Access Control
Role Based Access Control RBAC Icon Access Control Brochure PDF
Pitch your topic with ease and precision using this Role Based Access Control RBAC Icon Access Control Brochure PDF. This layout presents information on Role Based Access, Control RBAC . It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Cloud Security Checklist Access Control Rules PDF
This slide depicts the access control under the cloud security checklist and how it affects the organizations when data breaches happen due to poor access control management. Presenting Cloud Security Checklist Access Control Rules PDF to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like Security, Systems, Networks. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Aspects Of Information System Access Control Security Auditing Diagrams PDF
The following slide highlights the aspects of information system access control security audit illustrating key headings which incudes data access control, authentication privacy, user identity, user management, password management, network access control, and login Presenting Aspects Of Information System Access Control Security Auditing Diagrams PDF to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including User Management, Data Access Control, Network Access Control. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Information Security Access Control Ppt PowerPoint Presentation Inspiration
This is a information security access control ppt powerpoint presentation inspiration. This is a three stage process. The stages in this process are access rights, access management, business.
Role Based Access Control RBAC Icon Topics PDF
Persuade your audience using this Role Based Access Control RBAC Icon Topics PDF. This PPT design covers Three stages, thus making it a great tool to use. It also caters to a variety of topics including Role Based Access, Control RBAC Icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Role Based Access Control RBAC Securities Icon Demonstration PDF
Persuade your audience using this Role Based Access Control RBAC Securities Icon Demonstration PDF. This PPT design covers Three stages, thus making it a great tool to use. It also caters to a variety of topics including Role Based, Access Control. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Fingerprint Access Control Biometric Solution Ppt PowerPoint Presentation Pictures Format
This is a fingerprint access control biometric solution ppt powerpoint presentation pictures format. This is a two stage process. The stages in this process are access rights, access management, business.

Cloud Security Assessment Cloud Security Checklist Access Control Sample PDF
This slide depicts the access control under the cloud security checklist and how it affects the organizations when data breaches happen due to poor access control management.This is a Cloud Security Assessment Cloud Security Checklist Access Control Sample PDF template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Administrative Rights, Privileged Credentials, Legitimate Users You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
System Security Access Control Ppt PowerPoint Presentation Summary Background Cpb
Presenting this set of slides with name system security access control ppt powerpoint presentation summary background cpb. This is an editable Powerpoint six stages graphic that deals with topics like system security access control to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Access Control Ppt PowerPoint Presentation Slides Demonstration Cpb
Presenting this set of slides with name access control ppt powerpoint presentation slides demonstration cpb. This is an editable Powerpoint eight stages graphic that deals with topics like access control to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Access Control Ppt PowerPoint Presentation Layouts Display Cpb
Presenting this set of slides with name access control ppt powerpoint presentation layouts display cpb. This is an editable Powerpoint six stages graphic that deals with topics like access control to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Access Control Authentication Ppt PowerPoint Presentation Images Cpb Pdf
Presenting this set of slides with name access control authentication ppt powerpoint presentation images cpb pdf. This is an editable Powerpoint four stages graphic that deals with topics like access control authentication to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
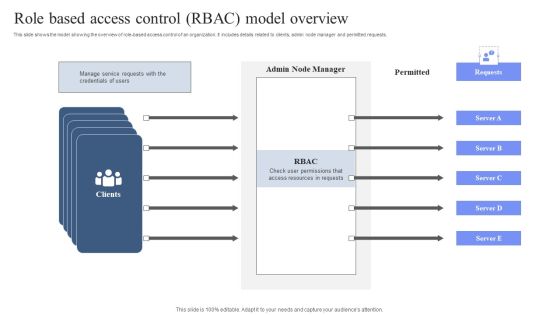
Role Based Access Control RBAC Model Overview Pictures PDF
This slide shows the model showing the overview of role based access control of an organization. It includes details related to clients, admin node manager and permitted requests. Showcasing this set of slides titled Role Based Access Control RBAC Model Overview Pictures PDF. The topics addressed in these templates are Manage Service, Credentials Of Users. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Cloud Access Control Ppt PowerPoint Presentation Icon Cpb Pdf
Presenting this set of slides with name cloud access control ppt powerpoint presentation icon cpb pdf. This is an editable Powerpoint four stages graphic that deals with topics like cloud access control to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Conditional Database Access Control With Intelligence Download PDF
This slide depicts conditional access control with intelligence for organizational data. The purpose of this slide is to show secure data access through AI. It integrates with any SaaS application, on-premises apps, and virtual private network solutions. It also includes four types of controls such as block, allow, MFA, and session control. Pitch your topic with ease and precision using this Conditional Database Access Control With Intelligence Download PDF. This layout presents information on Company Data, Modern, Intelligence. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
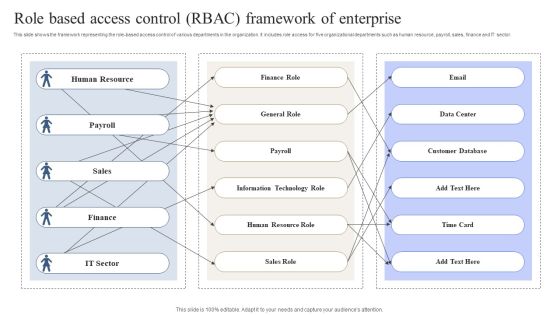
Role Based Access Control RBAC Framework Of Enterprise Download PDF
This slide shows the framework representing the role-based access control of various departments in the organization. It includes role access for five organizational departments such as human resource, payroll, sales, finance and IT sector. Showcasing this set of slides titled Role Based Access Control RBAC Framework Of Enterprise Download PDF. The topics addressed in these templates are Human Resource, Finance Role, Email. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
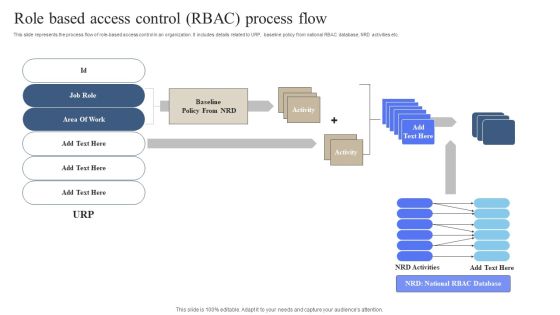
Role Based Access Control RBAC Process Flow Information PDF
This slide represents the process flow of role based access control in an organization. It includes details related to URP, baseline policy from national RBAC database, NRD activities etc. Pitch your topic with ease and precision using this Role Based Access Control RBAC Process Flow Information PDF. This layout presents information on Area Of Work, Baseline, Policy From NRD. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
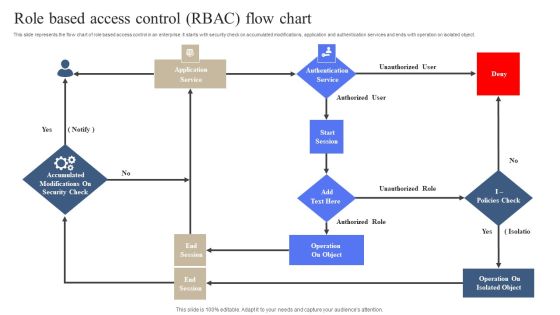
Role Based Access Control RBAC Flow Chart Slides PDF
This slide represents the flow chart of role based access control in an enterprise. It starts with security check on accumulated modifications, application and authentication services and ends with operation on isolated object. Persuade your audience using this Role Based Access Control RBAC Flow Chart Slides PDF. This PPT design covers One stage, thus making it a great tool to use. It also caters to a variety of topics including Operation On Object, Operation On Isolated Object. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

