Safety Performance
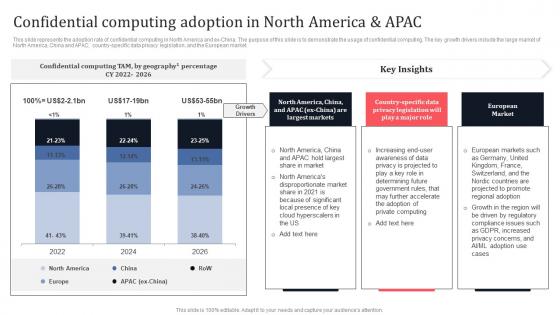
Confidential Computing Adoption In North America And APAC Secure Multi Party Brochure Pdf
This slide represents the adoption rate of confidential computing in North America and ex-China. The purpose of this slide is to demonstrate the usage of confidential computing. The key growth drivers include the large market of North America, China and APAC, country-specific data privacy legislation, and the European market. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Confidential Computing Adoption In North America And APAC Secure Multi Party Brochure Pdf will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.

Organizing Security Awareness Measuring Security Awareness Campaign Results Download PDF
The purpose of this slide is to showcase various key performance indicator KPIs which can assist the company to effectively track cyber security awareness campaign results. The KPIs are phishing rate, self-reported incidents, security breaches, cost of security breach and campaign participation rate. Explore a selection of the finest Organizing Security Awareness Measuring Security Awareness Campaign Results Download PDF here. With a plethora of professionally designed and pre-made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Organizing Security Awareness Measuring Security Awareness Campaign Results Download PDF to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.

Career Golden Key Future PowerPoint Templates Ppt Background For Slides 1112
We present our Career Golden Key Future PowerPoint Templates PPT Background For Slides 1112.Use our Security PowerPoint Templates because,It shows the pyramid which is a symbol of the desire to reach the top in a steady manner. Use our Business PowerPoint Templates because, Infrastructure growth is an obvious requirement of today.Inform your group on how exactly this potential is tailor made for you Use our Future PowerPoint Templates because, It helps your team to align their arrows to consistently be accurate. Use our Leadership PowerPoint Templates because, This slide Probe the minds of your colleagues, see their faces light up as they assimilate and understand the value of your suggestions. Use our Success PowerPoint Templates because, The success of your venture depends on the performance of every team member.Use these PowerPoint slides for presentations relating to Career gold key, future, security, business, leadership, success. The prominent colors used in the PowerPoint template are Black, Yellow, Brown

IT Security Automation Systems Guide Measure Security Automation Metrics For Operations Efficiency Mockup PDF
This slide highlights the security automation metrics for operation efficiency which includes time to remediation, operation performance improvements, sensor value and workflow effectiveness metrics. Crafting an eye catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward IT Security Automation Systems Guide Measure Security Automation Metrics For Operations Efficiency Mockup PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal IT Security Automation Systems Guide Measure Security Automation Metrics For Operations Efficiency Mockup PDF that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers.
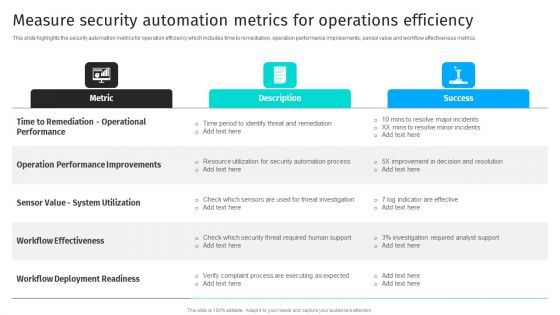
Security Automation To Analyze And Mitigate Cyberthreats Measure Security Automation Metrics Summary PDF
This slide highlights the security automation metrics for operation efficiency which includes time to remediation, operation performance improvements, sensor value and workflow effectiveness metrics.Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Security Automation To Analyze And Mitigate Cyberthreats Measure Security Automation Metrics Summary PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Security Automation To Analyze And Mitigate Cyberthreats Measure Security Automation Metrics Summary PDF that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers.

CYBER Security Breache Response Strategy Cyber Security Incident Response Kpi Dashboard Rules PDF
This slide represents dashboard showing the key metrics of cyber security incident response. It includes key performance indicators such as risk score, compliance status, threat level etc. Crafting an eye catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward CYBER Security Breache Response Strategy Cyber Security Incident Response Kpi Dashboard Rules PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal CYBER Security Breache Response Strategy Cyber Security Incident Response Kpi Dashboard Rules PDF that effortlessly grabs the attention of your audience. Begin now and be certain to wow your customers.
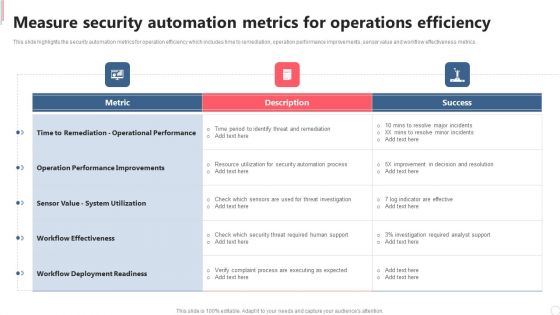
Cyber Security Automation Framework Measure Security Automation Metrics For Operations Efficiency Formats PDF
This slide highlights the security automation metrics for operation efficiency which includes time to remediation, operation performance improvements, sensor value and workflow effectiveness metrics. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Cyber Security Automation Framework Measure Security Automation Metrics For Operations Efficiency Formats PDF to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.

Cybersecurity Operations Cybersecops Limitations Of SOC As A Service Model Template PDF
This slide depicts the challenges of adopting SOC as a service. The purpose of this slide is to highlight the main limitations of SOC as a service, including the onboarding process, enterprising data security, cost of log delivery, regulatory considerations, no dedicated IT security team, and limited customized options. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy to edit and customizable templates. Cybersecurity Operations Cybersecops Limitations Of SOC As A Service Model Template PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.

Implementing Cyber Security Incident Enterprise Cyber Risk Dashboard Professional PDF
This slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Implementing Cyber Security Incident Enterprise Cyber Risk Dashboard Professional PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Implementing Cyber Security Incident Enterprise Cyber Risk Dashboard Professional PDF today and make your presentation stand out from the rest.
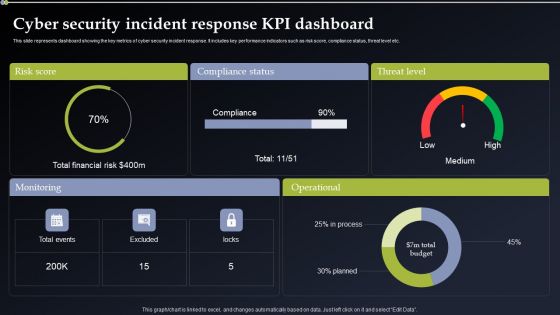
Cyber Security Incident Response KPI Dashboard Pictures PDF
This slide represents dashboard showing the key metrics of cyber security incident response. It includes key performance indicators such as risk score, compliance status, threat level etc. Do you know about Slidesgeeks Cyber Security Incident Response KPI Dashboard Pictures PDF These are perfect for delivering any kind od presentation. Using it, create PowerPoint presentations that communicate your ideas and engage audiences. Save time and effort by using our pre designed presentation templates that are perfect for a wide range of topic. Our vast selection of designs covers a range of styles, from creative to business, and are all highly customizable and easy to edit. Download as a PowerPoint template or use them as Google Slides themes.
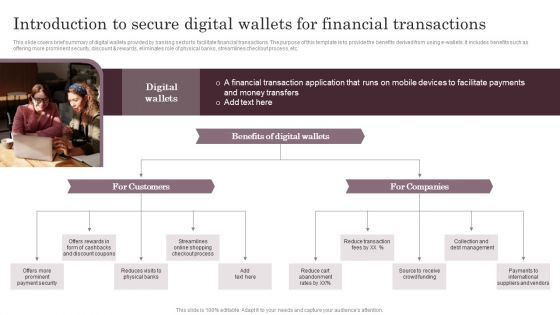
Introduction To Secure Digital Wallets For Financial Transactions Themes PDF
This slide covers brief summary of digital wallets provided by banking sector to facilitate financial transactions. The purpose of this template is to provide the benefits derived from using e-wallets. It includes benefits such as offering more prominent security, discount and rewards, eliminates role of physical banks, streamlines checkout process, etc. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy to edit and customizable templates. Introduction To Secure Digital Wallets For Financial Transactions Themes PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.

IT Simplification Roadmap Ppt PowerPoint Presentation Portfolio Picture
Presenting this set of slides with name it simplification roadmap ppt powerpoint presentation portfolio picture. This is a five stage process. The stages in this process are entrepreneurial approach, perform agile software development and rollouts, secure strong executive support. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Omnichannel Banking Services Platform Techniques To Optimize API Bill Payment Option For Customers Demonstration PDF
This slide covers strategies to improve performance of application programming interface technology. It includes strategies such as reducing payloads, use of faster networks, API caching, advanced security applications along with action steps to be taken and impact of these practices. Present like a pro with Omnichannel Banking Services Platform Techniques To Optimize API Bill Payment Option For Customers Demonstration PDF Create beautiful presentations together with your team, using our easy to use presentation slides. Share your ideas in real time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
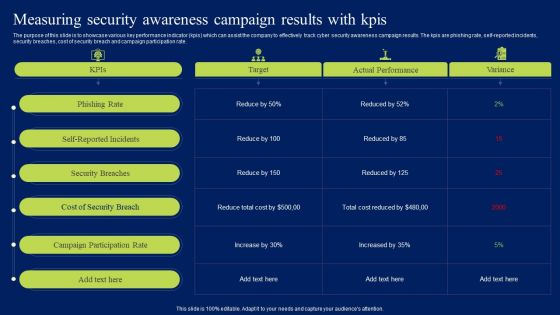
Measuring Security Awareness Campaign Results With Kpis Ppt Summary Sample PDF
The purpose of this slide is to showcase various key performance indicator kpis which can assist the company to effectively track cyber security awareness campaign results. The kpis are phishing rate, self-reported incidents, security breaches, cost of security breach and campaign participation rate. This modern and well-arranged Measuring Security Awareness Campaign Results With Kpis Ppt Summary Sample PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint, no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.
Deploying Cyber Security Incident Response Administration Enterprise Cyber Risk Management Dashboard Icons PDF
This slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Deploying Cyber Security Incident Response Administration Enterprise Cyber Risk Management Dashboard Icons PDF can be your best option for delivering a presentation. Represent everything in detail using Deploying Cyber Security Incident Response Administration Enterprise Cyber Risk Management Dashboard Icons PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.

CYBER Security Breache Response Strategy Enterprise Cyber Risk Management Dashboard Summary PDF
This slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Are you searching for a CYBER Security Breache Response Strategy Enterprise Cyber Risk Management Dashboard Summary PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal. With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download CYBER Security Breache Response Strategy Enterprise Cyber Risk Management Dashboard Summary PDF from Slidegeeks today.

Cloud Access Security Broker Implementation Roadmap Ppt PowerPoint Presentation Diagram Lists PDF
This slide outlines the roadmap for deploying a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to implement the cloud access security broker model. The steps include starting with the most critical cloud application in the portfolio, looking for suitable CASB, etc. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy to edit and customizable templates. Cloud Access Security Broker Implementation Roadmap Ppt PowerPoint Presentation Diagram Lists PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.
Organizing Security Awareness KPI Metrics Dashboard To Effectively Track Cyber Threat Icons PDF
The purpose of this slide is to highlight performance KPI dashboard used to monitor the cyber threat management.. The metrics highlighted in the slide are risk score, compliance status, threat level, monitoring and operational status. This Organizing Security Awareness KPI Metrics Dashboard To Effectively Track Cyber Threat Icons PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Organizing Security Awareness KPI Metrics Dashboard To Effectively Track Cyber Threat Icons PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, dont wait, grab the presentation templates today.
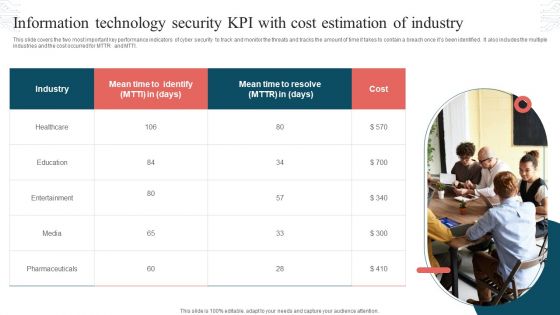
Information Technology Security KPI With Cost Estimation Of Industry Topics PDF
This slide covers the two most important key performance indicators of cyber security to track and monitor the threats and tracks the amount of time it takes to contain a breach once its been identified. It also includes the multiple industries and the cost occurred for MTTR and MTTI. Persuade your audience using this Information Technology Security KPI With Cost Estimation Of Industry Topics PDF. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including Industry, Mean Time, Cost. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Prevention Of Information Cyber Security Awareness Trends In 2023 Infographics PDF
The purpose of this slide is to showcase security awareness trends which the organization has to look out for in 2023. increase in malware and ransomware attack, more employees will be targeted by mobile malware attack and advancement of phishing attack are some of the major trends mentioned in the slide. rom laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Prevention Of Information Cyber Security Awareness Trends In 2023 Infographics PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.
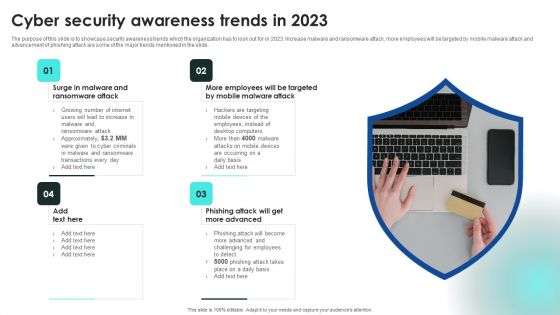
Implementing Cybersecurity Awareness Program To Prevent Attacks Cyber Security Awareness Trends Download PDF
The purpose of this slide is to showcase security awareness trends which the organization has to look out for in 2023. Increase malware and ransomware attack, more employees will be targeted by mobile malware attack and advancement of phishing attack are some of the major trends mentioned in the slide. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy to edit and customizable templates. Implementing Cybersecurity Awareness Program To Prevent Attacks Cyber Security Awareness Trends Download PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.

Incident Response Techniques Deployement Key Lessons Learned By Organization From Cyber Security Incident Formats PDF
This slide represents the key takeaways for the cyber security incident management team after they effectively respond to and manage the cyber attacks experienced by the organization. It includes key lessons learned by organization such as ransomware is here to stay etc. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy to edit and customizable templates. Incident Response Techniques Deployement Key Lessons Learned By Organization From Cyber Security Incident Formats PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.

Kpis To Evaluate Cyber Security Risk Management Ppt PowerPoint Presentation File Outline PDF
The following slide highlights some key performance indicators to measure the impact of cyber security risk administration to assess its effectiveness and take improved decisions. It includes elements such as level of preparedness, mean time to detect, success rating etc. Take your projects to the next level with our ultimate collection of Kpis To Evaluate Cyber Security Risk Management Ppt PowerPoint Presentation File Outline PDF. Slidegeeks has designed a range of layouts that are perfect for representing task or activity duration, keeping track of all your deadlines at a glance. Tailor these designs to your exact needs and give them a truly corporate look with your own brand colors they will make your projects stand out from the rest.

