment and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Inbound And Outbound Services Business Profile Integrated Performance Of The Company Brochure PDF
This slide highlights the integrated performance of call center which covers different elements such as jobs created, percentage of women, renewable energy consumption, employees trained on data security and code of conduct.Deliver an awe inspiring pitch with this creative Inbound And Outbound Services Business Profile Integrated Performance Of The Company Brochure PDF bundle. Topics like Percentage Of Women, Agents Trained, Technology And Analytics can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Impact Categories For Effectively Handling Cyber Security Incidents Download PDF
Mentioned slide provides information about the impact categories which can be used for effectively handling various cyber security incidents. Categories covered are function, information and recoverability impact.Deliver an awe inspiring pitch with this creative Impact Categories For Effectively Handling Cyber Security Incidents Download PDF bundle. Topics like Functional Impact, Information Impact, Recoverability Impact can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
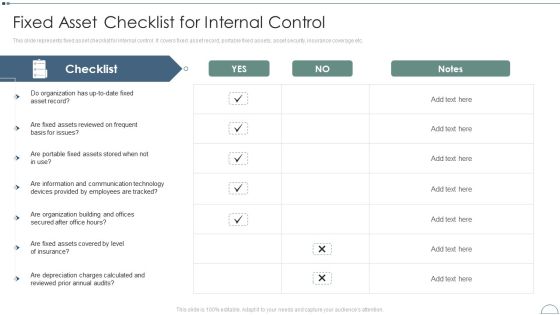
Fixed Asset Management Framework Implementation Fixed Asset Checklist For Internal Control Themes PDF
This slide represents fixed asset checklist for internal control. It covers fixed asset record, portable fixed assets, asset security, insurance coverage etc.Deliver and pitch your topic in the best possible manner with this Fixed Asset Management Framework Implementation Fixed Asset Checklist For Internal Control Themes PDF Use them to share invaluable insights on Assets Reviewed, Portable Fixed, Communication Technology and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Implementing Fixed Asset Management Fixed Asset Checklist For Internal Control Microsoft PDF
This slide represents fixed asset checklist for internal control. It covers fixed asset record, portable fixed assets, asset security, insurance coverage etc. Deliver an awe inspiring pitch with this creative Implementing Fixed Asset Management Fixed Asset Checklist For Internal Control Microsoft PDF bundle. Topics like Checklist, Organization, Insurance can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Technology Facility Maintenance And Provider What Services Do We Offer To Clients Inspiration PDF
This slide provides information regarding the various services that are offered to the clients. The services include - server monitoring, backup monitoring, patch management, etc. Deliver an awe inspiring pitch with this creative technology facility maintenance and provider what services do we offer to clients inspiration pdf bundle. Topics like server monitoring, patch management, performance reporting, automated maintenance, endpoint security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Auditing Committees For Food Quality Review Food Security Excellence Ppt Summary Example Topics PDF
This slide provides information regarding the different committees such as steering committees, general assembly meet, will review overall quality. Deliver an awe inspiring pitch with this creative auditing committees for food quality review food security excellence ppt summary example topics pdf bundle. Topics like acceptance criteria, quality audit review, corrective actions, quality document control, prepared quality control can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Cyber Security Administration In Organization Contingency Plan For Cyber Threat Handling Brochure PDF
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations Deliver an awe inspiring pitch with this creative cyber security administration in organization contingency plan for cyber threat handling brochure pdf bundle. Topics like contingency, implementation, components, documentation, technologies can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Cybersecurity Guidelines IT Information Technology Policy Implementation Budget For FY2022 Icons PDF
This slide represents the companys IT policy implementation budget for FY2022. It covers the details of the software application and security services that need to be purchased and updated. This Cybersecurity Guidelines IT Information Technology Policy Implementation Budget For FY2022 Icons PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Cybersecurity Guidelines IT Information Technology Policy Implementation Budget For FY2022 Icons PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today
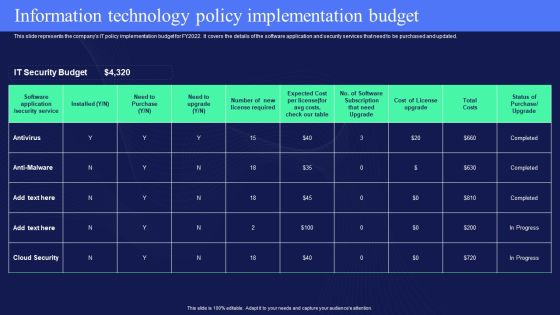
IT Policies And Procedures Information Technology Policy Implementation Budget Template PDF
This slide represents the companys IT policy implementation budget for FY2022. It covers the details of the software application and security services that need to be purchased and updated. This modern and well-arranged IT Policies And Procedures Information Technology Policy Implementation Budget Template PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint, no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.