FDDI Deployment Mac Medium Access Control Layer Designs PDF
This slide explains the medium layer as the responsible layer for identifying addresses as well as creating and verifying FCS and also specifies how to handle the synchronous and asynchronous data flow. Whether you have daily or monthly meetings, a brilliant presentation is necessary. FDDI Deployment Mac Medium Access Control Layer Designs PDF can be your best option for delivering a presentation. Represent everything in detail using FDDI Deployment Mac Medium Access Control Layer Designs PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.

Cyber Terrorism Assault Employee Access Control Protocols Diagrams PDF
This slide highlights how it is critical to limit employee rights and access in order to keep data safe and prevent it from being deleted or manipulated.This is a cyber terrorism assault employee access control protocols diagrams pdf template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Distributed Denial Of Service DDOS As Cyber Terrorism Tool You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Determine And Access Control Ppt PowerPoint Presentation Complete With Slides
Improve your presentation delivery using this Determine And Access Control Ppt PowerPoint Presentation Complete With Slides. Support your business vision and objectives using this well-structured PPT deck. This template offers a great starting point for delivering beautifully designed presentations on the topic of your choice. Comprising tweleve this professionally designed template is all you need to host discussion and meetings with collaborators. Each slide is self-explanatory and equipped with high-quality graphics that can be adjusted to your needs. Therefore, you will face no difficulty in portraying your desired content using this PPT slideshow. This PowerPoint slideshow contains every important element that you need for a great pitch. It is not only editable but also available for immediate download and utilization. The color, font size, background, shapes everything can be modified to create your unique presentation layout. Therefore, download it now.
Ensure Security And Access Controls Ppt PowerPoint Presentation Pictures Examples
This is a ensure security and access controls ppt powerpoint presentation pictures examples. This is a two stage process. The stages in this process are business, planning, strategy, marketing, management.

Ensure Security And Access Controls Ppt PowerPoint Presentation Inspiration Portfolio
This is a ensure security and access controls ppt powerpoint presentation inspiration portfolio. This is a two stage process. The stages in this process are marketing, management, strategy, business, planning.
Ensure Security And Access Controls Ppt PowerPoint Presentation Portfolio Images
This is a ensure security and access controls ppt powerpoint presentation portfolio images. This is a two stage process. The stages in this process are icons, strategy, business, management, marketing.
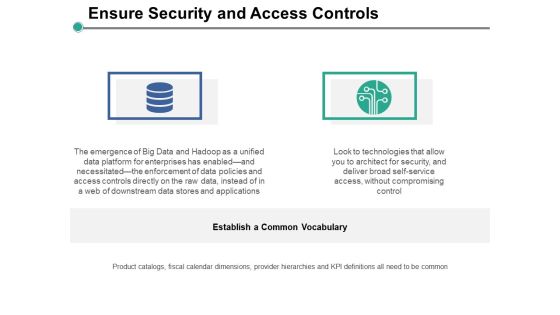
Ensure Security And Access Controls Ppt PowerPoint Presentation Slides Information
This is a ensure security and access controls ppt powerpoint presentation slides information. This is a two stage process. The stages in this process are business, management, planning, strategy, marketing.

Cloud Security Checklist Access Control Cloud Computing Security IT Ppt Show PDF
This slide depicts the access control under the cloud security checklist and how it affects the organizations when data breaches happen due to poor access control management. Deliver and pitch your topic in the best possible manner with this cloud security checklist access control cloud computing security it ppt show pdf. Use them to share invaluable insights on cloud services, security, privileged credentials, administrative and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Hotel Card Door Lock Access Control Vector Icon Ppt PowerPoint Presentation File Icon PDF
Presenting hotel card door lock access control vector icon ppt powerpoint presentation file icon pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including hotel card door lock access control vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Virtual Identify Biometric Access Control With Finger Print Scanner Themes PDF
Presenting virtual identify biometric access control with finger print scanner themes pdf to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including virtual identify biometric access control with finger print scanner. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Access Control Management With User Id And Password Ppt PowerPoint Presentation Icon Introduction
This is a access control management with user id and password ppt powerpoint presentation icon introduction. This is a three stage process. The stages in this process are access rights, access management, business.
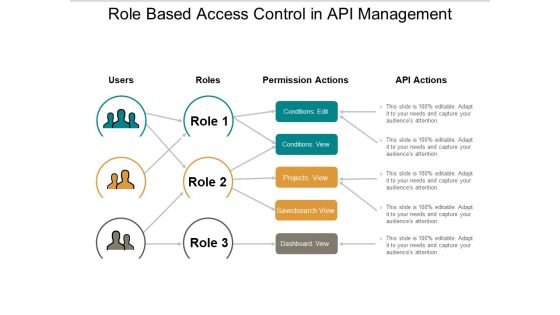
Role Based Access Control In Api Management Ppt PowerPoint Presentation Portfolio Template
This is a role based access control in api management ppt powerpoint presentation portfolio template. This is a three stage process. The stages in this process are access rights, access management, business.

Access Control System Key Security Lock Ppt PowerPoint Presentation Pictures Summary
This is a access control system key security lock ppt powerpoint presentation pictures summary. This is a three stage process. The stages in this process are access rights, access management, business.
Security Access Control Iris Scanning System Ppt PowerPoint Presentation Show Gridlines
This is a security access control iris scanning system ppt powerpoint presentation show gridlines. This is a two stage process. The stages in this process are access rights, access management, business.

Access Control Application Account Security Lock Ppt PowerPoint Presentation File Slide Portrait
This is a access control application account security lock ppt powerpoint presentation file slide portrait. This is a two stage process. The stages in this process are access rights, access management, business.

Door Access Control Padlock On Door Ppt PowerPoint Presentation Infographic Template Graphics Example
This is a door access control padlock on door ppt powerpoint presentation infographic template graphics example. This is a four stage process. The stages in this process are access rights, access management, business.