Steps To Deploy Cloud Access Security Broker Ppt PowerPoint Presentation Diagram Images PDF
This slide outlines the steps to implement a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to keep in mind while deploying a CASB model into a business and the steps include the deployment path, deployment model and releasing model. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy to edit and customizable templates. Steps To Deploy Cloud Access Security Broker Ppt PowerPoint Presentation Diagram Images PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.

Organizational Assets Security Management Strategy Evaluating Financial Practices In Firm Formats PDF
The firm can track the financial performance by looking the financial practices it follows in order to avoid any early signs of financial distress. Slidegeeks is here to make your presentations a breeze with Organizational Assets Security Management Strategy Evaluating Financial Practices In Firm Formats PDF With our easy to use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.

Challenges And Solutions For SASE Implementation Ppt Infographics Slideshow PDF
This slide represents the challenges and solutions for implementing a secure access service edge in an organization. The purpose of this slide is to showcase the different challenges that a business can face while deploying the SASE model into a business. The key challenges include networking and security team misalignment, change management, etc. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy to edit and customizable templates. Challenges And Solutions For SASE Implementation Ppt Infographics Slideshow PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.

Functional Testing Checklist To Review Key Components Of Blockchain Application Topics Pdf
The following slide showcases checklist for functional testing to ensure blockchain security. It includes elements such as size of blockchain, addition of blocks, data transmission, API, integration, performance and security testing, etc. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Functional Testing Checklist To Review Key Components Of Blockchain Application Topics Pdf a try. Our experts have put a lot of knowledge and effort into creating this impeccable Functional Testing Checklist To Review Key Components Of Blockchain Application Topics Pdf. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today

Digital Twin Tech IT Application Of Digital Twin In Supply Chain Industry Information PDF
This slide represents the application of digital twin in supply chain management to predict the quality of packaging materials, improve shipment security, warehouse design, and operational performance optimization, and create a logistics system. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Digital Twin Tech IT Application Of Digital Twin In Supply Chain Industry Information PDF for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
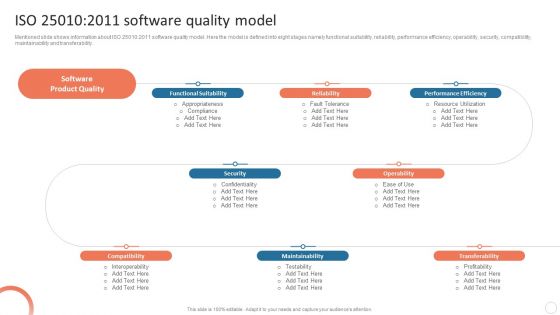
Quality Control Plan Iso 25010 2011 Software Quality Model Template PDF
Mentioned slide shows information about ISO 25010 2011 software quality model. Here the model is defined into eight stages namely functional suitability, reliability, performance efficiency, operability, security, compatibility, maintainability and transferability. Find highly impressive Quality Control Plan Iso 25010 2011 Software Quality Model Template PDF on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Quality Control Plan Iso 25010 2011 Software Quality Model Template PDF for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now.

Deploying AI To Enhance Digital Twin Technology Supply Chain Management Rules PDF
This slide represents the application of digital twin in supply chain management to predict the quality of packaging materials, improve shipment security, warehouse design, and operational performance optimization, and create a logistics system. Find highly impressive Deploying AI To Enhance Digital Twin Technology Supply Chain Management Rules PDF on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Deploying AI To Enhance Digital Twin Technology Supply Chain Management Rules PDF for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now.

Implementing Digital Transformation Global Survey Insights On Digital Transformation Background PDF
Following slide displays key statistics supporting success of digital transformation. It includes survey insights related to performance improvement, business opportunities, data security, evolving technologies, technology investments and procurement. This Implementing Digital Transformation Global Survey Insights On Digital Transformation Background PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Implementing Digital Transformation Global Survey Insights On Digital Transformation Background PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, dont wait, grab the presentation templates today.
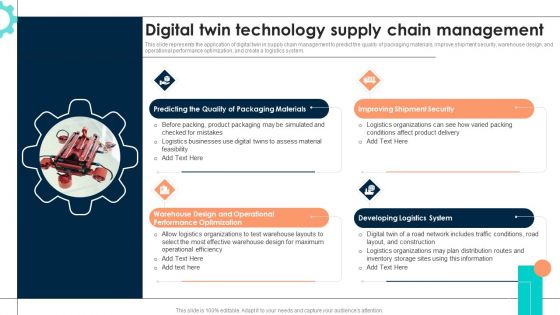
Intelligent Manufacturing Digital Twin Technology Supply Chain Management Rules PDF
This slide represents the application of digital twin in supply chain management to predict the quality of packaging materials, improve shipment security, warehouse design, and operational performance optimization, and create a logistics system. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Intelligent Manufacturing Digital Twin Technology Supply Chain Management Rules PDF can be your best option for delivering a presentation. Represent everything in detail using Intelligent Manufacturing Digital Twin Technology Supply Chain Management Rules PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.
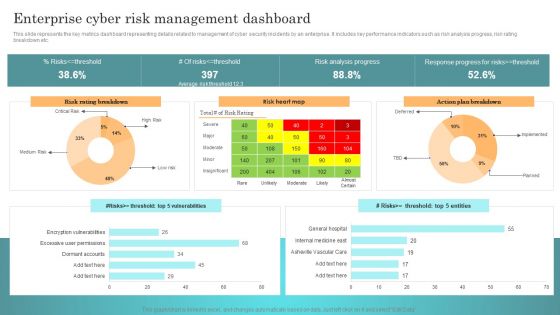
Incident Response Techniques Deployement Enterprise Cyber Risk Management Dashboard Rules PDF
This slide represents the key metrics dashboard representing details related to management of cyber security incidents by an enterprise. It includes key performance indicators such as risk analysis progress, risk rating breakdown etc. Find highly impressive Incident Response Techniques Deployement Enterprise Cyber Risk Management Dashboard Rules PDF on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Incident Response Techniques Deployement Enterprise Cyber Risk Management Dashboard Rules PDF for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now.

Application Of Digital Twin In Supply Chain Industry Ppt PowerPoint Presentation File Infographics PDF
This slide represents the application of digital twin in supply chain management to predict the quality of packaging materials, improve shipment security, warehouse design, and operational performance optimization, and create a logistics system. This Application Of Digital Twin In Supply Chain Industry Ppt PowerPoint Presentation File Infographics PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Application Of Digital Twin In Supply Chain Industry Ppt PowerPoint Presentation File Infographics PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today
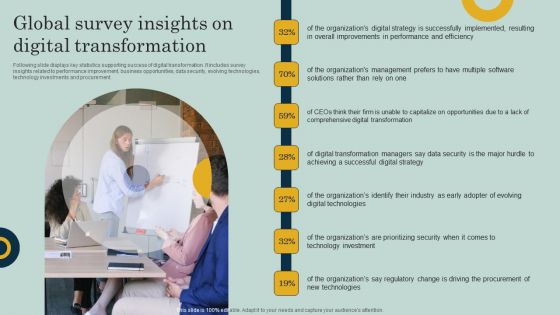
Global Survey Insights On Digital Transformation Ppt Visual Aids Files PDF
Following slide displays key statistics supporting success of digital transformation. It includes survey insights related to performance improvement, business opportunities, data security, evolving technologies, technology investments and procurement. This Global Survey Insights On Digital Transformation Ppt Visual Aids Files PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Global Survey Insights On Digital Transformation Ppt Visual Aids Files PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today
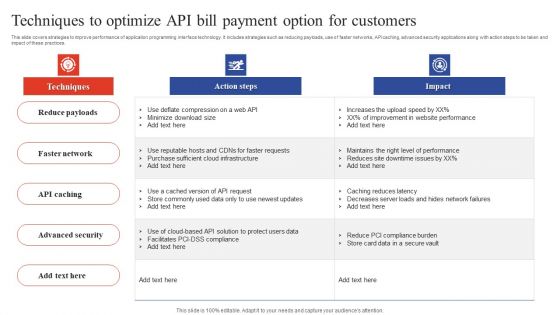
Deployment Of Omnichannel Banking Solutions Techniques To Optimize API Bill Payment Option For Customers Professional PDF
This slide covers strategies to improve performance of application programming interface technology. It includes strategies such as reducing payloads, use of faster networks, API caching, advanced security applications along with action steps to be taken and impact of these practices. Slidegeeks is here to make your presentations a breeze with Deployment Of Omnichannel Banking Solutions Techniques To Optimize API Bill Payment Option For Customers Professional PDF With our easy to use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.

Global Survey Insights On Digital Transformation Ppt Icon Topics PDF
Following slide displays key statistics supporting success of digital transformation. It includes survey insights related to performance improvement, business opportunities, data security, evolving technologies, technology investments and procurement. Welcome to our selection of the Global Survey Insights On Digital Transformation Ppt Icon Topics PDF. These are designed to help you showcase your creativity and bring your sphere to life. Planning and Innovation are essential for any business that is just starting out. This collection contains the designs that you need for your everyday presentations. All of our PowerPoints are 100 percent editable, so you can customize them to suit your needs. This multi purpose template can be used in various situations. Grab these presentation templates today.

Techniques To Optimize API Bill Payment Option For Customers Ppt Infographics Example PDF
This slide covers strategies to improve performance of application programming interface technology. It includes strategies such as reducing payloads, use of faster networks, API caching, advanced security applications along with action steps to be taken and impact of these practices. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Techniques To Optimize API Bill Payment Option For Customers Ppt Infographics Example PDF was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Techniques To Optimize API Bill Payment Option For Customers Ppt Infographics Example PDF.
Omnichannel Strategy Implementation For Banking Solutions Techniques To Optimize API Bill Payment Option Icons PDF
This slide covers strategies to improve performance of application programming interface technology. It includes strategies such as reducing payloads, use of faster networks, API caching, advanced security applications along with action steps to be taken and impact of these practices. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Omnichannel Strategy Implementation For Banking Solutions Techniques To Optimize API Bill Payment Option Icons PDF to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.

Techniques To Optimize API Bill Payment Option For Customers Information PDF
This slide covers strategies to improve performance of application programming interface technology. It includes strategies such as reducing payloads, use of faster networks, API caching, advanced security applications along with action steps to be taken and impact of these practices. The Techniques To Optimize API Bill Payment Option For Customers Information PDF is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.

Digital Twin Technology Supply Chain Management Template PDF
This slide represents the application of digital twin in supply chain management to predict the quality of packaging materials, improve shipment security, warehouse design, and operational performance optimization, and create a logistics system. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download Digital Twin Technology Supply Chain Management Template PDF to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the Digital Twin Technology Supply Chain Management Template PDF.

Transforming Manufacturing With Automation Digital Twin Technology Download PDF
This slide represents the application of digital twin in supply chain management to predict the quality of packaging materials, improve shipment security, warehouse design, and operational performance optimization, and create a logistics system. Crafting an eye catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Transforming Manufacturing With Automation Digital Twin Technology Download PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Transforming Manufacturing With Automation Digital Twin Technology Download PDF that effortlessly grabs the attention of your audience. Begin now and be certain to wow your customers.

Digital Twin Technology Supply Chain Management Designs PDF
This slide represents the application of digital twin in supply chain management to predict the quality of packaging materials, improve shipment security, warehouse design, and operational performance optimization, and create a logistics system. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download Digital Twin Technology Supply Chain Management Designs PDF to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the Digital Twin Technology Supply Chain Management Designs PDF.

Steps For Successful Business Diversification Market Expansion Through Formats Pdf
This slide showcases process that can help organization to formulate business diversification strategy. Its key steps are establish supportive corporate centre, select capable division managers, performance measures, secure competitive advantage, align corporate culture and set incentives. The Steps For Successful Business Diversification Market Expansion Through Formats Pdf is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.

Industrial Transformation Using Digital Twin Application Digital Twin Supply Professional Pdf
This slide represents the application of digital twin in supply chain management to predict the quality of packaging materials, improve shipment security, warehouse design, and operational performance optimization, and create a logistics system. Explore a selection of the finest Industrial Transformation Using Digital Twin Application Digital Twin Supply Professional Pdf here. With a plethora of professionally designed and pre made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Industrial Transformation Using Digital Twin Application Digital Twin Supply Professional Pdf to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.

Steps Successful Business Leveraging Horizontal Vertical Diversification Entering Introduction Pdf
This slide showcases process that can help organization to formulate business diversification strategy. Its key steps are establish supportive corporate centre, select capable division managers, performance measures, secure competitive advantage, align corporate culture and set incentives Present like a pro with Steps Successful Business Leveraging Horizontal Vertical Diversification Entering Introduction Pdf Create beautiful presentations together with your team, using our easy to use presentation slides. Share your ideas in real time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
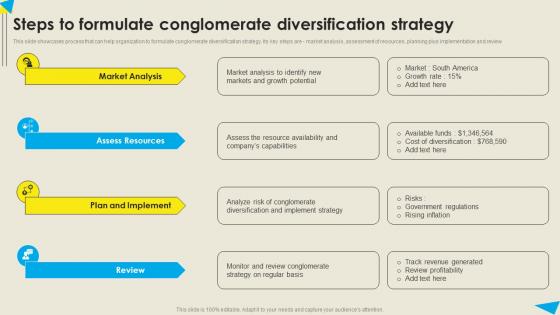
Steps To Formulate Conglomerate Diversification Strategic Diversification Plan Graphics PDF
This slide showcases process that can help organization to formulate business diversification strategy. Its key steps are establish supportive corporate centre, select capable division managers, performance measures, secure competitive advantage, align corporate culture and set incentives. Get a simple yet stunning designed Steps To Formulate Conglomerate Diversification Strategic Diversification Plan Graphics PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Steps To Formulate Conglomerate Diversification Strategic Diversification Plan Graphics PDF can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.
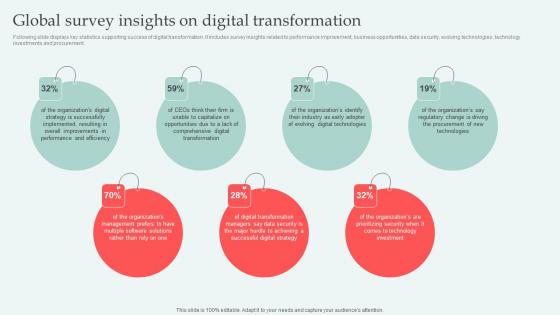
Global Survey Insights Digital Approaches To Increase Business Growth Formats Pdf
Following slide displays key statistics supporting success of digital transformation. It includes survey insights related to performance improvement, business opportunities, data security, evolving technologies, technology investments and procurement. Slidegeeks is here to make your presentations a breeze with Global Survey Insights Digital Approaches To Increase Business Growth Formats Pdf With our easy to use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first
Data Breach Prevention Status Tracking Dashboard Data Breach Prevention Information Pdf
This slide represents the critical cyber security performance indicators for the organization. The key components include application health, encryption status, license consumption, windows defender, etc. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Data Breach Prevention Status Tracking Dashboard Data Breach Prevention Information Pdf template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Data Breach Prevention Status Tracking Dashboard Data Breach Prevention Information Pdf that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers
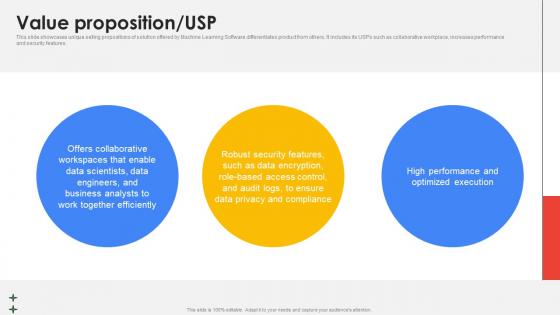
Value Proposition Usp Cloud Platform Provider Investor Funding Elevator Microsoft Pdf
This slide showcases unique selling propositions of solution offered by Machine Learning Software differentiates product from others. It includes its USPs such as collaborative workplace, increases performance and security features. Welcome to our selection of the Value Proposition Usp Cloud Platform Provider Investor Funding Elevator Microsoft Pdf. These are designed to help you showcase your creativity and bring your sphere to life. Planning and Innovation are essential for any business that is just starting out. This collection contains the designs that you need for your everyday presentations. All of our PowerPoints are 100 percent editable, so you can customize them to suit your needs. This multi-purpose template can be used in various situations. Grab these presentation templates today