Cloud Access Security Broker Use Cases Ppt PowerPoint Presentation File Background Images PDF
This slide represents the use cases of cloud access security broker. The purpose of this slide is to showcase the multiple use cases of cloud access security broker, covering protection against threats, governing usage, securing data, and enforcing data loss and compliance policies. This Cloud Access Security Broker Use Cases Ppt PowerPoint Presentation File Background Images PDF from Slidegeeks makes it easy to present information on your topic with precision. It provides customization options, so you can make changes to the colors, design, graphics, or any other component to create a unique layout. It is also available for immediate download, so you can begin using it right away. Slidegeeks has done good research to ensure that you have everything you need to make your presentation stand out. Make a name out there for a brilliant performance.

Summary Existing Security Management Capabilities Ppt Outline Themes PDF
Following slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating. Deliver an awe inspiring pitch with this creative summary existing security management capabilities ppt outline themes pdf bundle. Topics like security, information, average can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
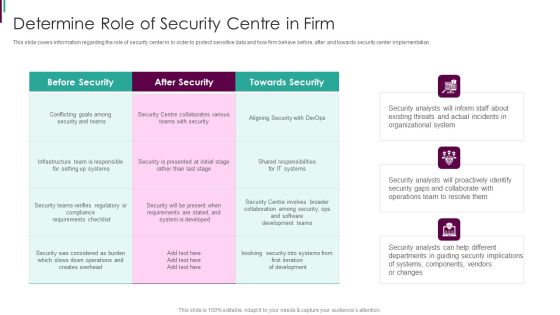
Developing Business Analytics Framework Determine Role Of Security Centre In Firm Brochure PDF
This slide covers information regarding the role of security center in in order to protect sensitive data and how firm behave before, after and towards security center implementation. Deliver an awe inspiring pitch with this creative Developing Business Analytics Framework Determine Role Of Security Centre In Firm Brochure PDF bundle. Topics like Before Security, After Security, Towards Security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Data Breach Prevention Recognition Organization Impact Metrics Behaviours Pictures PDF
This slide covers the metrics which measures the effect of the preparation on security awareness such as does training affecting the habits, behaviors, or beliefs of people.Deliver an awe-inspiring pitch with this creative data breach prevention recognition organization impact metrics behaviours pictures pdf bundle. Topics like organization impact metrics behaviours can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Analyzing The Impact Of Security Threats On Organization Elements PDF
This slide showcases impact of information breach on different assets which can help organization in formulating risk monitoring policy. Its key components are criterion, criterion weight and information assets .Deliver and pitch your topic in the best possible manner with this Analyzing The Impact Of Security Threats On Organization Elements PDF. Use them to share invaluable insights on Security Threats, Impact Organization, Average Financial and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
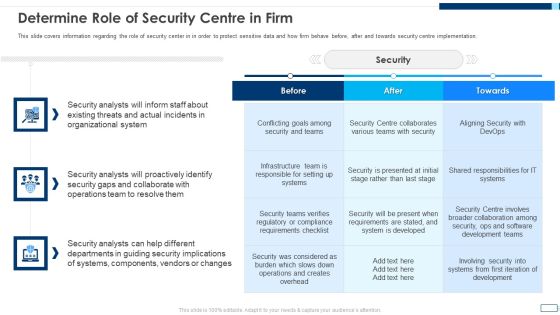
Evolving BI Infrastructure Determine Role Of Security Centre In Firm Summary PDF
This slide covers information regarding the role of security center in in order to protect sensitive data and how firm behave before, after and towards security centre implementation. Deliver an awe inspiring pitch with this creative evolving bi infrastructure determine role of security centre in firm summary pdf bundle. Topics like organizational, security analysts, collaborate can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
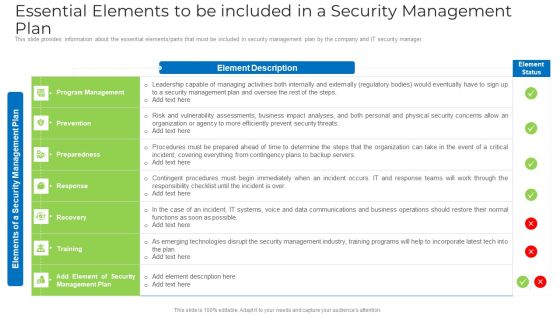
Essential Elements To Be Included In A Security Management Plan Elements PDF
This slide provides information about the essential elements or parts that must be included in security management plan by the company and IT security manager. Deliver an awe inspiring pitch with this creative essential elements to be included in a security management plan elements pdf bundle. Topics like risk, organization, security, systems, data communications can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Intelligent Infrastructure Determine Role Of Security Centre In Firm Graphics PDF