Cloud Information Security Cloud Security Checklist Access Control Ppt Inspiration Professional PDF
This slide depicts the access control under the cloud security checklist and how it affects the organizations when data breaches happen due to poor access control management. This is a Cloud Information Security Cloud Security Checklist Access Control Ppt Inspiration Professional PDF template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Control Identity, Security Breaches, Data Servers. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
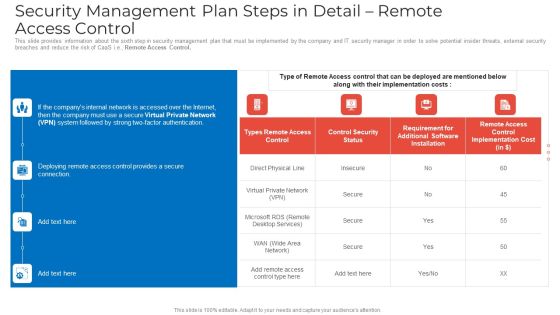
Security Management Plan Steps In Detail Remote Access Control Mockup PDF
This slide provides information about the sixth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e. Remote Access Control. Deliver an awe inspiring pitch with this creative security management plan steps in detail remote access control mockup pdf bundle. Topics like security management plan steps in detail remote access control can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Security Management Plan Steps In Detail Remote Access Control Diagrams PDF
This is a security management plan steps in detail remote access control diagrams pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like control security status, requirement for additional software installation, remote access control. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Person Opening Office Door With Security Access Control System Ppt PowerPoint Presentation Styles Rules PDF
Presenting person opening office door with security access control system ppt powerpoint presentation styles rules pdf to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including person opening office door with security access control system. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

ERP Software Solutions With Access Control Ppt PowerPoint Presentation Portfolio Pictures PDF
Presenting erp software solutions with access control ppt powerpoint presentation portfolio pictures pdf to dispense important information. This template comprises eight stages. It also presents valuable insights into the topics including access control, human resources, finance accounting, engineering, project management, data services, crm, purchasing. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Access Control Security SAP Ppt PowerPoint Presentation Portfolio Designs Cpb Pdf
Presenting this set of slides with name access control security sap ppt powerpoint presentation portfolio designs cpb pdf. This is an editable Powerpoint five stages graphic that deals with topics like access control security sap to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Role Based Access Control Ppt PowerPoint Presentation Summary Outfit Cpb Pdf
Presenting this set of slides with name role based access control ppt powerpoint presentation summary outfit cpb pdf. This is an editable Powerpoint six stages graphic that deals with topics like role based access control to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Access Control On Security Surveillance Vector Icon Ppt PowerPoint Presentation Gallery Graphics Download PDF
Persuade your audience using this access control on security surveillance vector icon ppt powerpoint presentation gallery graphics download pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including access control on security surveillance vector icon. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Person Protecting Data By Using Network Access Control Ppt PowerPoint Presentation Gallery Infographics PDF
Persuade your audience using this person protecting data by using network access control ppt powerpoint presentation gallery infographics pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including person protecting data by using network access control. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
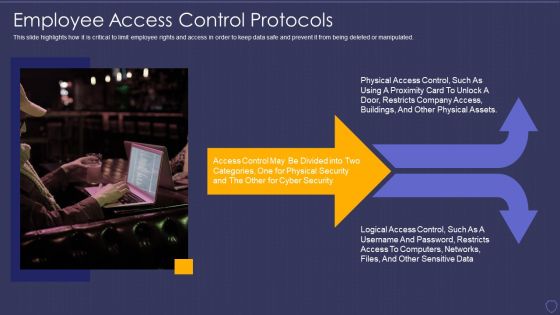
Global Cyber Terrorism Incidents On The Rise IT Employee Access Control Protocols Download PDF
This slide highlights how it is critical to limit employee rights and access in order to keep data safe and prevent it from being deleted or manipulated. Presenting global cyber terrorism incidents on the rise it employee access control protocols download pdf to provide visual cues and insights. Share and navigate important information on one stages that need your due attention. This template can be used to pitch topics like employee access control protocols. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
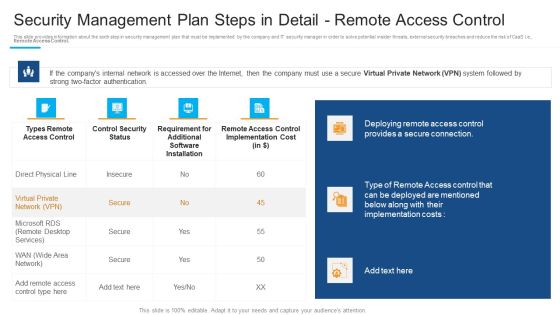
Security Management Plan Steps In Detail Remote Access Control Inspiration PDF
Deliver an awe inspiring pitch with this creative security management plan steps in detail remote access control inspiration pdf bundle. Topics like deploying remote access, provides a secure connection, requirement for additional can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Media Access Control Mac Layer Functions 5G Network Structure Infographics PDF
This slide represents the functions of the media access control sublayer in 5G-NR layer 2, such as padding, HARQ-based error correction, information reporting schedule, and mapping between logical and transport channels.If you are looking for a format to display your unique thoughts, then the professionally designed Media Access Control Mac Layer Functions 5G Network Structure Infographics PDF is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Media Access Control Mac Layer Functions 5G Network Structure Infographics PDF and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.

5G Network Operations Media Access Control MAC Layer Functions Professional PDF
This slide represents the functions of the media access control sublayer in 5G-NR layer 2, such as padding, HARQ-based error correction, information reporting schedule, and mapping between logical and transport channels. If you are looking for a format to display your unique thoughts, then the professionally designed 5G Network Operations Media Access Control MAC Layer Functions Professional PDF. is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download 5G Network Operations Media Access Control MAC Layer Functions Professional PDF. and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.
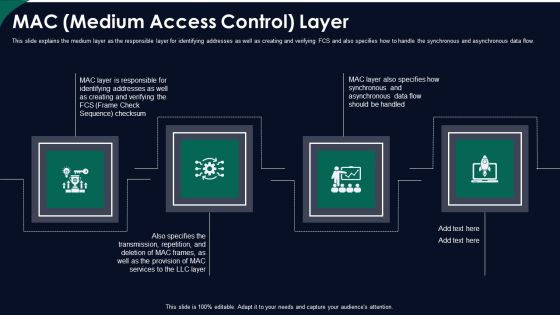
FDDI Network Standard IT MAC Medium Access Control Layer Ppt Layouts Deck PDF
This slide explains the medium layer as the responsible layer for identifying addresses as well as creating and verifying FCS and also specifies how to handle the synchronous and asynchronous data flow. Presenting fddi network standard it mac medium access control layer ppt layouts deck pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like mac medium access control layer. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Access Control In Secured DBMS Software Ppt PowerPoint Presentation Gallery Portrait PDF
This slide represents the block diagram representing the access control in secured database management system. It includes details related to database and security administrator, authorization system, database schemas, application programs etc. Presenting Access Control In Secured DBMS Software Ppt PowerPoint Presentation Gallery Portrait PDF to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including Database Administrator, Security Administrator, Database, Application Programs. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