Web Consulting Business Assessment Of Monthly Actual Spending On Modification
Mentioned slide provides information about actual spending by company on various core areas to enhance business performance and productivity. It includes key areas such as technology advancement, security management, marketing, CRM, and employee management. Present like a pro with Web Consulting Business Assessment Of Monthly Actual Spending On Modification. Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
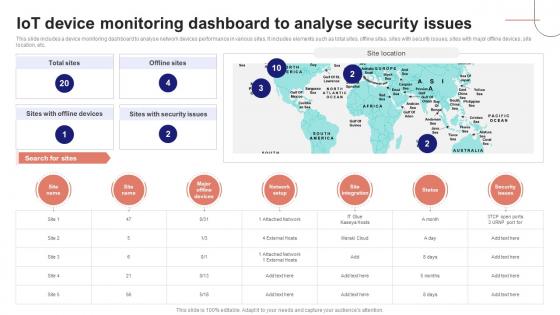
IoT Device Management Fundamentals IoT Device Monitoring Dashboard To Analyse IoT Ss V
This slide includes a device monitoring dashboard to analyse network devices performance in various sites. It includes elements such as total sites, offline sites, sites with security issues, sites with major offline devices, site location, etc. Slidegeeks is here to make your presentations a breeze with IoT Device Management Fundamentals IoT Device Monitoring Dashboard To Analyse IoT SS V With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first

How To Use Big Data To Drive Business Developing Strategic Insights Using Big Data Analytics SS V
This slide showcases various ways business uses big data to make informed business decisions which helps in improving performance and process efficiency. It includes elements such as retention, personalization, data security, asset efficiency, operational risk, innovation prospects etc. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download How To Use Big Data To Drive Business Developing Strategic Insights Using Big Data Analytics SS V to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the How To Use Big Data To Drive Business Developing Strategic Insights Using Big Data Analytics SS V.

Risks Analysis Blind Shipping GTM Strategy GTM SS V
The slide outlines potential challenges and mitigation strategies for drop shipping start-up business, further assisting in their long term operational stability. It highlights components such as performance and security, traffic, supplier frauds, etc.Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Risks Analysis Blind Shipping GTM Strategy GTM SS V to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.
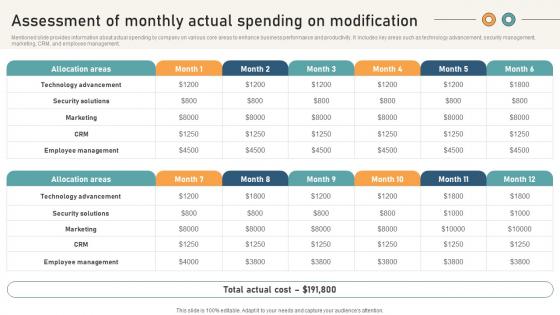
Comprehensive Guide For Website Assessment Of Monthly Actual Spending On Modification
Mentioned slide provides information about actual spending by company on various core areas to enhance business performance and productivity. It includes key areas such as technology advancement, security management, marketing, CRM, and employee management. Get a simple yet stunning designed Comprehensive Guide For Website Assessment Of Monthly Actual Spending On Modification. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Comprehensive Guide For Website Assessment Of Monthly Actual Spending On Modification can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.
Data Breach Prevention Status Tracking Dashboard Data Fortification Strengthening Defenses
This slide represents the critical cyber security performance indicators for the organization. The key components include application health, encryption status, license consumption, windows defender, etc.Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Data Breach Prevention Status Tracking Dashboard Data Fortification Strengthening Defenses and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.

Info Security Elements Of Information Security Application Security Ppt PowerPoint Presentation File Graphics Download PDF
This slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. Deliver and pitch your topic in the best possible manner with this info security elements of information security application security ppt powerpoint presentation file graphics download pdf. Use them to share invaluable insights on application security tools, parameter tampering, encryption and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Global Cyber Terrorism Incidents On The Rise IT Timeline For Implementation Of Cyber Security Download PDF
This slide shows the timeframe for implementing a cyber security model in a business and the monthly activities that must be completed to fight cyber terrorism. Deliver and pitch your topic in the best possible manner with this global cyber terrorism incidents on the rise it timeline for implementation of cyber security download pdf. Use them to share invaluable insights on business, network, perform and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Redundant Array Of Independent Disks Storage IT What Does RAID Not Do Diagrams PDF
This slide defines the tasks and responsibilities that doesnt perform by RAID storage. It also shows how it is failing to provide 100 percent uptime and it doesnt replace backups. Deliver an awe inspiring pitch with this creative redundant array of independent disks storage it what does raid not do diagrams pdf bundle. Topics like virtualization, security, organized, execution can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

IT Project Strategic Plan Roadmap Ideas PDF
This slide signifies the information technology project using strategic plan timeline. It covers information about tasks like installing security software, training, configuring technical control and perform penetration testing with start and end date Showcasing this set of slides titled IT Project Strategic Plan Roadmap Ideas PDF. The topics addressed in these templates are Roadmap, Project, Plan. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
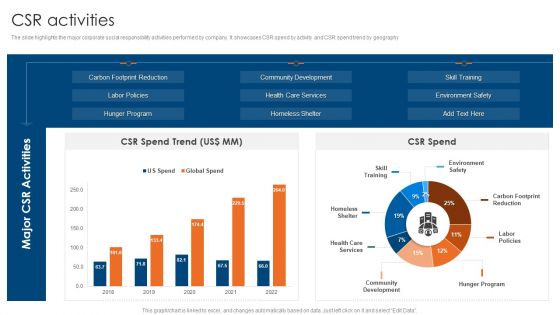
Engineering Consultancy Works Company Profile Csr Activities Demonstration PDF
The slide highlights the major corporate social responsibility activities performed by company. It showcases CSR spend by activity and CSR spend trend by geography. Deliver and pitch your topic in the best possible manner with this Engineering Consultancy Works Company Profile Csr Activities Demonstration PDF. Use them to share invaluable insights on Labor Policies, Environment Safety, Community Development and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
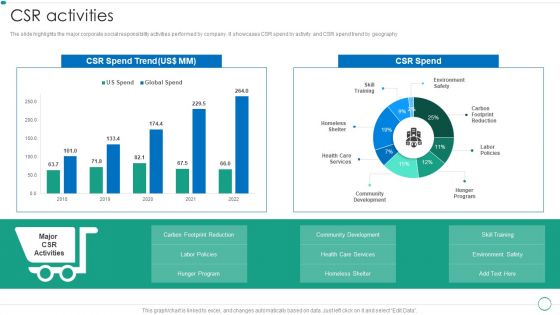
Real Estate Construction And Engineering Company Profile CSR Activities Inspiration PDF
The slide highlights the major corporate social responsibility activities performed by company. It showcases CSR spend by activity and CSR spend trend by geography.Deliver and pitch your topic in the best possible manner with this Real Estate Construction And Engineering Company Profile CSR Activities Inspiration PDF. Use them to share invaluable insights on Spend Trend, Environment Safety, Community Development and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Key In Labyrinth Solution Security PowerPoint Templates Ppt Backgrounds For Slides 1212
We present our Key In Labyrinth Solution Security PowerPoint Templates PPT Backgrounds For Slides 1212.Download and present our Marketing PowerPoint Templates because The marketplace is the merger of your dreams and your ability. Download and present our Business PowerPoint Templates because this template helps you to grab the attention of your listeners. Download our Services PowerPoint Templates because displaying your ideas and highlighting your ability will accelerate the growth of your company and yours. Download and present our puzzles or jigsaws PowerPoint Templates because our templates illustrates your ability. Present our Success PowerPoint Templates because the success of your venture depends on the performance of every team member.Use these PowerPoint slides for presentations relating to Key in the labyrinth security, business, services, marketing, success, puzzles or jigsaws. The prominent colors used in the PowerPoint template are White, Yellow, Black. We assure you our Key In Labyrinth Solution Security PowerPoint Templates PPT Backgrounds For Slides 1212 are Liberated. Customers tell us our marketing PowerPoint templates and PPT Slides will get their audience's attention. You can be sure our Key In Labyrinth Solution Security PowerPoint Templates PPT Backgrounds For Slides 1212 are Vintage. People tell us our services PowerPoint templates and PPT Slides are the best it can get when it comes to presenting. Presenters tell us our Key In Labyrinth Solution Security PowerPoint Templates PPT Backgrounds For Slides 1212 are No-nonsense. People tell us our the PowerPoint templates and PPT Slides are Pretty.
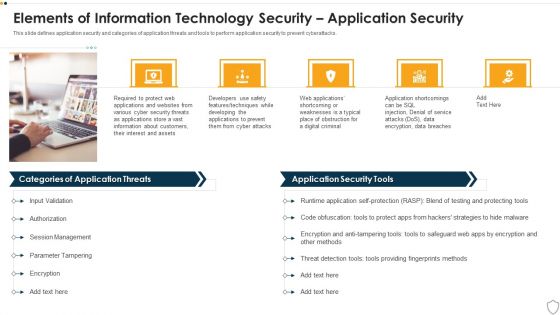
IT Security Elements Of Information Technology Security Application Security Ppt Slide Download PDF
This slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. Presenting it security elements of information technology security application security ppt slide download pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like developing, techniques, service, management. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Us Dollars Chained And Locked Saving PowerPoint Templates Ppt Backgrounds For Slides 1212
We present our US Dollars Chained And Locked Saving PowerPoint Templates PPT Backgrounds For Slides 1212.Present our Money PowerPoint Templates because to achieve sureshot success you need to come together at the right time, place and manner. Download and present our Finance PowerPoint Templates because let this slide illustrates others piggyback on you to see well over the horizon. Use our Security PowerPoint Templates because the gears of youthful minds are useful, therefore set them in motion. Use our Business PowerPoint Templates because project your ideas to you colleagues and complete the full picture. Download and present our Success PowerPoint Templates because the success of your venture depends on the performance of every team member.Use these PowerPoint slides for presentations relating to Us dollars chained and locked, money, finance, security, business, success. The prominent colors used in the PowerPoint template are Yellow, Gray, Black. Customers tell us our US Dollars Chained And Locked Saving PowerPoint Templates PPT Backgrounds For Slides 1212 are Reminiscent. Presenters tell us our security PowerPoint templates and PPT Slides are Perfect. Use our US Dollars Chained And Locked Saving PowerPoint Templates PPT Backgrounds For Slides 1212 are Clever. PowerPoint presentation experts tell us our business PowerPoint templates and PPT Slides are Precious. Customers tell us our US Dollars Chained And Locked Saving PowerPoint Templates PPT Backgrounds For Slides 1212 are Stylish. Presenters tell us our locked PowerPoint templates and PPT Slides are readymade to fit into any presentation structure.
Files Folder And Lifebuoy Computer PowerPoint Templates Ppt Backgrounds For Slides 1212
We present our Files Folder And Lifebuoy Computer PowerPoint Templates PPT Backgrounds For Slides 1212.Present our Computer PowerPoint Templates because the graphic is a symbol of growth and success. Download our Security PowerPoint Templates because you can see In any endeavour people matter most. Present our Inetrnet PowerPoint Templates because you can Signpost your preferred roadmap to your eager co- travellers and demonstrate clearly how you intend to navigate them towards the desired corporate goal. Download our Success PowerPoint Templates because the success of your venture depends on the performance of every team member. Download our Teamwork PowerPoint Templates because the Gear train is a basic element of living and daily business.Use these PowerPoint slides for presentations relating to Computer folders on a lifebuoy, internet, computer, security, success, teamwork. The prominent colors used in the PowerPoint template are Yellow, Red, White. Professionals tell us our Files Folder And Lifebuoy Computer PowerPoint Templates PPT Backgrounds For Slides 1212 are Stunning. Use our on PowerPoint templates and PPT Slides are Zippy. We assure you our Files Folder And Lifebuoy Computer PowerPoint Templates PPT Backgrounds For Slides 1212 are Charming. We assure you our computer PowerPoint templates and PPT Slides are Functional. Presenters tell us our Files Folder And Lifebuoy Computer PowerPoint Templates PPT Backgrounds For Slides 1212 are Ultra. PowerPoint presentation experts tell us our computer PowerPoint templates and PPT Slides are Graceful.

Forex Under Umbrella Business PowerPoint Templates Ppt Backgrounds For Slides 1212
We present our Forex Under Umbrella Business PowerPoint Templates PPT Backgrounds For Slides 1212.Download and present our Security PowerPoint Templates because clarity of thought has been the key to your growth. Download and present our Success PowerPoint Templates because the success of your venture depends on the performance of every team member. Download our Umbrellas PowerPoint Templates because it is all there in bits and pieces. Download our Business PowerPoint Templates because it will demonstrate the strength of character under severe stress. Shine the torch ahead and bring the light to shine on all. Use our Future PowerPoint Templates because let this slide illustrates others piggyback on you to see well over the horizon.Use these PowerPoint slides for presentations relating to Red umbrella, security, future, business, success, umbrellas. The prominent colors used in the PowerPoint template are Red, Green, Black. We assure you our Forex Under Umbrella Business PowerPoint Templates PPT Backgrounds For Slides 1212 are Whimsical. Customers tell us our future PowerPoint templates and PPT Slides provide great value for your money. Be assured of finding the best projection to highlight your words. You can be sure our Forex Under Umbrella Business PowerPoint Templates PPT Backgrounds For Slides 1212 look good visually. People tell us our PowerPoint templates and PPT Slides are Efficacious. Presenters tell us our Forex Under Umbrella Business PowerPoint Templates PPT Backgrounds For Slides 1212 will get their audience's attention. People tell us our future PowerPoint templates and PPT Slides are visually appealing.