This slide covers information regarding the role of security center in in order to protect sensitive data and how firm behave before, after and towards security centre implementation. Deliver an awe inspiring pitch with this creative Intelligent Infrastructure Determine Role Of Security Centre In Firm Graphics PDF bundle. Topics like Security, Organizational System, Operations Team, Conflicting Goals can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Facilitating IT Intelligence Architecture Determine Role Of Security Centre In Firm Demonstration PDF
This slide covers information regarding the role of security center in in order to protect sensitive data and how firm behave before, after and towards security centre implementation. Deliver an awe inspiring pitch with this creative Facilitating IT Intelligence Architecture Determine Role Of Security Centre In Firm Demonstration PDF bundle. Topics like Organizational System, Security Analysts, Collaborate With Operations can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Blockchain Business Methodology Impact On Business Operations Information PDF
This slide covers the details related to the advantages of blockchain technology for business. The purpose of this template is to defines blockchain as it helps to increase trust, security, transparency and bring other benefits to businesses. It includes details related to innovation, reduced cost, etc. Pitch your topic with ease and precision using this Blockchain Business Methodology Impact On Business Operations Information PDF. This layout presents information on Innovation, Security And Privacy, Tokenization, Cost. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Corporate Security And Risk Management Budget For Effective Threat Management At Workplace Portrait PDF
Firm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Deliver an awe inspiring pitch with this creative corporate security and risk management budget for effective threat management at workplace portrait pdf bundle. Topics like incident management, risk management, client onboarding process, document management, information management can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Facilities Rendered By Security Centre Implementation Ppt Pictures Design Templates PDF
This slide provides information regarding the various facilities that are offered by successful implementation of security center in the organization in terms if malware detection, phishing detection, investigations by HR, risk mitigation, etc. Deliver an awe inspiring pitch with this creative facilities rendered by security centre implementation ppt pictures design templates pdf bundle. Topics like Determine, organization, Security, Systems, data can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Enhancing B2B Demand Creation And Sales Growth Determine B2B Purchase Decision Maker Assessment Information PDF
This slide provides information regarding B2B purchase decision maker assessment in terms of decision maker role, influence level, buy in, support quotient, etc. Deliver and pitch your topic in the best possible manner with this enhancing b2b demand creation and sales growth determine b2b purchase decision maker assessment information pdf. Use them to share invaluable insights on marketing, decision maker, data security, sale and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
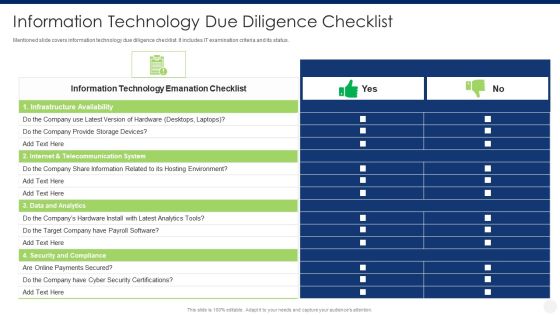
Merger And Acquisition Due Diligence Information Technology Due Diligence Checklist Structure PDF