5G Network Applications And Features Media Access Control MAC Layer Functions Graphics PDF
This slide represents the functions of the media access control sublayer in 5G-NR layer 2, such as padding, HARQ-based error correction, information reporting schedule, and mapping between logical and transport channels. Find a pre-designed and impeccable 5G Network Applications And Features Media Access Control MAC Layer Functions Graphics PDF. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

Security Management Plan Steps In Detail Remote Access Control Topics PDF
This slide provides information about the sixth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e., Remote Access Control. Deliver and pitch your topic in the best possible manner with this security management plan steps in detail remote access control topics pdf. Use them to share invaluable insights on requirement, security, implementation cost and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Media Access Control Mac Layer Functions 5G Functional Architecture Clipart PDF
Deliver an awe inspiring pitch with this creative Media Access Control Mac Layer Functions 5G Functional Architecture Clipart PDF bundle. Topics like Transport Channels, Scheduling Provides, Management Between can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
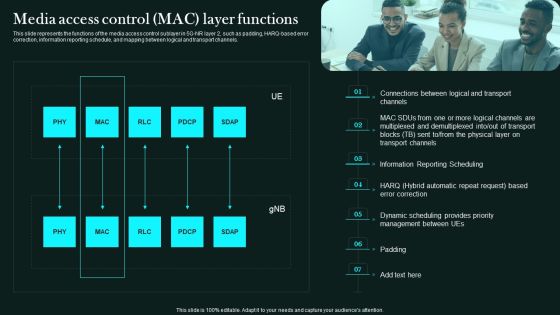
Media Access Control Mac Layer Functions 5G Network Functional Architecture Inspiration PDF
This slide represents the functions of the media access control sublayer in 5G-NR layer 2, such as padding, HARQ-based error correction, information reporting schedule, and mapping between logical and transport channels.Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Media Access Control Mac Layer Functions 5G Network Functional Architecture Inspiration PDF and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
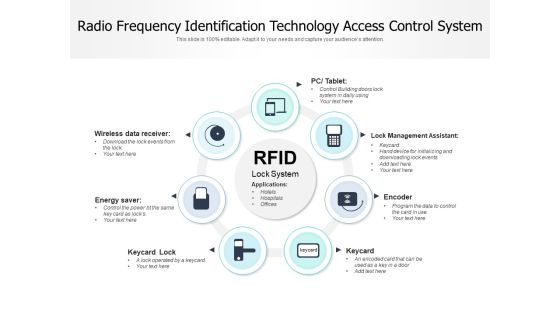
Radio Frequency Identification Technology Access Control System Ppt PowerPoint Presentation Ideas Elements PDF
Persuade your audience using this radio frequency identification technology access control system ppt powerpoint presentation ideas elements pdf. This PPT design covers seven stages, thus making it a great tool to use. It also caters to a variety of topics including pc table, lock management assistant, encoder, keycard, keycard lock, energy saver, wireless data receiver. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
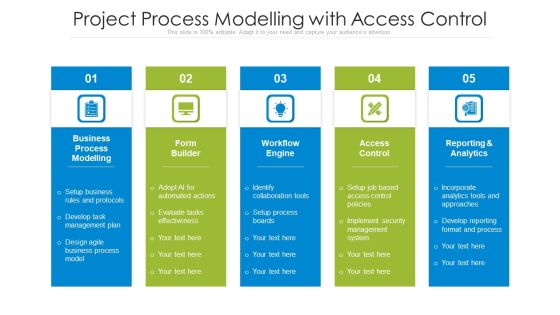
Project Process Modelling With Access Control Ppt PowerPoint Presentation Styles Layouts PDF
Persuade your audience using this project process modelling with access control ppt powerpoint presentation styles layouts pdf. This PPT design covers five stages, thus making it a great tool to use. It also caters to a variety of topics including setup business rules and protocols, develop task management plan, design agile business process model. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Define Access Control Measures For Employees IT Security IT Ppt Professional Icon PDF
This slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. This is a define access control measures for employees it security it ppt professional icon pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like organization, access data, networks, responsibilities. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
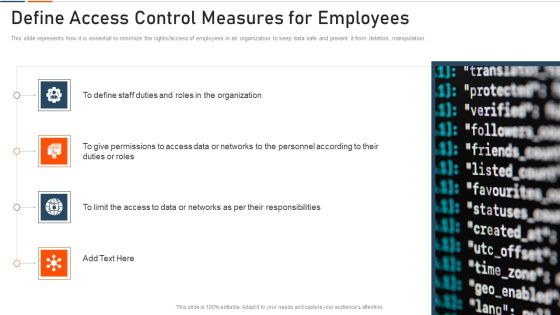
Information Technology Security Define Access Control Measures For Employees Ppt Professional Design Templates PDF
This slide represents how it is essential to minimize the rights access of employees in an organization to keep data safe and prevent it from deletion, manipulation. This is a information technology security define access control measures for employees ppt professional design templates pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like staff duties, organization, roles, access, permissions. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
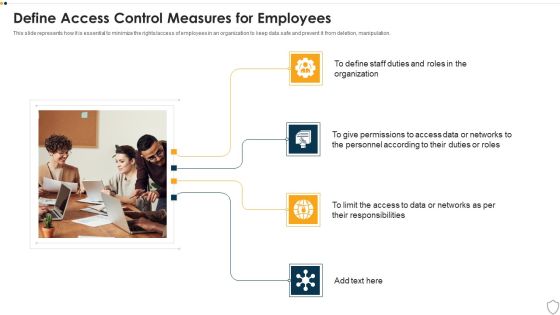
IT Security Define Access Control Measures For Employees Ppt Styles Good PDF
This slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. Presenting it security define access control measures for employees ppt styles good pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like organization, responsibilities, access. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
Info Security Define Access Control Measures For Employees Ppt PowerPoint Presentation Gallery Icon PDF
This slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. Presenting info security define access control measures for employees ppt powerpoint presentation gallery icon pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like access data, personnel according, duties or roles, organization. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Desktop Security Management Define Access Control Measures For Employees Icons PDF
This slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. This is a desktop security management define access control measures for employees icons pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like organization, networks. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Information Security Define Access Control Measures For Employees Ppt Icon Pictures PDF
This slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. This is a information security define access control measures for employees ppt icon pictures pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like networks, organization. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cybersecurity Define Access Control Measures For Employees Ppt Show Clipart Images PDF
This slide represents how it is essential to minimize the rights or access of employees in an organization to keep data safe and prevent it from deletion, manipulation. This is a cybersecurity define access control measures for employees ppt show clipart images pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like organization, networks. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Optimizing Fiber Distributed Data Interface To Enhance Processes Mac Medium Access Control Layer Portrait PDF
This slide explains the medium layer as the responsible layer for identifying addresses as well as creating and verifying FCS and also specifies how to handle the synchronous and asynchronous data flow. Slidegeeks is here to make your presentations a breeze with Optimizing Fiber Distributed Data Interface To Enhance Processes Mac Medium Access Control Layer Portrait PDF With our easy to use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first.