Major Types Of Distributed Ledger Security Methods Portrait Pdf
This slide highlights types of blockchain security methods aimed at efficiently storing data to execute transaction and perform functions in an open environment. It covers three types public blockchain, private blockchain and consortium blockchain Showcasing this set of slides titled Major Types Of Distributed Ledger Security Methods Portrait Pdf The topics addressed in these templates are Public Blockchain, Private Blockchain, Consortium Blockchain All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Folder And Alarm Clock Security PowerPoint Templates Ppt Backgrounds For Slides 1212
We present our Folder And Alarm Clock Security PowerPoint Templates PPT Backgrounds For Slides 1212.Download and present our Time Planning PowerPoint Templates because the vision of being the market leader is clear to you. Download our Internet PowerPoint Templates because there are a bucketful of brilliant ideas swirling around within your group. Download our Computer PowerPoint Templates because you can Transmit your thoughts via our slides and proud your team to action. Download and present our Success PowerPoint Templates because the success of your venture depends on the performance of every team member. Present our Business PowerPoint Templates because everybody knows The world over it is a priority for many. Along with it there are so many oppurtunities waiting to be utilised.Use these PowerPoint slides for presentations relating to Alarm clock and folder, business, time planning, internet, computer, success. The prominent colors used in the PowerPoint template are Red, Yellow, White. Professionals tell us our Folder And Alarm Clock Security PowerPoint Templates PPT Backgrounds For Slides 1212 are Stylish. Use our folder PowerPoint templates and PPT Slides are Fantastic. We assure you our Folder And Alarm Clock Security PowerPoint Templates PPT Backgrounds For Slides 1212 are Efficient. We assure you our time PowerPoint templates and PPT Slides will make the presenter look like a pro even if they are not computer savvy. Presenters tell us our Folder And Alarm Clock Security PowerPoint Templates PPT Backgrounds For Slides 1212 are Reminiscent. PowerPoint presentation experts tell us our business PowerPoint templates and PPT Slides are Cheerful.

Best Practices For Secure Web Gateway Implementation Web Threat Protection System
This slide outlines various measures to be taken to maintain and enhance the functionality of Secure Web Gateway. The purpose of this slide is to demonstrate best practices for SWG. These are perform a risk assessment, deploy safe setups, monitor and analyse traffic, etc. There are so many reasons you need a Best Practices For Secure Web Gateway Implementation Web Threat Protection System. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.

Information Security Elements Of Data Security Application Security Ppt Slides Master Slide PDF
This slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. This is a information security elements of data security application security ppt slides master slide pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like required, applications, information, customers, developers. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Internet Security Threats Management Framework Icons PDF
This slide exhibits data breach risk management model. It includes major evaluation criteria such as- does the management has two unique credentials to perform administer activities, does the multifactor authentication is enabled for administrative access etc. Showcasing this set of slides titled internet security threats management framework icons pdf. The topics addressed in these templates are asset, control topic, evaluation questions, response, threat. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
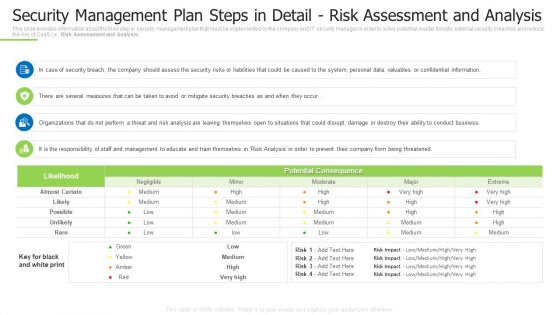
Techniques And Strategies To Reduce Security Management Risks Security Detail Risk Assessment And Analysis Template PDF
This slide provides information about the third step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e., Risk Assessment and Analysis. Deliver and pitch your topic in the best possible manner with this techniques and strategies to reduce security management risks security detail risk assessment and analysis template pdf Use them to share invaluable insights on security breach, perform a threat, several measures and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Elements Of IT Security IT Application Security Ppt Layouts Ideas PDF
This slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. This is a elements of it security it application security ppt layouts ideas pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like management, encryption, authorization, techniques, cyber attacks. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
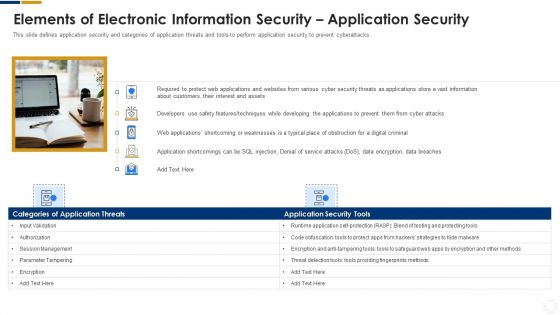
Cybersecurity Elements Of Electronic Information Security Application Security Ppt Styles Graphics PDF
This slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. This is a cybersecurity elements of electronic information security application security ppt styles graphics pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like applications, information, developers, data. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
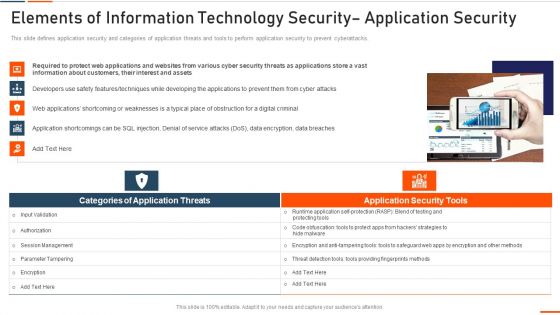
Elements Of Information Technology Security Application Security Ppt Portfolio Inspiration PDF
This slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. Presenting elements of information technology security application security ppt portfolio inspiration pdf to provide visual cues and insights. Share and navigate important information on one stages that need your due attention. This template can be used to pitch topics like required, information, customers, interest, assets. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Information Security Risk Evaluation Process For Information Security Risk Assessment Template PDF
This slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets.This is a Information Security Risk Evaluation Process For Information Security Risk Assessment Template PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Identifying Internal, Allocating Vulnerability, Assessing Level. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
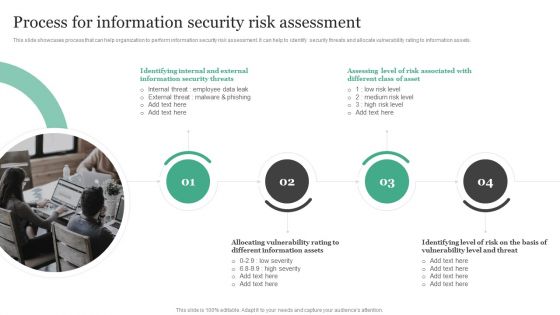
Process For Information Security Risk Assessment Information Security Risk Administration Demonstration PDF
This slide showcases process that can help organization to perform information security risk assessment. It can help to identify security threats and allocate vulnerability rating to information assets.Take your projects to the next level with our ultimate collection of Process For Information Security Risk Assessment Information Security Risk Administration Demonstration PDF. Slidegeeks has designed a range of layouts that are perfect for representing task or activity duration, keeping track of all your deadlines at a glance. Tailor these designs to your exact needs and give them a truly corporate look with your own brand colors they all make your projects stand out from the rest.
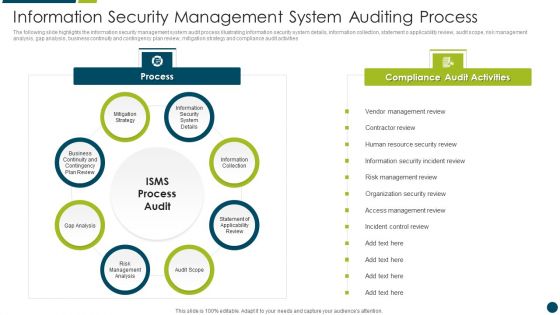
Information Security Management System Auditing Process Microsoft PDF
The following slide highlights the information security management system audit methodology illustrating key headings which includes steps and activities, where steps consists of document review, audit review, plan audit, perform audit and reporting Showcasing this set of slides titled Information Security Management System Auditing Process Microsoft PDF. The topics addressed in these templates are Plan Audit, Reporting, Audit Checklist. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

ERM Plan For Cyber Security Ppt PowerPoint Presentation File Ideas PDF
This slide displays the steps that helps to stay away from the threats of cyber security and makes clients feel safe from the cyber attacks. The steps includes Identifying digital assets, audit data, perform assessments, analyze risk level, establish committee ,etc. Persuade your audience using this ERM Plan For Cyber Security Ppt PowerPoint Presentation File Ideas PDF. This PPT design covers eight stages, thus making it a great tool to use. It also caters to a variety of topics including Establish Risk Assessment Committee, Create Response Plan, Educate Employees On Policies. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
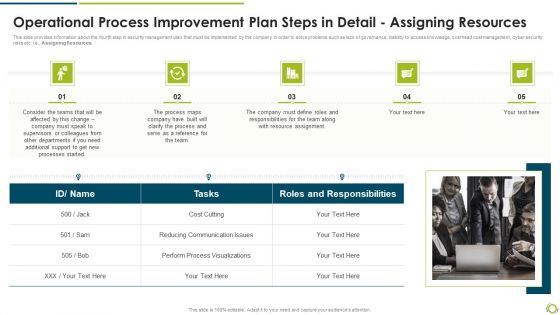
Operational Process Improvement Plan Steps In Detail Assigning Resources Background PDF
This slide provides information about the fourth step in security management plan that must be implemented by the company in order to solve problems such as lack of governance, inability to access knowledge, overhead cost management, cyber security risks etc. i.e. Assigning Resources. Presenting operational process improvement plan steps in detail assigning resources background pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like reducing communication issues, perform process visualizations, roles and responsibilities. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Handling Cyber Threats Digital Era Employee Upskilling Training Program Ppt Professional Master Slide
Mentioned slide displays a five day employee upskilling training program that company will use to provide an in-dept details about information security program activities and deliverables. This is a handling cyber threats digital era employee upskilling training program ppt professional master slide template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like assess security requirements, perform a gap analysis, develop gap initiatives. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
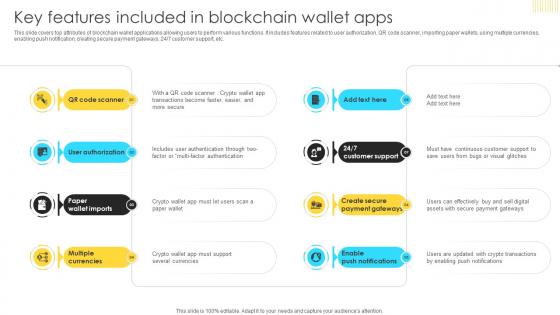
Mastering Blockchain Wallets Key Features Included In Blockchain Wallet Apps BCT SS V
This slide covers top attributes of blockchain wallet applications allowing users to perform various functions. It includes features related to user authorization, QR code scanner, importing paper wallets, using multiple currencies, enabling push notification, creating secure payment gateways, 24 or 7 customer support, etc. There are so many reasons you need a Mastering Blockchain Wallets Key Features Included In Blockchain Wallet Apps BCT SS V. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
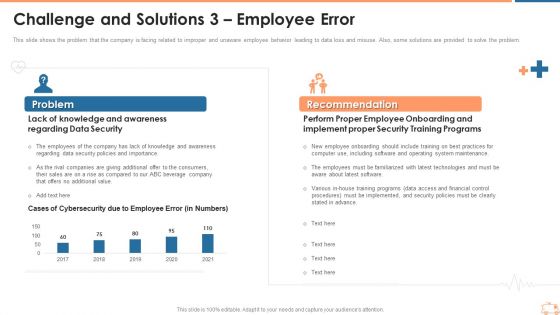
Challenge And Solutions 3 Employee Error Ppt Portfolio Good PDF
This slide shows the problem that the company is facing related to improper and unaware employee behavior leading to data loss and misuse. Also, some solutions are provided to solve the problem. Deliver an awe inspiring pitch with this creative challenge and solutions 3 employee error ppt portfolio good pdf bundle. Topics like problem, recommendation, perform proper employee onboarding and implement proper security training programs can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Data Interpretation And Analysis Playbook Business Intelligence And Predictive Analytics Challenges Template PDF
This template covers the problems while implementing BI and predictive analytics in the organization. The challenges are undefined KPIs and metrics, and unable to hire right data science talent. Presenting data interpretation and analysis playbook business intelligence and predictive analytics challenges template pdf to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like security vulnerabilities, operationalizing, perform analysis, deployed. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Data Lake Architecture How To Decide If You Need A Data Lake Information PDF
This slide depicts the key pointers to help to understand organizations if they need to maintain a data lake for critical business information and perform analytics on that data. Deliver an awe inspiring pitch with this creative Data Lake Architecture How To Decide If You Need A Data Lake Information PDF bundle. Topics like Make Data Administration Easier, Accelerate Analytics, Enhance Security And Governance, Businesses Depend can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Data Migration Project Process With Estimated Time And Cost Demonstration PDF
This slow showcases process that can help organization to formulate the migration project design and perform data security checks. Its key steps are planning, data preparation, migration design, testing and go live. Pitch your topic with ease and precision using this Data Migration Project Process With Estimated Time And Cost Demonstration PDF. This layout presents information on Planning, Data Preparation, Migration Design. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
Information Visualizations Playbook Business Intelligence And Predictive Analytics Challenges Icons PDF
This template covers the problems while implementing BI and predictive analytics in the organization. The challenges are undefined KPIs and metrics, and unable to hire right data science talent. Presenting Information Visualizations Playbook Business Intelligence And Predictive Analytics Challenges Icons PDF to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like Raw Data Organized, Security Vulnerabilities, Perform Analysis. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
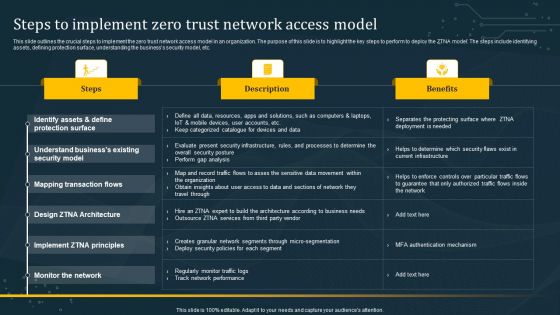
Steps To Implement Zero Trust Network Access Model Graphics PDF
This slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. If your project calls for a presentation, then Slidegeeks is your go-to partner because we have professionally designed, easy-to-edit templates that are perfect for any presentation. After downloading, you can easily edit Steps To Implement Zero Trust Network Access Model Graphics PDF and make the changes accordingly. You can rearrange slides or fill them with different images. Check out all the handy templates
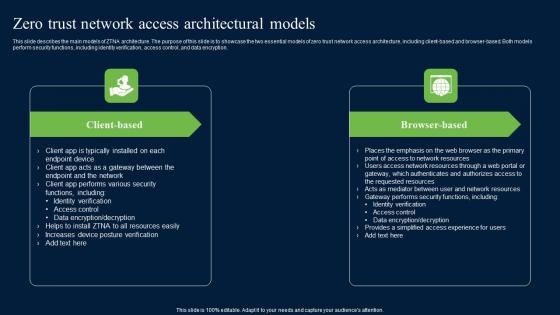
Zero Trust Network Access Architectural Models Ideas Pdf
This slide describes the main models of ZTNA architecture. The purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client-based and browser-based. Both models perform security functions, including identity verification, access control, and data encryption. There are so many reasons you need a Zero Trust Network Access Architectural Models Ideas Pdf. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.