Mentioned slide covers information technology due diligence checklist. It includes IT examination criteria and its status. Deliver and pitch your topic in the best possible manner with this merger and acquisition due diligence information technology due diligence checklist structure pdf. Use them to share invaluable insights on infrastructure availability, internet and telecommunication system, data and analytics, security and compliance and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Difference Between Cloud Security Solutions And Traditional It Solutions Cloud Computing Security IT Ppt Ideas Example Topics PDF
This slide represents the difference between cloud security solutions and traditional IT solutions based on information centers, cost, scalability, and expenses. Deliver an awe inspiring pitch with this creative difference between cloud security solutions and traditional it solutions cloud computing security it ppt ideas example topics pdf bundle. Topics like cloud security, traditional it security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

IT Security Program To Measure Likelihood Of Impact Topics PDF
This slide represents the information security program to measure likelihood of impact which includes effects, system operationality that will help company to categorize risk level and develop risk mitigation strategies.Pitch your topic with ease and precision using this IT Security Program To Measure Likelihood Of Impact Topics PDF This layout presents information on System Operationality, Uncontrollable Situations, Confidentiality It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Current Security Management Plan Critical Success Factors Infographics PDF
This slide shows some of the current IT Security Management Critical Success Factors of the company prior to the proactive measures taken by the company to mitigate security management problems and implementing an advanced Information Security Management System.Deliver an awe inspiring pitch with this creative Current security management plan critical success factors infographics pdf bundle. Topics like security incidents level, security management, critical success factors can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Current Security Management Plan Critical Success Factors Topics PDF
This slide shows some of the current IT Security Management Critical Success Factors of the company prior to the proactive measures taken by the company to mitigate security management problems and implementing an advanced Information Security Management System.Deliver an awe inspiring pitch with this creative current security management plan critical success factors topics pdf bundle. Topics like security management, intrusion attempts, security implementation can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
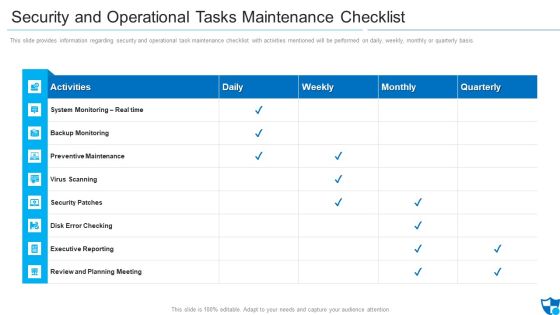
Security And Operational Tasks Maintenance Checklist Infographics PDF
This slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis.Deliver an awe inspiring pitch with this creative security and operational tasks maintenance checklist infographics pdf bundle. Topics like preventive maintenance, security patches, review and planning meeting can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Effective IT Risk Management Process Present Security Management Formats PDF
Following slide shows the current security management capabilities of the firm. It covers details about core functions, its description, key enablers, required and actual standard ratings. Deliver and pitch your topic in the best possible manner with this effective it risk management process present security management formats pdf. Use them to share invaluable insights on information, risk, security, plan and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

6 Level IT Security Plan Maturity Model Slides PDF
This slide represent 6 level cyber security strategy maturity model illustrating levels such as initial, developing, defined, managed, optimization and unified. Pitch your topic with ease and precision using this 6 Level IT Security Plan Maturity Model Slides PDF. This layout presents information on Awareness, Organization Security, Metrics To Measure. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