Role Based Access Control Model Ppt PowerPoint Presentation Complete Deck With Slides
If designing a presentation takes a lot of your time and resources and you are looking for a better alternative, then this Role Based Access Control Model Ppt PowerPoint Presentation Complete Deck With Slides is the right fit for you. This is a prefabricated set that can help you deliver a great presentation on the topic. All the Twelve slides included in this sample template can be used to present a birds eye view of the topic. These slides are also fully editable, giving you enough freedom to add specific details to make this layout more suited to your business setting. Apart from the content, all other elements like color, design, theme are also replaceable and editable. This helps in designing a variety of presentations with a single layout. Not only this, you can use this PPT design in formats like PDF, PNG, and JPG once downloaded. Therefore, without any further ado, download and utilize this sample presentation as per your liking.

Access Control Computer Screen With Lock Ppt PowerPoint Presentation Ideas Templates
This is aaccess control computer screen with lock ppt powerpoint presentation ideas templates. This is a two stage process. The stages in this process are access rights, access management, business.
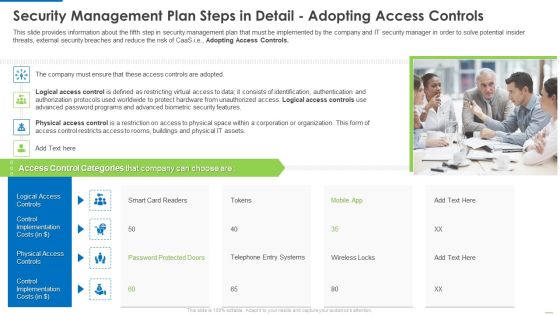
Security Management Plan Steps In Detail Adopting Access Controls Clipart PDF
Deliver and pitch your topic in the best possible manner with this Security management plan steps in detail adopting access controls clipart pdf. Use them to share invaluable insights on logical access controls, physical access controls, control implementation costs and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Security Management Plan Steps In Detail Adopting Access Controls Demonstration PDF
Presenting security management plan steps in detail adopting access controls demonstration pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like logical access controls, control implementation, physical access controls. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Security Management Plan Steps In Detail Adopting Access Controls Download PDF
This slide provides information about the fifth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e. Adopting Access Controls. Deliver an awe inspiring pitch with this creative security management plan steps in detail adopting access controls download pdf bundle. Topics like logical access controls, control implementation costs, physical access controls can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
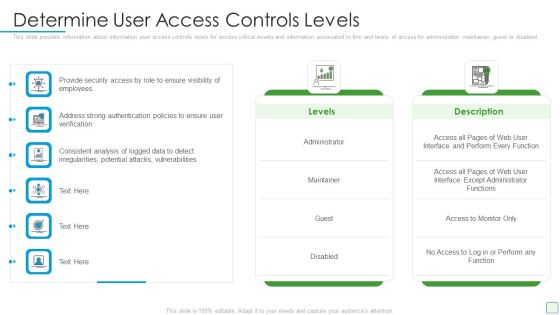
Developing Firm Security Strategy Plan Determine User Access Controls Levels Guidelines PDF
This slide provides information about information user access controls levels for access critical assets and information associated to firm and levels of access for administrator, maintainer, guest or disabled. Deliver an awe inspiring pitch with this creative developing firm security strategy plan determine user access controls levels guidelines pdf bundle. Topics like administrator, maintainer, guest or disabled can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Organizational Assets Security Management Strategy Determine User Access Controls Levels Diagrams PDF
This slide provides information about information user access controls levels for access critical assets and information associated to firm and levels of access for administrator, maintainer, guest or disabled. Get a simple yet stunning designed Organizational Assets Security Management Strategy Determine User Access Controls Levels Diagrams PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy to edit Organizational Assets Security Management Strategy Determine User Access Controls Levels Diagrams PDF can be your go to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.

Security Management Plan Steps In Detail Adopting Access Controls Microsoft PDF
This slide provides information about the fifth step in security management plan that must be implemented by the company and IT security manager in order to solve potential insider threats, external security breaches and reduce the risk of CaaS i.e. Adopting Access Controls. Deliver an awe inspiring pitch with this creative security management plan steps in detail adopting access controls microsoft pdf bundle. Topics like implementation costs, security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Control Access To Private Content Ppt PowerPoint Presentation Portfolio Outfit
This is a control access to private content ppt powerpoint presentation portfolio outfit. This is a three stage process. The stages in this process are access rights, access management, business.

Execution Of ICT Strategic Plan Key Access Security Control Models Topics PDF
This slide represents key access security control models for organizations. It includes discretionary access control, mandatory access control, role-based access control and attributes based access control, Do you know about Slidesgeeks Execution Of ICT Strategic Plan Key Access Security Control Models Topics PDF These are perfect for delivering any kind od presentation. Using it, create PowerPoint presentations that communicate your ideas and engage audiences. Save time and effort by using our pre designed presentation templates that are perfect for a wide range of topic. Our vast selection of designs covers a range of styles, from creative to business, and are all highly customizable and easy to edit. Download as a PowerPoint template or use them as Google Slides themes.

Security Control Laptop Access Ppt PowerPoint Presentation Complete Deck With Slides
If designing a presentation takes a lot of your time and resources and you are looking for a better alternative, then this security control laptop access ppt powerpoint presentation complete deck with slides is the right fit for you. This is a prefabricated set that can help you deliver a great presentation on the topic. All the eleven slides included in this sample template can be used to present a birds-eye view of the topic. These slides are also fully editable, giving you enough freedom to add specific details to make this layout more suited to your business setting. Apart from the content, all other elements like color, design, theme are also replaceable and editable. This helps in designing a variety of presentations with a single layout. Not only this, you can use this PPT design in formats like PDF, PNG, and JPG once downloaded. Therefore, without any further ado, download and utilize this sample presentation as per your liking.