Shim Rune Workflow In Inclavare Containers Secure Multi Party Ideas Pdf
This slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Shim Rune Workflow In Inclavare Containers Secure Multi Party Ideas Pdf can be your best option for delivering a presentation. Represent everything in detail using Shim Rune Workflow In Inclavare Containers Secure Multi Party Ideas Pdf and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.
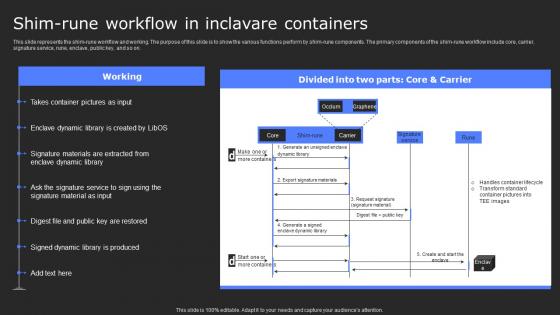
Shim Rune Workflow In Inclavare Containers Secure Computing Framework Infographics Pdf
This slide represents the shim-rune workflow and working. The purpose of this slide is to show the various functions perform by shim-rune components. The primary components of the shim-rune workflow include core, carrier, signature service, rune, enclave, public key, and so on. Create an editable Shim Rune Workflow In Inclavare Containers Secure Computing Framework Infographics Pdf that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Shim Rune Workflow In Inclavare Containers Secure Computing Framework Infographics Pdf is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.

Ppt Sequential Way To Prevent Business Losses Three Steps PowerPoint Templates
PPT sequential way to prevent business losses three steps PowerPoint Templates-Use this Arrow based PowerPoint Diagram to elaborate three interconnected issues which performs their actions in cycle. This diagram provides an overview of the interactions of different factors in a company.-PPT sequential way to prevent business losses three steps PowerPoint Templates-Asset, Bank, Banking, Business, Care, Careful, Cash, Commerce, Concept, Crime, Criminal, Currency, Defend, Deposit, Economic, Economy, , Finance, , Financial, Frugal, Future, Goal, Hold, Hope, Identity, Invest, Investment, Keep, Lock, Lockdown, Loss, Market, Money, Optimism, Opulence, Opulent, Planning, Possibility, Precious, Prevention, Profit, Prosperity, Protect, Protection, Reserve, Robbery, Safe, Safety, Save, Saving, Secure, Security, Shelter, Speculate, Tax

Business Arrows PowerPoint Templates Business Data Mining Process Ppt Slides
Business Arrows PowerPoint Templates Business data mining process PPT Slides-Use this diagram to show Data Mining Process as a mechanism or group of parts performing one function or serving one purpose in a complex situation-Business Arrows PowerPoint Templates Business data mining process PPT Slides-This template can be used for presentations relating to Analysis, Anomaly, Artificial, Break, Clean, Computer, Cut, Data, Database, Decision, Detection, Discovery, Divide, Explore, Extract, Hammer, Helmet, Human, Index, Intelligence, Kdd, knowledge, Learning, Light, Mallet, Management, Mining, Model, Movement, Pattern, Predictive, Process, Records, Recycle, Repair, Safety, Science

Healthcare Financial Stabilization And Sustainability Provider Ppt Professional Slide Download PDF
This slide covers the actions performed to stabilize cash expenditures and review labor strategies which focuses on market actions, assets and capabilities, technology enablers and other considerations. Deliver and pitch your topic in the best possible manner with this healthcare financial stabilization and sustainability provider ppt professional slide download pdf. Use them to share invaluable insights on focus immediate cash flow and liquidity, capture charges for new services, assets, and locations, safety, and expense and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Earth On A Lifeline Security Concept PowerPoint Templates Ppt Backgrounds For Slides 1212
We present our Earth On A Lifeline Security Concept PowerPoint Templates PPT Backgrounds For Slides 1212.Download and present our Security PowerPoint Templates because with the help of our Slides you can Illustrate these thoughts with this slide. Download our Global PowerPoint Templates because with the help of our Slides you can Illustrate your plans on using the many social media modes available to inform soceity at large of the benefits of your product. Present our Nature PowerPoint Templates because you can put it up there for all to see. Use our environment PowerPoint Templates because The atmosphere is full of newfound enthusiasm and energy. Everyone around is buzzing with interesting ideas. Be the spark that lights up the fuse. Be the catalyst that galvanises everyone to action. Download and present our Success PowerPoint Templates because the success of your venture depends on the performance of every team member.Use these PowerPoint slides for presentations relating to Life buoy and earth globe , global, security, nature, environment, success. The prominent colors used in the PowerPoint template are Red, Blue, White. Professionals tell us our Earth On A Lifeline Security Concept PowerPoint Templates PPT Backgrounds For Slides 1212 are Sparkling. Use our earth PowerPoint templates and PPT Slides are One-of-a-kind. We assure you our Earth On A Lifeline Security Concept PowerPoint Templates PPT Backgrounds For Slides 1212 are designed to make your presentations professional. We assure you our earth PowerPoint templates and PPT Slides are effectively colour coded to prioritise your plans They automatically highlight the sequence of events you desire. Presenters tell us our Earth On A Lifeline Security Concept PowerPoint Templates PPT Backgrounds For Slides 1212 are Royal. PowerPoint presentation experts tell us our environment PowerPoint templates and PPT Slides are Pretty.

Success Key Business PowerPoint Templates Ppt Backgrounds For Slides 1212
We present our Success key Business PowerPoint Templates PPT Backgrounds For Slides 1212.Present our Business PowerPoint Templates because The foundation of the structure of your business is resilient and dependable. Convey this confidence to your colleagues and assure them of a great and enduring future. Download and present our Success PowerPoint Templates because the success of your venture depends on the performance of every team member. Use our Future PowerPoint Templates because Our PowerPoint Templates and Slides will give you great value for your money. Be assured of finding the best projection to highlight your words. Use our Steps PowerPoint Templates because it expound on why you have discarded some plans as you went along to the apex and came out with the final selection which you know will make you and your team shine. Download and present our Security PowerPoint Templates because let your words be the drops of wisdom spreading knowledge and peace like ripples through the expectant minds of your devoted followers.Use these PowerPoint slides for presentations relating to Key to success business, success, business, future, steps, security. The prominent colors used in the PowerPoint template are Yellow, White, Gray. We assure you our Success key Business PowerPoint Templates PPT Backgrounds For Slides 1212 are Quaint. Customers tell us our success PowerPoint templates and PPT Slides are Playful. Customers tell us our Success key Business PowerPoint Templates PPT Backgrounds For Slides 1212 are Striking. The feedback we get is that our security PowerPoint templates and PPT Slides are Handsome. PowerPoint presentation experts tell us our Success key Business PowerPoint Templates PPT Backgrounds For Slides 1212 are Great. PowerPoint presentation experts tell us our security PowerPoint templates and PPT Slides are Luxurious.

3d Men With Red House Key Real Estate PowerPoint Templates Ppt Backgrounds For Slides 1212
We present our 3d Men With Red House Key Real Estate PowerPoint Templates PPT Backgrounds For Slides 1212.Present our Future PowerPoint Templates because you can illustrate your ideas and imprint them in the minds of your team with this template. Download and present our People PowerPoint Templates because this slide imprint them on the minds of your audience via our slides. Use our Security PowerPoint Templates because you should go for Gold and not just silver. Present our Success PowerPoint Templates because the success of your venture depends on the performance of every team member. Present our Family PowerPoint Templates because grapes are the source of some of the sweetest of wines.Use these PowerPoint slides for presentations relating to Business man with house or home key, people, future, security, success, family. The prominent colors used in the PowerPoint template are Gray, White, Red. Customers tell us our 3d Men With Red House Key Real Estate PowerPoint Templates PPT Backgrounds For Slides 1212 are Gorgeous. Presenters tell us our people PowerPoint templates and PPT Slides are Reminiscent. Use our 3d Men With Red House Key Real Estate PowerPoint Templates PPT Backgrounds For Slides 1212 are Lush. PowerPoint presentation experts tell us our future PowerPoint templates and PPT Slides provide you with a vast range of viable options. Select the appropriate ones and just fill in your text. Customers tell us our 3d Men With Red House Key Real Estate PowerPoint Templates PPT Backgrounds For Slides 1212 are Liberated. Presenters tell us our house PowerPoint templates and PPT Slides are Zippy.
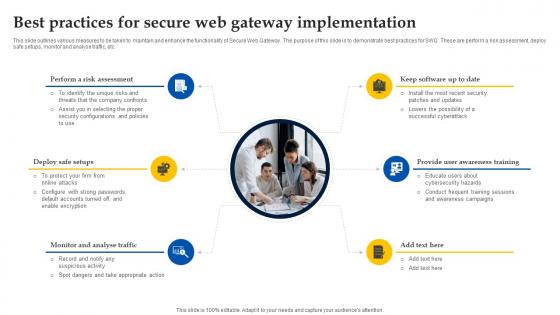
Web Access Control Solution Best Practices For Secure Web Gateway Implementation
This slide outlines various measures to be taken to maintain and enhance the functionality of Secure Web Gateway. The purpose of this slide is to demonstrate best practices for SWG. These are perform a risk assessment, deploy safe setups, monitor and analyse traffic, etc. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Web Access Control Solution Best Practices For Secure Web Gateway Implementation can be your best option for delivering a presentation. Represent everything in detail using Web Access Control Solution Best Practices For Secure Web Gateway Implementation and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.

Yellow Computer Folder With-key Internet PowerPoint Templates And PowerPoint Themes 1112
We present our Yellow Computer Folder With-Key Internet PowerPoint Templates And PowerPoint Themes 1112.Use our Computer PowerPoint Templates because, Different people with differing ideas and priorities perform together to score. Use our Internet PowerPoint Templates because, Our template will help pinpoint their viability. Use our Communication PowerPoint Templates because, Use our creative template to lay down your views. Use our Security PowerPoint Templates because, Gears Interconnected:- The Gear Train is a basic element of living and daily business. Use our Symbol PowerPoint Templates because,Use our templates for your colleagues knowledge to feed.Use these PowerPoint slides for presentations relating to Yellow computer folder with key Internet Security Computer Symbol Communication. The prominent colors used in the PowerPoint template are Yellow, White, Brown
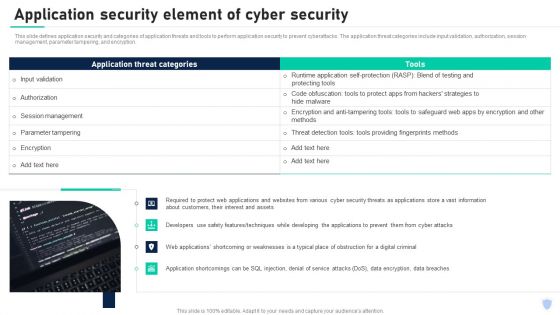
Cyber Security Components To Enhance Processes Application Security Element Of Cyber Security Infographics PDF
This slide defines application security and categories of application threats and tools to perform application security to prevent cyberattacks. The application threat categories include input validation, authorization, session management, parameter tampering, and encryption. Boost your pitch with our creative Cyber Security Components To Enhance Processes Career Opportunities In Cybersecurity Profession Sample PDF. Deliver an awe inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.
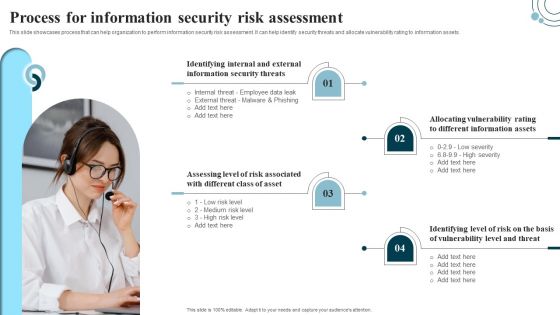
Developing IT Security Strategy Process For Information Security Risk Assessment Graphics PDF
This slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Developing IT Security Strategy Process For Information Security Risk Assessment Graphics PDF was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Developing IT Security Strategy Process For Information Security Risk Assessment Graphics PDF.

Information Systems Security And Risk Management Plan Process For Information Security Risk Assessment Formats PDF
This slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets. This modern and well arranged Information Systems Security And Risk Management Plan Process For Information Security Risk Assessment Formats PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.

Process For Information Security Risk Assessment Cybersecurity Risk Assessment Portrait PDF
This slide showcases process that can help organization to perform information security risk assessment. It can help identify security threats and allocate vulnerability rating to information assets. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Process For Information Security Risk Assessment Cybersecurity Risk Assessment Portrait PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Process For Information Security Risk Assessment Cybersecurity Risk Assessment Portrait PDF today and make your presentation stand out from the rest.

Steps To Implement Zero Trust Network Access Model Zero Trust Network Security Inspiration Pdf
This slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. Get a simple yet stunning designed Steps To Implement Zero Trust Network Access Model Zero Trust Network Security Inspiration Pdf. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Steps To Implement Zero Trust Network Access Model Zero Trust Network Security Inspiration Pdf can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.

Timeline For The Implementation Of IT Security IT Ppt Inspiration Portrait PDF
This slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Deliver an awe inspiring pitch with this creative timeline for the implementation of it security it ppt inspiration portrait pdf bundle. Topics like network, internal security, perform, phishing exercise can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Developing Firm Security Strategy Plan Role Of Management In Effective Corporate Security Governance Slides PDF
This slide portrays information regarding the responsibilities that are to be performed by board of directors, senior executives, steering committees and chief security office in order to ensure the effective corporate security governance. Deliver an awe inspiring pitch with this creative developing firm security strategy plan role of management in effective corporate security governance slides pdf bundle. Topics like strategic alignment, risk management, measuring performance, value delivery, managing resource can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
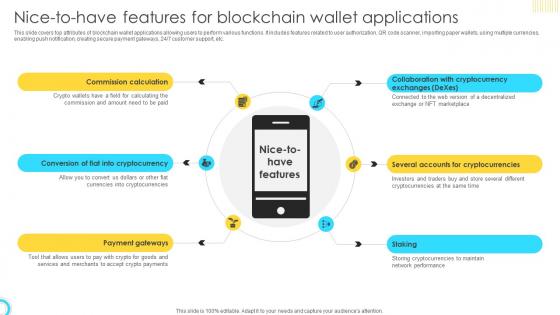
Mastering Blockchain Wallets Nice To Have Features For Blockchain Wallet BCT SS V
This slide covers top attributes of blockchain wallet applications allowing users to perform various functions. It includes features related to user authorization, QR code scanner, importing paper wallets, using multiple currencies, enabling push notification, creating secure payment gateways, 24 or 7 customer support, etc. Present like a pro with Mastering Blockchain Wallets Nice To Have Features For Blockchain Wallet BCT SS V. Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.