IT Security For Remote Workplace Plan Checklist Introduction PDF
This slide represents cyber security for remote workplace checklist illustrating approval of remote platforms, employee training, deployment of firewall etc. Pitch your topic with ease and precision using this IT Security For Remote Workplace Plan Checklist Introduction PDF. This layout presents information on Security Measures, Employees, Team. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

IT Risk Management Framework To Manage Security Threats Background PDF
This slide provides information regarding the implementation of IT risk management framework to monitor security threats. The initiatives include the implementation of an enterprise security program, deploy a control environment, etc. There are so many reasons you need a IT Risk Management Framework To Manage Security Threats Background PDF. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
Addressing Compliance Classes In Iot Security Framework Ppt Icon Smartart
This slide provides information regarding different compliance classes in IoT security framework catering different security objective. Find a pre designed and impeccable Addressing Compliance Classes In Iot Security Framework Ppt Icon Smartart. The templates can ace your presentation without additional effort. You can download these easy to edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

Software Checklist To Respond Cyber Security Cases Action Plan Ppt PowerPoint Presentation File Visuals PDF
This slide provides checklist of operating systems used in responding to cyber threat incidents. The purpose of this checklist is to use most appropriate software to respond and to reduce risk. It includes incidents such as information leakage, password change, data stealing etc. Pitch your topic with ease and precision using this Software Checklist To Respond Cyber Security Cases Action Plan Ppt PowerPoint Presentation File Visuals PDF. This layout presents information on Cyber Security, Confidential Information Leakage, Hacker Changed Password. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Current Security Management Plan Critical Success Factors Formats PDF
This slide shows some of the current IT Security Management Critical Success Factors of the company prior to the proactive measures taken by the company to mitigate security management problems and implementing an advanced Information Security Management System. Deliver and pitch your topic in the best possible manner with this current security management plan critical success factors formats pdf. Use them to share invaluable insights on security, management, implementation and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
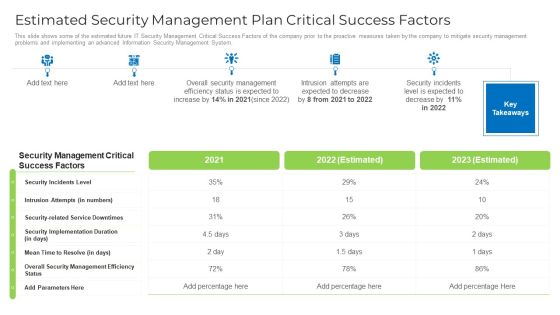
Estimated Security Management Plan Critical Success Factors Designs PDF
This slide shows some of the estimated future IT Security Management Critical Success Factors of the company prior to the proactive measures taken by the company to mitigate security management problems and implementing an advanced Information Security Management System. Deliver and pitch your topic in the best possible manner with this estimated security management plan critical success factors designs pdf. Use them to share invaluable insights on security, management, implementation and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
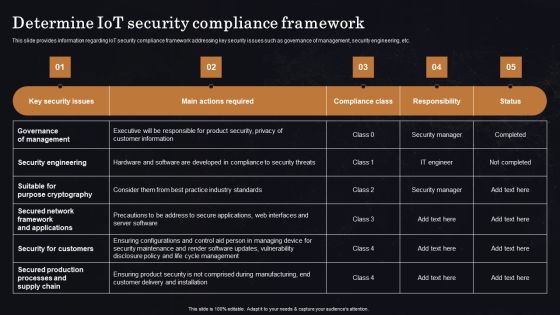
Determine Iot Security Compliance Framework Ppt Professional Vector PDF
This slide provides information regarding IoT security compliance framework addressing key security issues such as governance of management, security engineering, etc. Get a simple yet stunning designed Determine Iot Security Compliance Framework Ppt Professional Vector PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy to edit Determine Iot Security Compliance Framework Ppt Professional Vector PDF can be your go to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.