Leveraging Openai API For Business Rate Limits For Controlling User Access Pictures PDF
This slide showcases rate limits for ChatGPT and ChatGPT-4 which will enforce users to utilize application programming interface APIs abilities in controlled manner. It provides details about tokens per minute and requests per minute. There are so many reasons you need a Leveraging Openai API For Business Rate Limits For Controlling User Access Pictures PDF. The first reason is you cannot spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
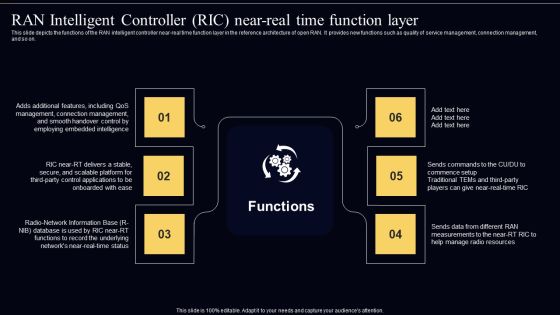
Open Radio Access Network IT RAN Intelligent Controller RIC Near Real Time Function Layer Professional PDF
This slide depicts the functions of the RAN intelligent controller near-real time function layer in the reference architecture of open RAN. It provides new functions such as quality of service management, connection management, and so on. This modern and well arranged Open Radio Access Network IT RAN Intelligent Controller RIC Near Real Time Function Layer Professional PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.
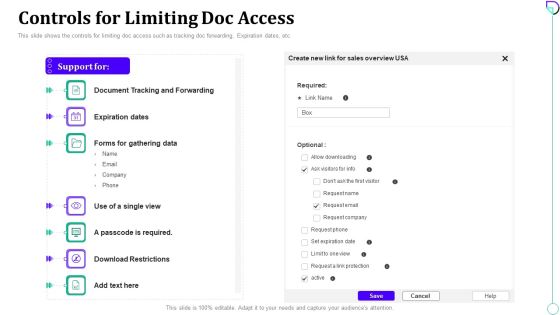
Docsend Capital Fundraising Controls For Limiting Doc Access Ppt Inspiration Smartart PDF
This slide shows the controls for limiting doc access such as tracking doc forwarding, Expiration dates, etc. Deliver an awe inspiring pitch with this creative docsend capital fundraising controls for limiting doc access ppt inspiration smartart pdf bundle. Topics like controls for limiting doc access can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
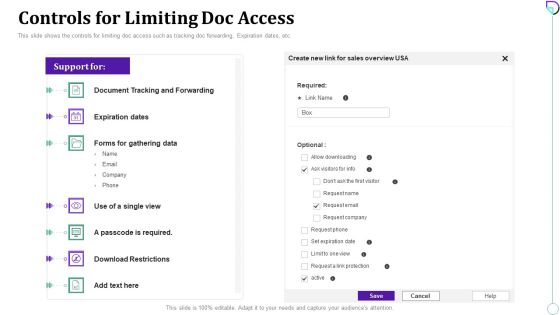
Docsend Capital Raising Pitch Deck Controls For Limiting Doc Access Themes PDF
This slide shows the controls for limiting doc access such as tracking doc forwarding, Expiration dates, etc.Deliver an awe inspiring pitch with this creative Docsend Capital Raising Pitch Deck Controls For Limiting Doc Access Themes PDF bundle. Topics like Expiration Dates, Passcode Required, Download Restrictions can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Access Management Powerpoint Slide Themes
This is a access management powerpoint slide themes. This is a five stage process. The stages in this process are access management, service desk, technical management, it operations management, application management.

Data Access Timeline Ppt Slides
This is a data access timeline ppt slides. This is a five stage process. The stages in this process are data access, customer report, model building and evaluation, problem definition, external applications.

Case Management Database Access Model Download PDF
This slide represents the overview of the case management data access model. The purpose of this slide is to showcase how different departments can access shared data. The components of the data access model include a case manager, employee, and business departments. The slide also comprises the data access process within an organization and the data type. Showcasing this set of slides titled Case Management Database Access Model Download PDF. The topics addressed in these templates are Data Access, Example, Data Type. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
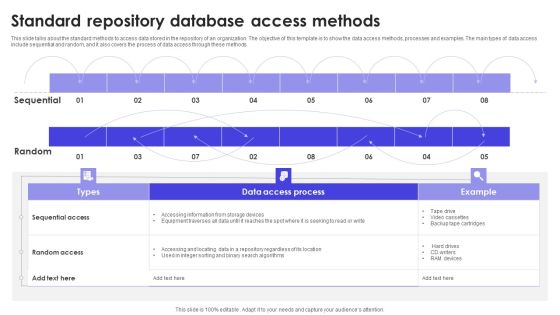
Standard Repository Database Access Methods Formats PDF
This slide talks about the standard methods to access data stored in the repository of an organization. The objective of this template is to show the data access methods, processes and examples. The main types of data access include sequential and random, and it also covers the process of data access through these methods. Pitch your topic with ease and precision using this Standard Repository Database Access Methods Formats PDF. This layout presents information on Sequential, Random, Methods. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
Increasing Speed Access Knowledge Ppt Sample
This is a increasing speed access knowledge ppt sample. This is a four stage process. The stages in this process are increasing speed access knowledge, reducing communication costs, increasing satisfaction of suppliers, partner and external experts.

Easy Access To Distribution Channels Ppt Slides
This is an easy access to distribution channels ppt slides. This is a four stage process. The stages in this process are industry overview, easy access to distribution channels, low initial capital investment, lower consumer switching costs.

Access Of Distribution Channels Ppt Slide Design
This is a access of distribution channels ppt slide design. This is a four stage process. The stages in this process are brand identity, economies of scale, access of distribution channels, product differentiation.

Database Access Layer Optimization Benefits Slides PDF
This slide depicts the advantages of data access layer optimization. The objective of this template is to represent the data access layer benefits and its model. The benefits include improved self-service data access, decreased ownership costs, faster reports generation, advanced querying and model building, and better access to open-source capabilities. Presenting Database Access Layer Optimization Benefits Slides PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Benefits, Lower Ownership Costs, Faster Reporting. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Internet Access Worldwide Template Powerpoint Templates
This is a internet access worldwide template powerpoint templates. This is a four stage process. The stages in this process are information, technology, innovation, foundation.

Analytical Access Example Sample Presentation Ppt
This is a analytical access example sample presentation ppt. This is a four stage process. The stages in this process are hypothesis, collect facts, optimize, measure.

Inventory Management Access Diagram Powerpoint Themes
This is a inventory management access diagram powerpoint themes. This is a eight stage process. The stages in this process are product inventory, product sales, physical inventory, store manager, engage, measure, accounting manager, supplier manager.