Roles And Responsibilities Of Cloud Team In Project Administration Ppt Pictures Guide PDF
The purpose of this slide is to provide information about key roles of cloud team in project management. Project manager, cloud architect, engineer, security and compliance specialist are some of the key members of cloud team structure who have to perform various roles for successful project management. Persuade your audience using this Roles And Responsibilities Of Cloud Team In Project Administration Ppt Pictures Guide PDF. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including Project Manager, Cloud Architect, Cloud Engineer. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
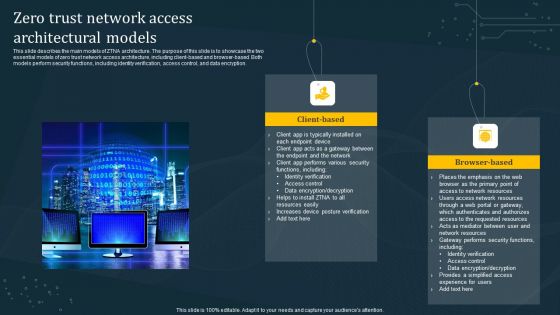
Zero Trust Network Access Architectural Models Diagrams PDF
This slide describes the main models of ZTNA architecture. The purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client-based and browser-based. Both models perform security functions, including identity verification, access control, and data encryption. Are you searching for a Zero Trust Network Access Architectural Models Diagrams PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Zero Trust Network Access Architectural Models Diagrams PDF from Slidegeeks today.

Zero Trust Model Steps To Implement Zero Trust Network Access Model
This slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. Slidegeeks is here to make your presentations a breeze with Zero Trust Model Steps To Implement Zero Trust Network Access Model With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first
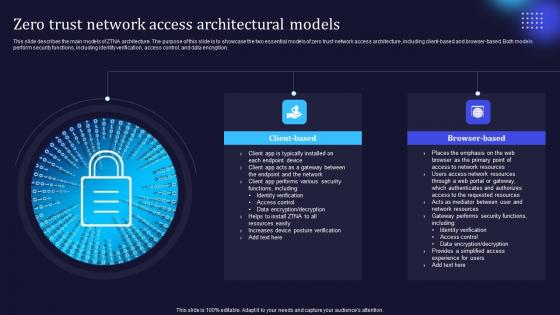
Zero Trust Model Zero Trust Network Access Architectural Models
This slide describes the main models of ZTNA architecture. The purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client-based and browser-based. Both models perform security functions, including identity verification, access control, and data encryption. This Zero Trust Model Zero Trust Network Access Architectural Models is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Zero Trust Model Zero Trust Network Access Architectural Models features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today

Zero Trust Network Access Architectural Models Software Defined Perimeter SDP
This slide describes the main models of ZTNA architecture. The purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client-based and browser-based. Both models perform security functions, including identity verification, access control, and data encryption. This Zero Trust Network Access Architectural Models Software Defined Perimeter SDP is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Zero Trust Network Access Architectural Models Software Defined Perimeter SDP features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today
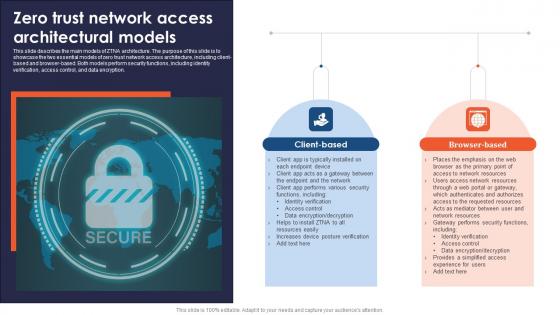
A48 Zero Trust Network Access Architectural Models
This slide describes the main models of ZTNA architecture. The purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client-based and browser-based. Both models perform security functions, including identity verification, access control, and data encryption. Boost your pitch with our creative A48 Zero Trust Network Access Architectural Models. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.

Zero Trust Network Access Steps To Implement Zero Trust Network Access Model
This slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Zero Trust Network Access Steps To Implement Zero Trust Network Access Model template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Zero Trust Network Access Steps To Implement Zero Trust Network Access Model that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers
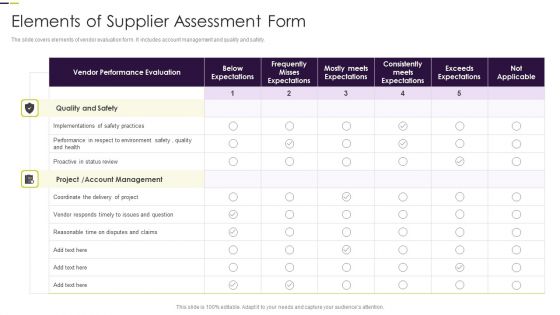
Elements Of Supplier Assessment Form Slides PDF
The slide covers elements of vendor evaluation form. It includes account management and quality and safety.Pitch your topic with ease and precision using this Elements Of Supplier Assessment Form Slides PDF. This layout presents information on Vendor Performance, Below Expectations, Misses Expectations. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Checklist To Conduct Tokenization In Data Security PPT Presentation
This slide showcases the checklist for performing tokenization. The purpose of this slide is to highlight the actions performed while conducting regression testing, person responsible, status and comments for the same. Boost your pitch with our creative Checklist To Conduct Tokenization In Data Security PPT Presentation. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.