Cyber Security Risk Management Plan System Disposal Checklist Introduction PDF
Mentioned slide shows system disposal checklist. It covers information such as system requirement, its compliance and remarks. Deliver an awe inspiring pitch with this creative cyber security risk management plan system disposal checklist introduction pdf bundle. Topics like system disposal checklist can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Accounting Actual Business Analysis Method Ppt Show Information PDF
Deliver an awe inspiring pitch with this creative accounting actual business analysis method ppt show information pdf bundle. Topics like inventory, investment, securities, sale, equipment can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
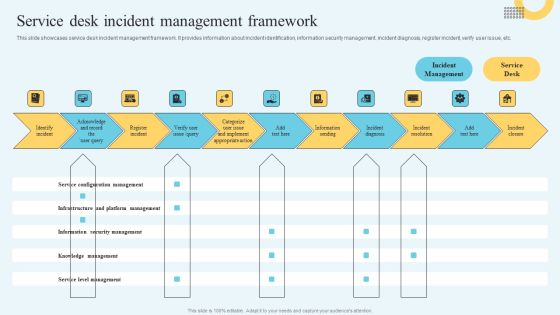
Incident Management Ticketing Service Desk Incident Management Framework Brochure PDF
This slide showcases service desk incident management framework. It provides information about incident identification, information security management, incident diagnosis, register incident, verify user issue, etc. Slidegeeks is here to make your presentations a breeze with Incident Management Ticketing Service Desk Incident Management Framework Brochure PDF With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, youre sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether youre giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.
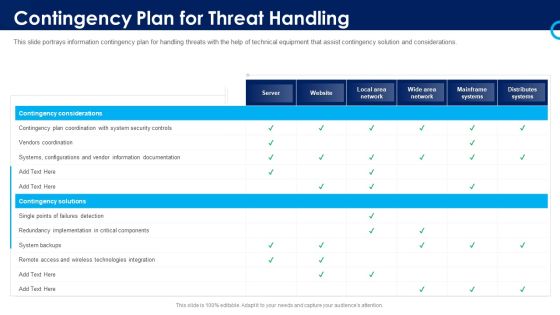
Organizational Security Solutions Contingency Plan For Threat Handling Pictures PDF
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an awe inspiring pitch with this creative organizational security solutions contingency plan for threat handling pictures pdf bundle. Topics like contingency considerations, mainframe systems, security, implementation, technologies integration can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Security Training Program Frameworks Ppt Outline Layout Ideas PDF
This slide outlines the criteria, describes possible positions that could be subject to instruction, instruction information sources, and metrics to assess training success in those control areas. Deliver and pitch your topic in the best possible manner with this security training program frameworks ppt outline layout ideas pdf. Use them to share invaluable insights on requirements, metrics, systems security, materials and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Contingency Plan For Threat Handling In Security Centre Demonstration PDF
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an awe inspiring pitch with this creative contingency plan for threat handling in security centre demonstration pdf bundle. Topics like contingency plan for threat handling in security centre can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Cyber Security Management Risk Plan Ppt Outline Designs PDF
This slide showcases cyber security issues and action plan to mitigate the risks as per their priority. Risks are prioritized based on their confidentiality, integrity and availability. Pitch your topic with ease and precision using this Cyber Security Management Risk Plan Ppt Outline Designs PDF. This layout presents information on Risk Mitigation Plan, Risk, Confidentiality. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

How Management Enables Effective Corporate Security Governance Designs PDF
This slide portrays information regarding the management role in effective corporate security governance by highlight management level, strategic alignment, risk management, etc. There are so many reasons you need a How Management Enables Effective Corporate Security Governance Designs PDF. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
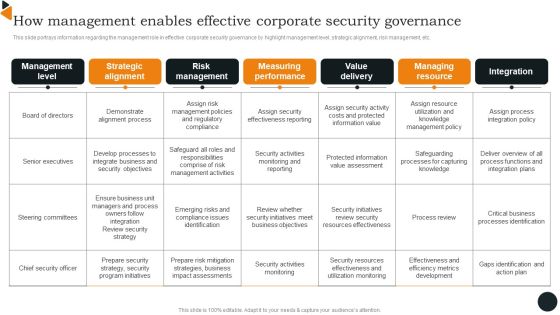
How Management Enables Effective Corporate Security Governance Brochure PDF
This slide portrays information regarding the management role in effective corporate security governance by highlight management level, strategic alignment, risk management, etc. There are so many reasons you need a How Management Enables Effective Corporate Security Governance Brochure PDF. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.