System Access Benefits Ppt PowerPoint Presentation Visuals
This is a system access benefits ppt powerpoint presentation visuals. This is a one stage process. The stages in this process are for human resource management, for operation management, for goal and target setting.
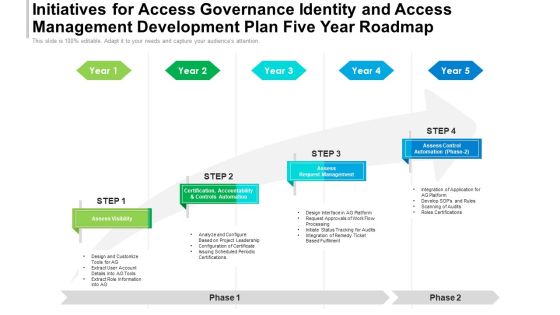
Initiatives For Access Governance Identity And Access Management Development Plan Five Year Roadmap Themes
We present our initiatives for access governance identity and access management development plan five year roadmap themes. This PowerPoint layout is easy-to-edit so you can change the font size, font type, color, and shape conveniently. In addition to this, the PowerPoint layout is Google Slides compatible, so you can share it with your audience and give them access to edit it. Therefore, download and save this well-researched initiatives for access governance identity and access management development plan five year roadmap themes in different formats like PDF, PNG, and JPG to smoothly execute your business plan.
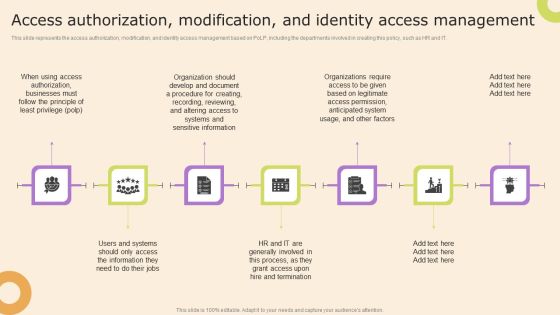
Information Technology Policy And Processes Access Authorization Modification And Identity Access Themes PDF
This slide represents the access authorization, modification, and identity access management based on PoLP, including the departments involved in creating this policy, such as HR and IT. Create an editable Information Technology Policy And Processes Access Authorization Modification And Identity Access Themes PDF that communicates your idea and engages your audience. Whether youre presenting a business or an educational presentation, pre designed presentation templates help save time. Information Technology Policy And Processes Access Authorization Modification And Identity Access Themes PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
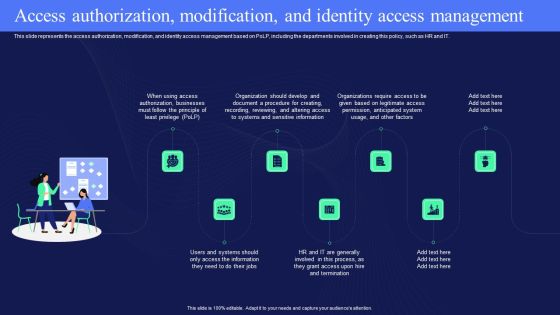
IT Policies And Procedures Access Authorization Modification And Identity Access Topics PDF
This slide represents the access authorization, modification, and identity access management based on PoLP, including the departments involved in creating this policy, such as HR and IT. Boost your pitch with our creative IT Policies And Procedures Access Authorization Modification And Identity Access Topics PDF. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you dont have to invest time in any additional work. Just grab the template now and use them.
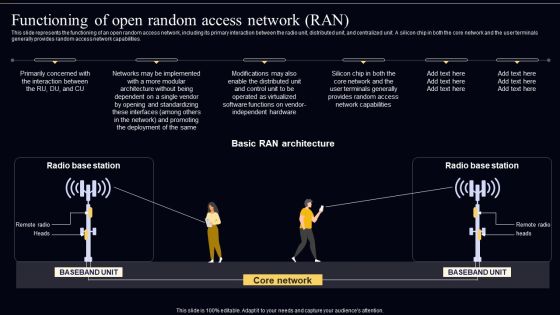
Open Radio Access Network IT Functioning Of Open Random Access Network RAN Sample PDF
This slide represents the functioning of an open random access network, including its primary interaction between the radio unit, distributed unit, and centralized unit. A silicon chip in both the core network and the user terminals generally provides random access network capabilities. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our Open Radio Access Network IT Functioning Of Open Random Access Network RAN Sample PDF was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into Open Radio Access Network IT Functioning Of Open Random Access Network RAN Sample PDF.

Cybersecurity Guidelines IT Access Authorization Modification And Identity Access Inspiration PDF
This slide represents the access authorization, modification, and identity access management based on polp, including the departments involved in creating this policy, such as HR and IT. Boost your pitch with our creative Cybersecurity Guidelines IT Access Authorization Modification And Identity Access Inspiration PDF. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.

Initiatives For Access Governance Identity And Access Management Development Plan Four Quarter Roadmap Guidelines
Presenting our innovatively-structured initiatives for access governance identity and access management development plan four quarter roadmap guidelines Template. Showcase your roadmap process in different formats like PDF, PNG, and JPG by clicking the download button below. This PPT design is available in both Standard Screen and Widescreen aspect ratios. It can also be easily personalized and presented with modified font size, font type, color, and shapes to measure your progress in a clear way.
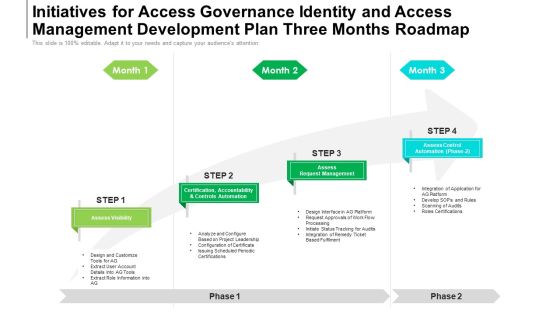
Initiatives For Access Governance Identity And Access Management Development Plan Three Months Roadmap Slides
Presenting our jaw-dropping initiatives for access governance identity and access management development plan three months roadmap slides. You can alternate the color, font size, font type, and shapes of this PPT layout according to your strategic process. This PPT presentation is compatible with Google Slides and is available in both standard screen and widescreen aspect ratios. You can also download this well-researched PowerPoint template design in different formats like PDF, JPG, and PNG. So utilize this visually-appealing design by clicking the download button given below.
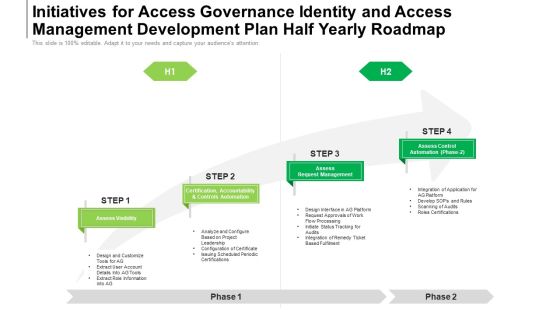
Initiatives For Access Governance Identity And Access Management Development Plan Half Yearly Roadmap Graphics
Introducing our initiatives for access governance identity and access management development plan half yearly roadmap graphics. This PPT presentation is Google Slides compatible, therefore, you can share it easily with the collaborators for measuring the progress. Also, the presentation is available in both standard screen and widescreen aspect ratios. So edit the template design by modifying the font size, font type, color, and shapes as per your requirements. As this PPT design is fully editable it can be presented in PDF, JPG and PNG formats.