30 60 90 Days Plan To Implement Cloud Security In Business Cloud Computing Security IT Ppt Gallery Master Slide PDF
This slide defines the 30,60 and 90 days plan to implement cloud security in the organization and what tasks would be performed on each 30 days interval. This is a 30 60 90 days plan to implement cloud security in business cloud computing security it ppt gallery master slide pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like performed, analyze, cloud services, data access policies. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
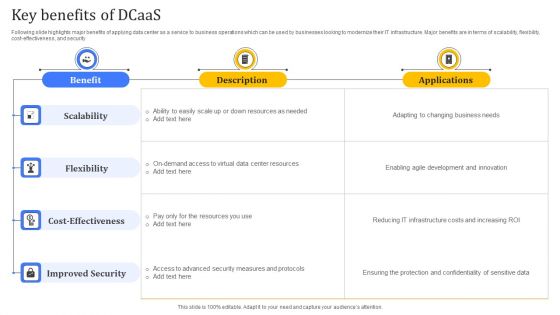
Key Benefits Of Dcaas Diagrams PDF
This slide depicts a dashboard which can be used to monitor the key performing indicators related to data center as a service model. The key performing indicators are items by status, counts by model attributes, item count by customer type, physical vs virtual system Showcasing this set of slides titled Key Benefits Of Dcaas Diagrams PDF. The topics addressed in these templates are Scalability, Flexibility, Cost Effectiveness, Improved Security. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Scrum Crystal And Extreme Programming Procedure Key Principles Of The Crystal Agile Framework Sample PDF
This slide provides the glimpse about the key principles of crystal agile framework which focuses on frequent delivery, reflective improvement, osmotic communication, personal safety, focus on work, access to experts and users and technical tooling. This is a scrum crystal and extreme programming procedure key principles of the crystal agile framework sample pdf template with various stages. Focus and dispense information on seven stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like performance, important, improved, communication, documentation. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Effective Company Event Communication Plan Types Of Risks Associated With Upcoming Event Template PDF
This slide covers various kinds of risks that can take place at upcoming events. It includes risk categories such as safety, weather, external forces, staffing, event site, ethics, and images. This is a Effective Company Event Communication Plan Types Of Risks Associated With Upcoming Event Template PDF template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Ethical Performance, Social Responsibility, Issues Grievances You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
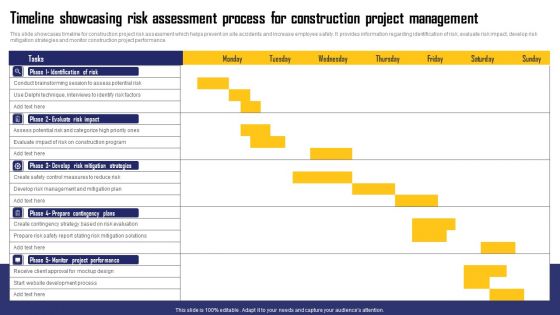
Timeline Showcasing Risk Assessment Process For Construction Project Management Rules PDF
This slide showcases timeline for construction project risk assessment which helps prevent on site accidents and increase employee safety. It provides information regarding identification of risk, evaluate risk impact, develop risk mitigation strategies and monitor construction project performance. Pitch your topic with ease and precision using this Timeline Showcasing Risk Assessment Process For Construction Project Management Rules PDF. This layout presents information on Identification Of Risk, Evaluate Risk Impact, Develop Risk Mitigation Strategies. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Checklist To Conduct Tokenization In Data Security Securing Your Data Ppt Example
This slide showcases the checklist for performing tokenization. The purpose of this slide is to highlight the actions performed while conducting regression testing, person responsible, status and comments for the same. Present like a pro with Checklist To Conduct Tokenization In Data Security Securing Your Data Ppt Example Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
PowerPoint Theme Flow Diverging Arrow Process Diagram Ppt Cycle Spoke Network Slides
We present our powerpoint theme flow diverging arrow process diagram ppt Cycle Spoke Network Slides.Use our Process and Flows PowerPoint Templates because it helps you to display your ideas and thoughts. Download and present our Business PowerPoint Templates because you have secured a name for yourself in the domestic market. Now the time is right to spread your reach to other countries. Download our Shapes PowerPoint Templates because this is a wonderful graphics to see the smiles of happiness spread as your audience realizes the value of your words. Use our Success PowerPoint Templates because different people with differing ideas and priorities perform together to score. Download our Flow Charts PowerPoint Templates because different personalities, different abilities but formidable together.Use these PowerPoint slides for presentations relating to Arrows, Business, Central, Centralized, Chart, Circle, Circular, Circulation, Concept, Conceptual, Illustration, Organization, Pointing, Process, Radial, Resource, Strategy, Template, Graphic, Group, Illustration, Process, Progress. The prominent colors used in the PowerPoint template are Red, Gray, White. People tell us our powerpoint theme flow diverging arrow process diagram ppt Cycle Spoke Network Slides are incredible easy to use. Professionals tell us our Concept PowerPoint templates and PPT Slides are Second to none. Customers tell us our powerpoint theme flow diverging arrow process diagram ppt Cycle Spoke Network Slides are Wistful. Use our Chart PowerPoint templates and PPT Slides are Spiffy. We assure you our powerpoint theme flow diverging arrow process diagram ppt Cycle Spoke Network Slides are Cheerful. Professionals tell us our Central PowerPoint templates and PPT Slides are Efficient.
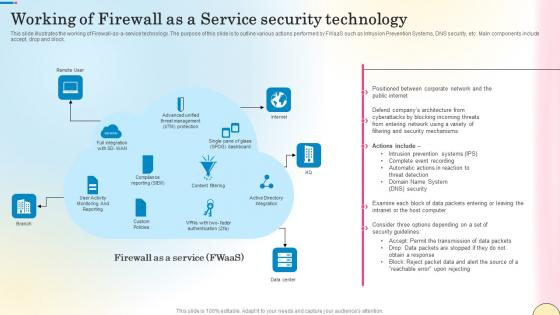
Working Of Firewall As A Service Security Technology Network Security Guidelines Pdf
This slide illustrates the working of Firewall-as-a-service technology. The purpose of this slide is to outline various actions performed by FWaaS such as Intrusion Prevention Systems, DNS security, etc. Main components include accept, drop and block. Find highly impressive Working Of Firewall As A Service Security Technology Network Security Guidelines Pdf on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Working Of Firewall As A Service Security Technology Network Security Guidelines Pdf for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now
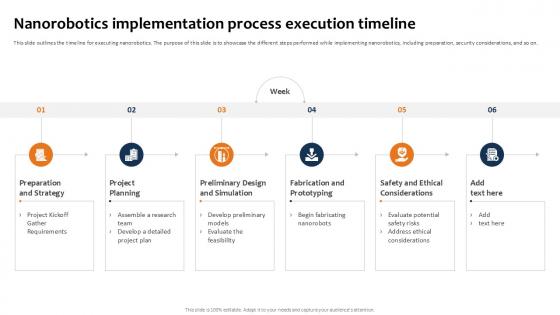
Nanorobotics Implementation Building The Future Of Robotic Ppt Slide
This slide outlines the timeline for executing nanorobotics. The purpose of this slide is to showcase the different steps performed while implementing nanorobotics, including preparation, security considerations, and so on.The Nanorobotics Implementation Building The Future Of Robotic Ppt Slide is a compilation of the most recent design trends as a series of slides. It is suitable for any subject or industry presentation, containing attractive visuals and photo spots for businesses to clearly express their messages. This template contains a variety of slides for the user to input data, such as structures to contrast two elements, bullet points, and slides for written information. Slidegeeks is prepared to create an impression.
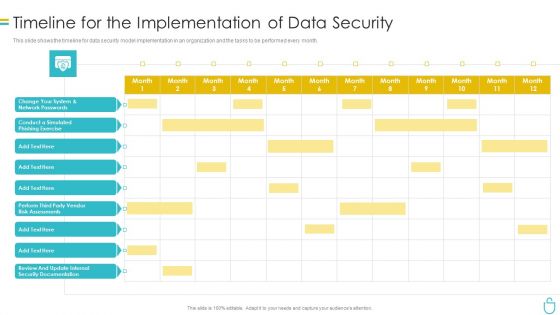
Information Security Timeline For The Implementation Of Data Security Ppt Gallery Topics PDF
This slide shows the timeline for data security model implementation in an organization and the tasks to be performed every month. Deliver and pitch your topic in the best possible manner with this information security timeline for the implementation of data security ppt gallery topics pdf. Use them to share invaluable insights on timeline for the implementation of data security and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
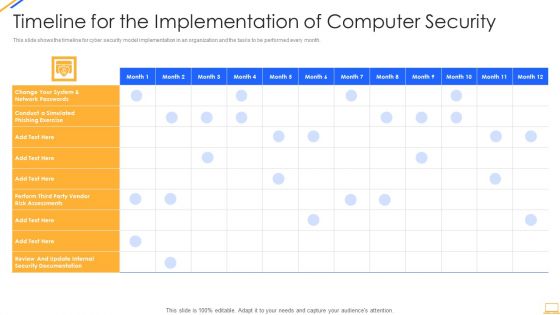
Desktop Security Management Timeline For The Implementation Of Computer Security Sample PDF
This slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Deliver and pitch your topic in the best possible manner with this desktop security management timeline for the implementation of computer security sample pdf. Use them to share invaluable insights on security documentation, system and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
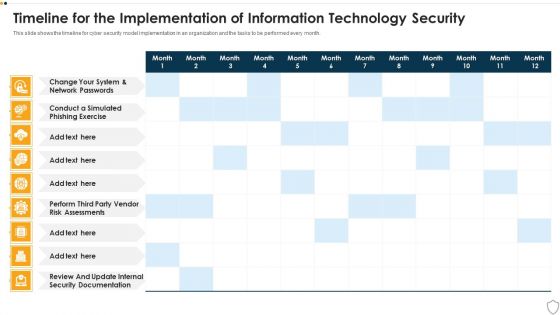
IT Security Timeline For The Implementation Of Information Technology Security Structure PDF
This slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Deliver an awe inspiring pitch with this creative it security timeline for the implementation of information technology security structure pdf bundle. Topics like timeline for the implementation of information technology security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
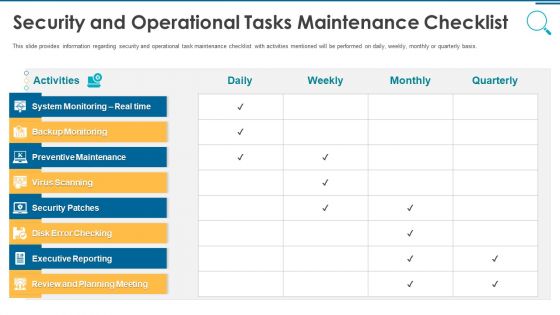
Information And Technology Security Operations Security And Operational Tasks Maintenance Checklist Pictures PDF
This slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Deliver and pitch your topic in the best possible manner with this information and technology security operations security and operational tasks maintenance checklist pictures pdf. Use them to share invaluable insights on system monitoring, executive reporting, planning meeting, preventive maintenance and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
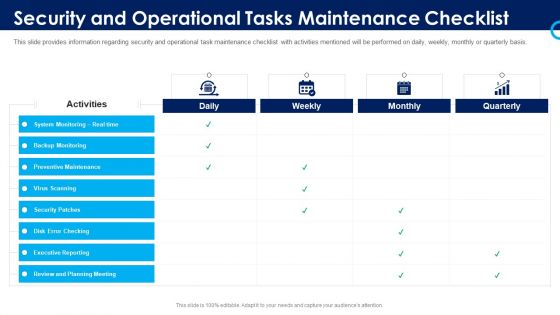
Organizational Security Solutions Security And Operational Tasks Maintenance Checklist Pictures PDF
This slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Deliver and pitch your topic in the best possible manner with this organizational security solutions security and operational tasks maintenance checklist pictures pdf. Use them to share invaluable insights on system monitoring, executive reporting, planning meeting, preventive maintenance and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Security Functioning Centre Security And Operational Tasks Maintenance Checklist Inspiration PDF
This slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Deliver and pitch your topic in the best possible manner with this security functioning centre security and operational tasks maintenance checklist inspiration pdf. Use them to share invaluable insights on executive reporting, review and planning meeting, system monitoring and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
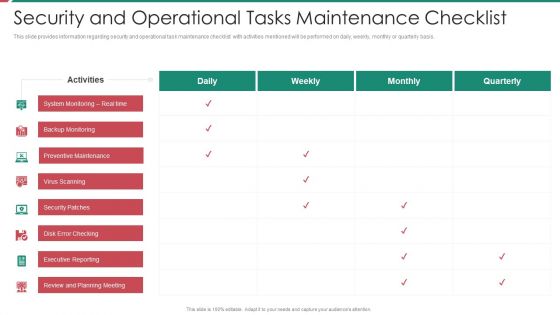
Security And Process Integration Security And Operational Tasks Maintenance Checklist Diagrams PDF
This slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Deliver and pitch your topic in the best possible manner with this security and process integration security and operational tasks maintenance checklist diagrams pdf. Use them to share invaluable insights on system monitoring, executive reporting, planning meeting, preventive maintenance and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
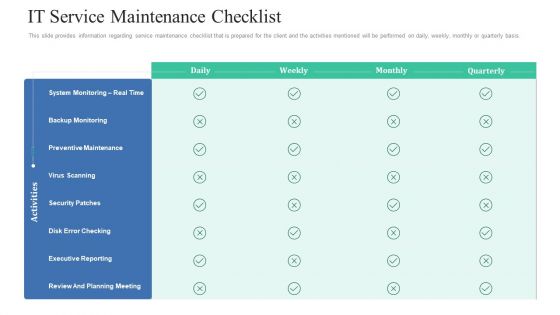
Retaining Clients Improving Information Technology Facilities IT Service Maintenance Checklist Graphics PDF
This slide provides information regarding service maintenance checklist that is prepared for the client and the activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Deliver an awe-inspiring pitch with this creative retaining clients improving information technology facilities it service maintenance checklist graphics pdf bundle. Topics like preventive maintenance, security patches, executive reporting can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Strategic Plan Roadmap For Cyber Security Project Information PDF
This slide signifies the twelve week strategic plan timeline for effective cyber security project. It covers information about installing security, configuring security, provide training and performing penetration testing Pitch your topic with ease and precision using this Strategic Plan Roadmap For Cyber Security Project Information PDF. This layout presents information on Strategic, Plan, Project. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
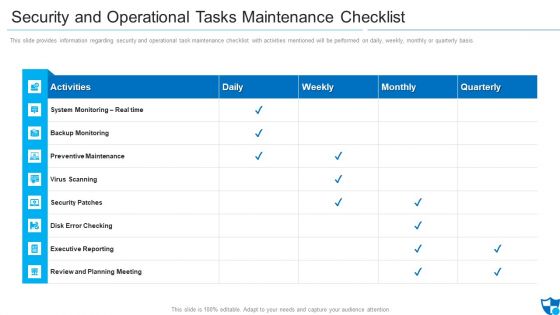
Security And Operational Tasks Maintenance Checklist Infographics PDF
This slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis.Deliver an awe inspiring pitch with this creative security and operational tasks maintenance checklist infographics pdf bundle. Topics like preventive maintenance, security patches, review and planning meeting can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Checklist For Effectively Managing Asset Security Ppt Layouts Introduction PDF
Following slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Deliver and pitch your topic in the best possible manner with this checklist for effectively managing asset security ppt layouts introduction pdf. Use them to share invaluable insights on checklist for effectively managing asset security and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
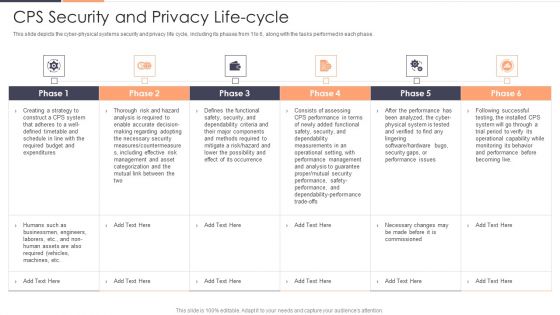
CPS Security And Privacy Life Cycle Ppt Gallery Professional PDF
This slide depicts the cyber physical systems security and privacy life cycle, including its phases from 1 to 6, along with the tasks performed in each phase. Deliver and pitch your topic in the best possible manner with this CPS Security And Privacy Life Cycle Ppt Gallery Professional PDF. Use them to share invaluable insights on Risk, Required, Securityand impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Cloud Security Assessment Roadmap Of Cloud Security Implementation Information PDF
This slide defines the roadmap of cloud security implementation in an organization and what tasks would be performed in each months interval starting from January.Presenting Cloud Security Assessment Roadmap Of Cloud Security Implementation Information PDF to provide visual cues and insights. Share and navigate important information on seven stages that need your due attention. This template can be used to pitch topics like Configuration Management, Services Management, Security Measures. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Cybersecurity Timeline For The Implementation Of Electronic Information Security Ppt Infographic Template Information PDF
This slide shows the timeline for cyber security model implementation in an organization and the tasks to be performed every month. Deliver an awe inspiring pitch with this creative cybersecurity timeline for the implementation of electronic information security ppt infographic template information pdf bundle. Topics like security documentation, network can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Handling Cyber Threats Digital Era Checklist For Effectively Managing Asset Security Ppt Slides Example File PDF
Following slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Deliver an awe inspiring pitch with this creative handling cyber threats digital era checklist for effectively managing asset security ppt slides example file pdf bundle. Topics like checklist for effectively managing asset security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Timeline For The Implementation Of Information Technology Security Ppt Portfolio Slideshow PDF
This slide shows the timeline for network security model implementation in an organization and the tasks to be performed every month. Deliver an awe inspiring pitch with this creative timeline for the implementation of information technology security ppt portfolio slideshow pdf bundle. Topics like timeline for the implementation of information technology security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Enhanced Protection Corporate Event Administration Security And Operational Tasks Maintenance Checklist Slides PDF
This slide provides information regarding security and operational task maintenance checklist with activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Deliver and pitch your topic in the best possible manner with this enhanced protection corporate event administration security and operational tasks maintenance checklist slides pdf. Use them to share invaluable insights on system monitoring, executive reporting, planning meeting, preventive maintenance and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
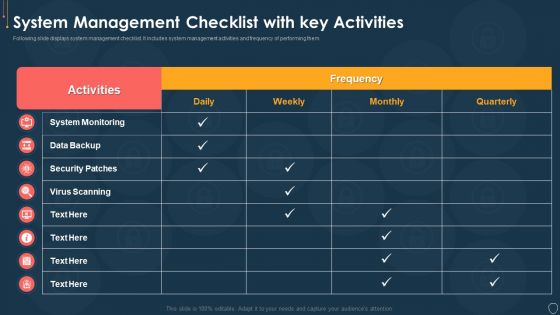
Cyber Security Risk Management Plan System Management Checklist With Key Activities Structure PDF
Following slide displays system management checklist. It includes system management activities and frequency of performing them. Deliver an awe inspiring pitch with this creative cyber security risk management plan system management checklist with key activities structure pdf bundle. Topics like system monitoring, data backup, security patches, virus scanning can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Risk Management Model For Data Security System Management Checklist With Key Activities Guidelines PDF
Following slide displays system management checklist. It includes system management activities and frequency of performing them. Deliver an awe inspiring pitch with this creative Risk Management Model For Data Security System Management Checklist With Key Activities Guidelines PDF bundle. Topics like System Monitoring, Data Backup, Security Patches, Virus Scanning can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
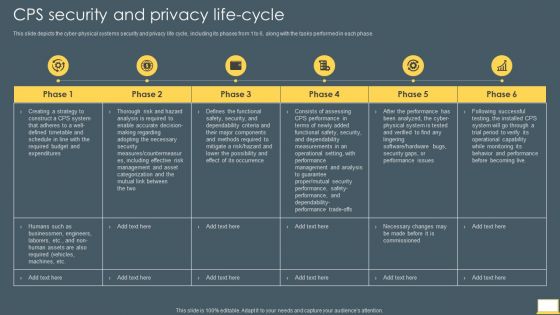
Cyber Intelligent Computing System CPS Security And Privacy Life Cycle Slides PDF
This slide depicts the cyber physical systems security and privacy life cycle, including its phases from 1 to 6, along with the tasks performed in each phase. Deliver an awe inspiring pitch with this creative Cyber Intelligent Computing System CPS Security And Privacy Life Cycle Slides PDF bundle. Topics like Management, Analysis, Required can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
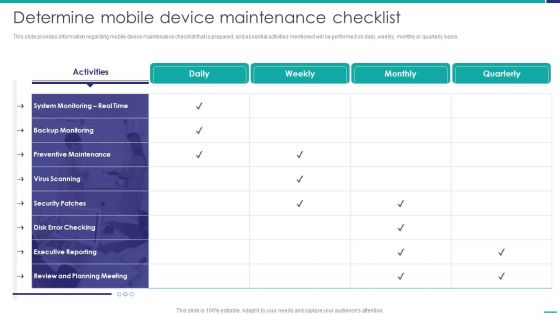
Determine Mobile Device Maintenance Checklist Mobile Device Security Management Graphics PDF
This slide provides information regarding mobile device maintenance checklist that is prepared, and essential activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Deliver an awe inspiring pitch with this creative Determine Mobile Device Maintenance Checklist Mobile Device Security Management Graphics PDF bundle. Topics like Preventive Maintenance, Executive Reporting, Planning Meeting can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Scope For Security Camera Services One Pager Sample Example Document
This slide depicts the project scope providing information about the multiple activities to be performed by the bidding company for the client. Presenting you an exemplary Scope For Security Camera Services One Pager Sample Example Document. Our one-pager comprises all the must-have essentials of an inclusive document. You can edit it with ease, as its layout is completely editable. With such freedom, you can tweak its design and other elements to your requirements. Download this Scope For Security Camera Services One Pager Sample Example Document brilliant piece now.

Roadmap Of Cloud Security Implementation Infographics PDF
This slide defines the roadmap of cloud security implementation in an organization and what tasks would be performed in each months interval starting from January. Presenting Roadmap Of Cloud Security Implementation Infographics PDF to provide visual cues and insights. Share and navigate important information on seven stages that need your due attention. This template can be used to pitch topics like Applications Services Management, Cloud Services Monitoring, Network Security December. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
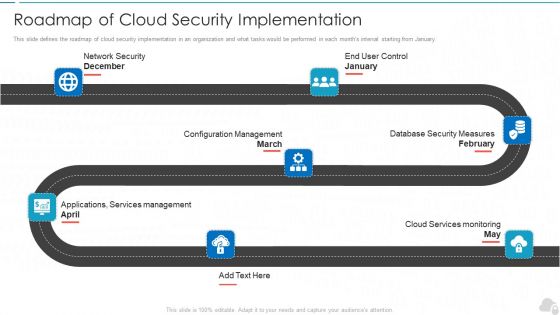
Roadmap Of Cloud Security Implementation Cloud Computing Security IT Ppt Outline Files PDF
This slide defines the roadmap of cloud security implementation in an organization and what tasks would be performed in each months interval starting from January. This is a roadmap of cloud security implementation cloud computing security it ppt outline files pdf template with various stages. Focus and dispense information on seven stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like configuration management, database security measures, cloud services monitoring, applications, services management, network security. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cloud Information Security Roadmap Of Cloud Security Implementation Ppt Styles PDF
This slide defines the roadmap of cloud security implementation in an organization and what tasks would be performed in each months interval starting from January. Presenting Cloud Information Security Roadmap Of Cloud Security Implementation Ppt Styles PDF to provide visual cues and insights. Share and navigate important information on seven stages that need your due attention. This template can be used to pitch topics like Network Security, Configuration Management, Cloud Services. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Effective IT Risk Management Process System Management Checklist Brochure PDF
Following slide displays system management checklist. It includes system management activities and frequency of performing them. Deliver and pitch your topic in the best possible manner with this effective it risk management process system management checklist brochure pdf. Use them to share invaluable insights on security patches, data backup, system monitoring and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Vendor Due Diligence Procedure Checklist Diagrams PDF
The slide shows a checklist for vendors containing number of different asks to be done during performing due diligence process. Persuade your audience using this Vendor Due Diligence Procedure Checklist Diagrams PDF. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including Financial, Payments, Security. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
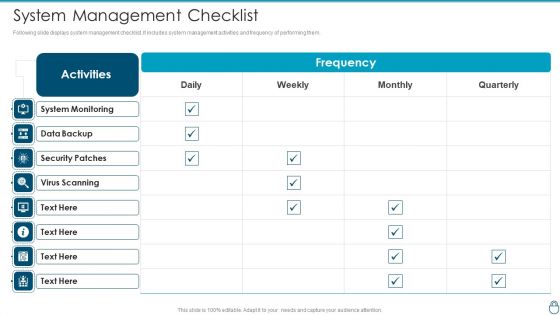
Cybersecurity Risk Administration Plan System Management Checklist Background PDF
Following slide displays system management checklist. It includes system management activities and frequency of performing them.Deliver and pitch your topic in the best possible manner with this Cybersecurity Risk Administration Plan System Management Checklist Background PDF Use them to share invaluable insights on System Monitoring, Security Patches, Virus Scanning and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
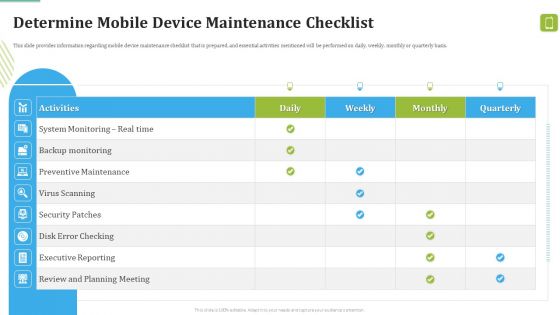
MDM Strategies At Office Determine Mobile Device Maintenance Checklist Download PDF
This slide provides information regarding mobile device maintenance checklist that is prepared, and essential activities mentioned will be performed on daily, weekly, monthly or quarterly basis. Deliver and pitch your topic in the best possible manner with this MDM Strategies At Office Determine Mobile Device Maintenance Checklist Download PDF. Use them to share invaluable insights on Preventive Maintenance, Virus Scanning, Security Patches and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Timeline For Implementing Efficient Application Security Testing
This slide outlines the different steps performed while deploying application security, including planning phase, requirement gathering, etc. Are you searching for a Timeline For Implementing Efficient Application Security Testing that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Timeline For Implementing Efficient Application Security Testing from Slidegeeks today.