Resolving Integrate IOT Security Challenges With Blockchain Platform Structure PDF
This slide covers various challenges and issues faced while using IoT applications. The purpose of this slide is to provide information about various challenges and proposed solutions. It includes challenges such as RPL routing attack, cost and capacity constraints, cloud server downtime along with description and blockchain solutions. Pitch your topic with ease and precision using this Resolving Integrate IOT Security Challenges With Blockchain Platform Structure PDF. This layout presents information on Iot Challenges, Blockchain Solutions, Cloud Server Downtime. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
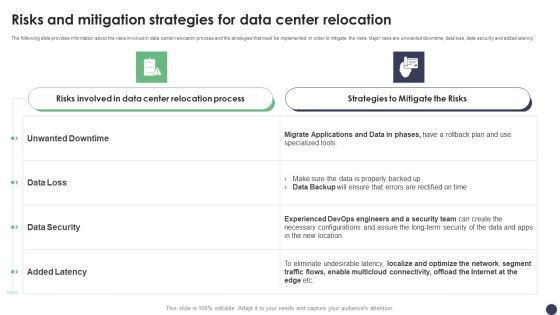
Risks And Mitigation Strategies For Data Center Relocation Ppt PowerPoint Presentation File Example PDF
The following slide provides information about the risks involved in data center relocation process and the strategies that must be implemented in order to mitigate the risks. Major risks are unwanted downtime, data loss, data security and added latency. If you are looking for a format to display your unique thoughts, then the professionally designed Risks And Mitigation Strategies For Data Center Relocation Ppt PowerPoint Presentation File Example PDF is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Risks And Mitigation Strategies For Data Center Relocation Ppt PowerPoint Presentation File Example PDF and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.

Mitigating Cybersecurity Threats And Vulnerabilities Selecting Secured Threat Formats PDF
This slide will help firm in choosing the suitable automated threat management software which is to handle existing security and privacy issues and predict upcoming threats. The firm will choose effective software with features such as automated workflows, centralized platform, etc. Deliver an awe inspiring pitch with this creative mitigating cybersecurity threats and vulnerabilities selecting secured threat formats pdf bundle. Topics like information security prevention, api integration, security incident can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Effective Security Operations Tools To Prevent Cyber Threats Formats PDF
This slide includes some SecOps tools that provide a more secure working environment to organisations by improving collaboration between operations and security teams. It includes elements such as tools, pricing, features, rating, free version, and free trial. Pitch your topic with ease and precision using this Effective Security Operations Tools To Prevent Cyber Threats Formats PDF. This layout presents information on Develops, Organization Security, Compliance Requirements. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Addressing Role Of Chief Security Officer At Workplace Clipart PDF
This slide provides information regarding role of chief security officer at workplace and determine their key priorities in terms of day to day operations, security, compliance, innovation, etc. Create an editable Addressing Role Of Chief Security Officer At Workplace Clipart PDF that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre designed presentation templates help save time. Addressing Role Of Chief Security Officer At Workplace Clipart PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
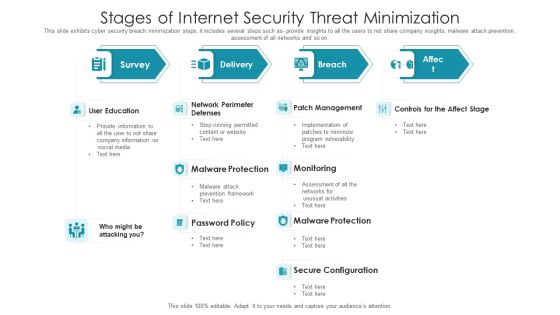
Stages Of Internet Security Threat Minimization Summary PDF
This slide exhibits cyber security breach minimization steps, it includes several steps such as- provide insights to all the users to not share company insights, malware attack prevention, assessment of all networks and so on. Pitch your topic with ease and precision using this stages of internet security threat minimization summary pdf. This layout presents information on patch management, monitoring, malware protection, secure configuration, user education. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

 Home
Home