Desktop Security Management Process Of Disaster Recovery Planning Professional PDF
This slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. This is a desktop security management process of disaster recovery planning professional pdf template with various stages. Focus and dispense information on one stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like plans, team, risk. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Managed Cyber Security Solutions Service Framework For Operations Management Ppt Styles Themes PDF
The flowing slide highlights managed security service framework. It provides information about components such as clients issues and key operations to be performed by service provider such as antivirus offerings, data loss prevention etc. Presenting Managed Cyber Security Solutions Service Framework For Operations Management Ppt Styles Themes PDF to dispense important information. This template comprises two stages. It also presents valuable insights into the topics including Framework Significance, Business Security Users, Major Bottlenecks. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
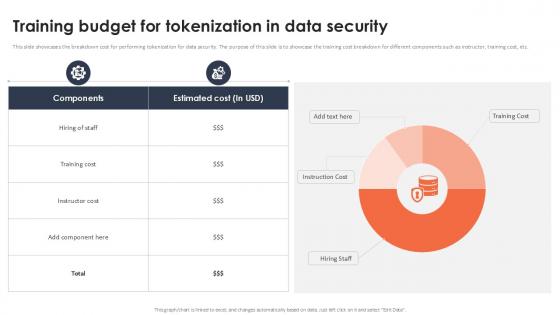
Training Budget For Tokenization In Data Security Securing Your Data Ppt Slide
This slide showcases the breakdown cost for performing tokenization for data security. The purpose of this slide is to showcase the training cost breakdown for different components such as instructor, training cost, etc. If your project calls for a presentation, then Slidegeeks is your go-to partner because we have professionally designed, easy-to-edit templates that are perfect for any presentation. After downloading, you can easily edit Training Budget For Tokenization In Data Security Securing Your Data Ppt Slide and make the changes accordingly. You can rearrange slides or fill them with different images. Check out all the handy templates

Training Budget For Tokenization In Data Security PPT Template
This slide showcases the breakdown cost for performing tokenization for data security. The purpose of this slide is to showcase the training cost breakdown for different components such as instructor, training cost, etc. Find a pre-designed and impeccable Training Budget For Tokenization In Data Security PPT Template. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

Timeline To Implementation Tokenization In Data Security PPT Powerpoint
This slide outlines the timeline for executing tokenization. The purpose of this slide is to showcase the different steps performed while implementing tokenization, including key management, monitoring, etc. Find a pre-designed and impeccable Timeline To Implementation Tokenization In Data Security PPT Powerpoint. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.
Kpi Dashboard For Tracking Virtual Security Hazards Of Healthcare Organization Professional Pdf
This slide depicts dashboard for tracking cyber security risks faced by healthcare organizations to effectively manage the major threats and take action accordingly. The key performing indicators are percentage of risks exceeding threshold limit, breakdown of threat rating, action plan etc. Showcasing this set of slides titled Kpi Dashboard For Tracking Virtual Security Hazards Of Healthcare Organization Professional Pdf. The topics addressed in these templates are Analysis Progress, Resolution Progress, Threshold Limit. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
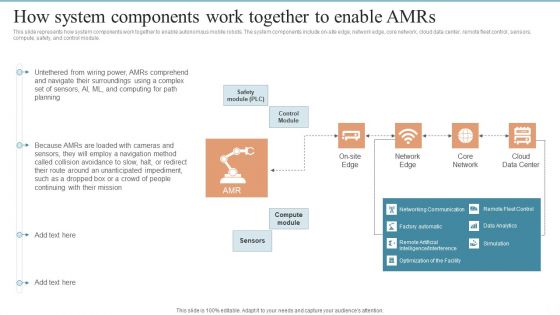
AMR Robot How System Components Work Together To Enable Amrs Ppt PowerPoint Presentation File Slides PDF
This slide represents how system components work together to enable autonomous mobile robots. The system components include on-site edge, network edge, core network, cloud data center, remote fleet control, sensors, compute, safety, and control module. This AMR Robot How System Components Work Together To Enable Amrs Ppt PowerPoint Presentation File Slides PDF from Slidegeeks makes it easy to present information on your topic with precision. It provides customization options, so you can make changes to the colors, design, graphics, or any other component to create a unique layout. It is also available for immediate download, so you can begin using it right away. Slidegeeks has done good research to ensure that you have everything you need to make your presentation stand out. Make a name out there for a brilliant performance.
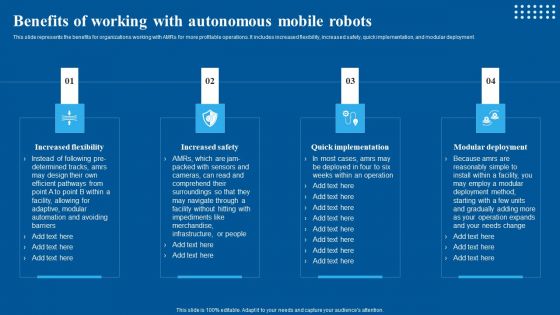
Benefits Of Working With Autonomous Mobile Robots Designs PDF
This slide represents the benefits for organizations working with AMRs for more profitable operations. It includes increased flexibility, increased safety, quick implementation, and modular deployment. This Benefits Of Working With Autonomous Mobile Robots Designs PDF from Slidegeeks makes it easy to present information on your topic with precision. It provides customization options, so you can make changes to the colors, design, graphics, or any other component to create a unique layout. It is also available for immediate download, so you can begin using it right away. Slidegeeks has done good research to ensure that you have everything you need to make your presentation stand out. Make a name out there for a brilliant performance.
Advantages Of Using Robots In Industrial Sector Icons PDF
This slide illustrates the benefits of using robots in industries. The purpose of this slide is to explain how industrial sector is getting optimized from robotic automation. Their key pros included are high speed, increased load capacity, improved safety, etc. This Advantages Of Using Robots In Industrial Sector Icons PDF from Slidegeeks makes it easy to present information on your topic with precision. It provides customization options, so you can make changes to the colors, design, graphics, or any other component to create a unique layout. It is also available for immediate download, so you can begin using it right away. Slidegeeks has done good research to ensure that you have everything you need to make your presentation stand out. Make a name out there for a brilliant performance.

Why Should Organizations Invest In Cobots Transforming Industries With Collaborative Robotics Sample Pdf
This slide describes the reasons for organizations to invest in cobots. It includes low-cost, safety, flexibility, more straightforward automation for all sizes of organizations, and is designed to work in a shared environment. This Why Should Organizations Invest In Cobots Transforming Industries With Collaborative Robotics Sample Pdf from Slidegeeks makes it easy to present information on your topic with precision. It provides customization options, so you can make changes to the colors, design, graphics, or any other component to create a unique layout. It is also available for immediate download, so you can begin using it right away. Slidegeeks has done good research to ensure that you have everything you need to make your presentation stand out. Make a name out there for a brilliant performance.
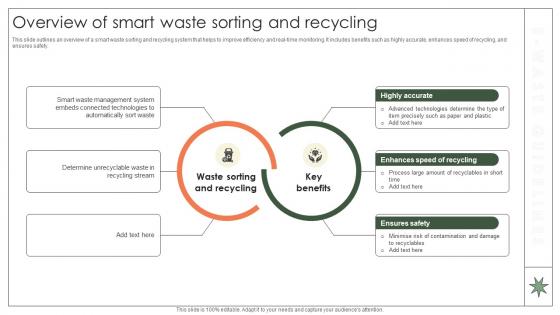
Overview Of Smart Waste Sorting And Recycling Implementation Of E Waste Guidelines
This slide outlines an overview of a smart waste sorting and recycling system that helps to improve efficiency and real-time monitoring. It includes benefits such as highly accurate, enhances speed of recycling, and ensures safety. This Overview Of Smart Waste Sorting And Recycling Implementation Of E Waste Guidelines from Slidegeeks makes it easy to present information on your topic with precision. It provides customization options, so you can make changes to the colors, design, graphics, or any other component to create a unique layout. It is also available for immediate download, so you can begin using it right away. Slidegeeks has done good research to ensure that you have everything you need to make your presentation stand out. Make a name out there for a brilliant performance.

Overview Of Food Analysis And Quality Control Guide For Food PPT Slide
This slide gives an overview of food quality control programs that are to be followed by managers and ensure consumers safety. Major elements covered in the slide are the goals and characteristics of the food quality control system. This Overview Of Food Analysis And Quality Control Guide For Food PPT Slide from Slidegeeks makes it easy to present information on your topic with precision. It provides customization options, so you can make changes to the colors, design, graphics, or any other component to create a unique layout. It is also available for immediate download, so you can begin using it right away. Slidegeeks has done good research to ensure that you have everything you need to make your presentation stand out. Make a name out there for a brilliant performance.

Information Security Process Of Disaster Recovery Planning Ppt Portfolio Backgrounds PDF
This slide represents the detailed process of a disaster recovery plan, how it should work, what points to keep in mind, and what steps to be performed to build the best recovery plan. Presenting information security process of disaster recovery planning ppt portfolio backgrounds pdf to provide visual cues and insights. Share and navigate important information on eight stages that need your due attention. This template can be used to pitch topics like recovery team, risk analysis, prioritize procedures, recovery plan, data collection. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

30 60 90 Days Plan To Implement Cloud Security In Business Ppt Layouts Sample PDF
This slide defines the 30,60 and 90 days plan to implement cloud security in the organization and what tasks would be performed on each 30 days interval. This is a 30 60 90 Days Plan To Implement Cloud Security In Business Ppt Layouts Sample PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Analyze Different, Cloud Services, Provided Vendors. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
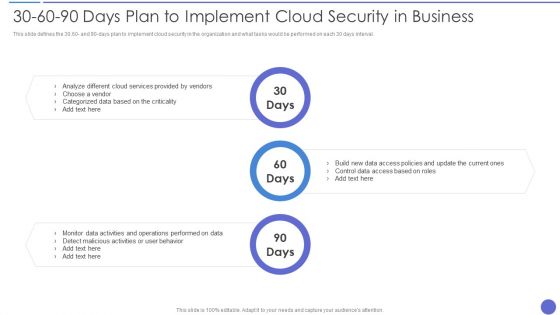
30 60 90 Days Plan To Implement Cloud Security In Business Information PDF
This slide defines the 30,60 and 90 days plan to implement cloud security in the organization and what tasks would be performed on each 30 days interval. This is a 30 60 90 Days Plan To Implement Cloud Security In Business Information PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Analyze, Cloud Services Provided , Control Data. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Three Lines Of Defense Border Model For Cyber Security Designs PDF
This slide represents the model of lines of defense for products and services quality assurance. It includes activities performed in first, second and third line of defense for quality assurance such as risk management, monitor and support in risk related matters, internal quality audits etc. Presenting Three Lines Of Defense Border Model For Cyber Security Designs PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Cyber Security, Three Lines, Border Model. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Cyber Security Incident Response Coordination Activities Ppt Powerpoint Presentation File Portfolio Pdf
This slide represents the activities performed by cyber security incident management team to eradicate and recover cyber security incidents in order to reduce their impact on business operations. It starts with the declaration of incident and ends with post incident activity. Make sure to capture your audiences attention in your business displays with our gratis customizable Cyber Security Incident Response Coordination Activities Ppt Powerpoint Presentation File Portfolio Pdf. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.

Desktop Security Management Security Framework In Cloud Computing Demonstration PDF
This slide depicts how tasks are performed under cloud security through the framework. The framework consists of different stages such as identity, protection, detection, response, and recovery. This is a desktop security management security framework in cloud computing demonstration pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like protect, detect, respond, recover, identify. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
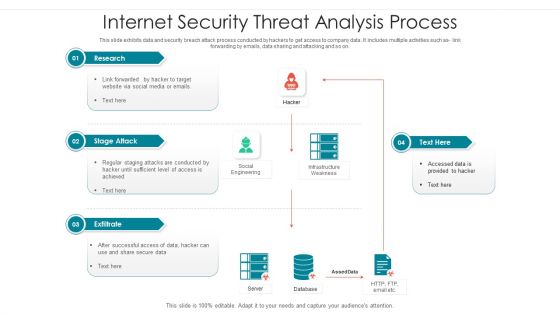
Internet Security Threat Analysis Process Brochure PDF
Following slide showcase how a data breach process is performed by hacker to collect and utilize company data. It includes following activities such as code integration with company software, so on. Showcasing this set of slides titled internet security threat analysis process brochure pdf. The topics addressed in these templates are supply chain attack, execution persistence, defense evasion, exfiltration, keyboard attack. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Developing Firm Security Strategy Plan Information Security Process To Manage Firms Sensitive Data Introduction PDF
This slide provides information about information security process in order to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc. This is a developing firm security strategy plan information security process to manage firms sensitive data introduction pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like privileged password management, daily tasks performed by network administrator, network security audit checklist. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Project Security Administration IT Information Security Process To Manage Firms Sensitive Data Summary PDF
This slide provides information about information security process in order to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc. Deliver an awe inspiring pitch with this creative project security administration it information security process to manage firms sensitive data summary pdf bundle. Topics like privileged password management, daily tasks performed by network administrator, network security audit checklist can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Risk Based Procedures To IT Security Checklist For Effectively Managing Asset Security Portrait PDF
Following slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. This is a Risk Based Procedures To IT Security Checklist For Effectively Managing Asset Security Portrait PDF template with various stages. Focus and dispense information on one stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like System Monitoring, Data Backup, Security Patches. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

IT Security Risk Management Approach Introduction Checklist For Effectively Managing Asset Security Sample PDF
Following slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. This is a IT Security Risk Management Approach Introduction Checklist For Effectively Managing Asset Security Sample PDF template with various stages. Focus and dispense information on one stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like System Monitoring, Data Backup, Security Patches. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Security Framework In Cloud Computing IT Security IT Ppt Portfolio Pictures PDF
This slide depicts how tasks are performed under cloud security through the framework. The framework consists of different stages such as identity, protection, detection, response, and recovery. This is a security framework in cloud computing it security it ppt portfolio pictures pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like recover, respond, protect, identify, detect. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

 Home
Home