Initiatives For Access Governance Identity And Access Management Development Plan Six Months Roadmap Rules
Presenting the initiatives for access governance identity and access management development plan six months roadmap rules. The template includes a roadmap that can be used to initiate a strategic plan. Not only this, the PowerPoint slideshow is completely editable and you can effortlessly modify the font size, font type, and shapes according to your needs. This PPT slide can be easily reached in standard screen and widescreen aspect ratios. The set is also available in various formats like PDF, PNG, and JPG. So download and use it multiple times as per your knowledge.
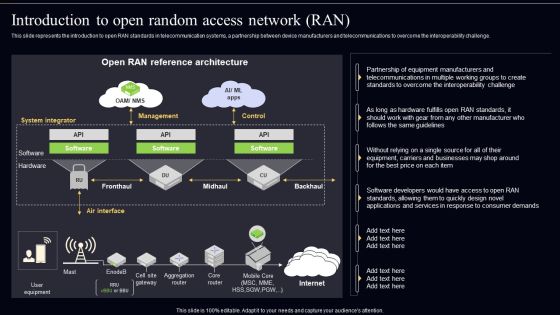
Open Radio Access Network IT Introduction To Open Random Access Network RAN Slides PDF
This slide represents the introduction to open RAN standards in telecommunication systems, a partnership between device manufacturers and telecommunications to overcome the interoperability challenge. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Open Radio Access Network IT Introduction To Open Random Access Network RAN Slides PDF to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.

Zero Trust Network Access Ztna Introduction Ppt Slide PDF
This slide represents the overview of zero trust network access, including its architecture. The purpose of this slide is to demonstrate the overview and use cases of ZTNA. The primary use cases include authentication and access control and holistic control and visibility. Slidegeeks has constructed Zero Trust Network Access Ztna Introduction Ppt Slide PDF after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping off point to explore our content and will give new users an insight into our top notch PowerPoint Templates.

Strategies For Successful Database Access Governance Program Infographics PDF
This slide outlines the strategies for an effective data access governance program. The purpose of this slide is to demonstrate the techniques for adequate data access. The steps include discovering and segmenting sensitive data, assigning access controls, monitoring user behavior, and rechecking compliance requirements. Pitch your topic with ease and precision using this Strategies For Successful Database Access Governance Program Infographics PDF. This layout presents information on Steps, Description, Impact . It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
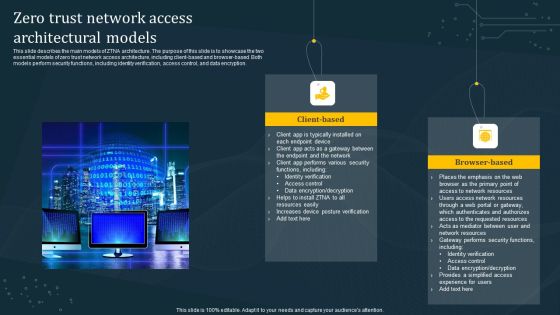
Zero Trust Network Access Architectural Models Diagrams PDF
This slide describes the main models of ZTNA architecture. The purpose of this slide is to showcase the two essential models of zero trust network access architecture, including client-based and browser-based. Both models perform security functions, including identity verification, access control, and data encryption. Are you searching for a Zero Trust Network Access Architectural Models Diagrams PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Zero Trust Network Access Architectural Models Diagrams PDF from Slidegeeks today.

Features Of Zero Trust Network Access Security Model Sample PDF
This slide represents the main features of ZTNA. The purpose of this slide is to showcase the various features of zero trust network access, including safeguarding private apps, connecting security controls to apps more closely, restriction of access, recognizing internal app use, and so on. Explore a selection of the finest Features Of Zero Trust Network Access Security Model Sample PDF here. With a plethora of professionally designed and pre-made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Features Of Zero Trust Network Access Security Model Sample PDF to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.

Benefits Of Zero Trust Network Access ZTNA Download PDF
This slide represents the benefits of zero trust network access, a component of SASE technology. The purpose of this slide is to demonstrate the multiple benefits of ZTNA to businesses and users. It also caters to the security benefits such as increased control and visibility, invisible infrastructure, and simple app segmentation. Present like a pro with Benefits Of Zero Trust Network Access ZTNA Download PDF Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
Identify And Access Management Technique Model Icons PDF
This slide shows controls management model for designing IAM strategy. The purpose of this slide is to highlight important phases with concerned stages for IAM strategy. It include phases such as prepare, develop and deliver , etc. Persuade your audience using this Identify And Access Management Technique Model Icons PDF. This PPT design covers six stages, thus making it a great tool to use. It also caters to a variety of topics including Prepare, Develop, Deliver. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Access Form Templates Ppt PowerPoint Presentation Layouts Sample Cpb
This is a access form templates ppt powerpoint presentation layouts sample cpb. This is a four stage process. The stages in this process are access form templates.

Complete Data Easy Access To Data Ppt Example
This is a complete data easy access to data ppt example. This is a four stage process. The stages in this process are trust data, complete data, easy access to data, intuitive tools.

House Training Program Custom Access Ppt PowerPoint Presentation Show Visuals
This is a house training program custom access ppt powerpoint presentation show visuals. This is a six stage process. The stages in this process are house training program, custom access.

Types Of Database Access Sharing Rules Slides PDF
This slide represents the overview of the case management data access model. The purpose of this slide is to showcase how different departments can access shared data. The components of the data access model include a case manager, employee, and business departments. The slide also comprises the data access process within an organization and the data type. Showcasing this set of slides titled Types Of Database Access Sharing Rules Slides PDF. The topics addressed in these templates are Public Groups, Role Hierarchy, Permission Sets. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Steps To Create Database Access Layer Slides PDF
This slide outlines the guidelines for creating a data access layer for an organizational structure. The objective of this slide is to demonstrate the data access layer creation phases. The key steps include creating the design, designing data access components, designing data helper components, and designing service agents. Showcasing this set of slides titled Steps To Create Database Access Layer Slides PDF. The topics addressed in these templates are Data Access Components, Create Design, Steps. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
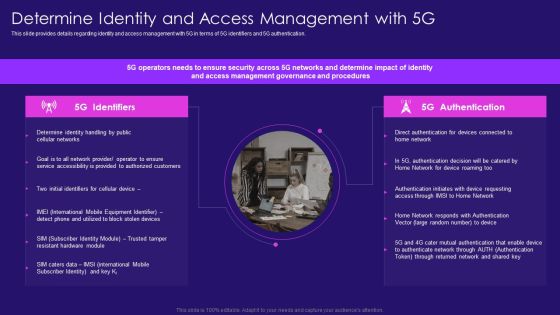
Determine Identity And Access Management With 5G Information PDF
This slide provides details regarding identity and access management with 5G in terms of 5G identifiers and 5G authentication. Deliver an awe inspiring pitch with this creative Determine Identity And Access Management With 5G Information PDF bundle. Topics like Determine Identity, Accessibility Provided, Identifiers Cellular can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Identity And Access Management Sample Diagram Powerpoint Slide Information
This is a identity and access management sample diagram powerpoint slide information. This is a two stage process. The stages in this process are governance, provisioning, sso.

Identity And Access Management Sample Diagram Ppt Slides
This is a identity and access management sample diagram ppt slides. This is a nine stage process. The stages in this process are auditors, itsm change management, end users and key users, identity and access administrators, administrators owners, legacy, cloud, sap, ad.

Steps For Document Lifecycle With Manage And Access Template PDF
Presenting steps for document lifecycle with manage and access template pdf. to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including capture, categorize, manage, access. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
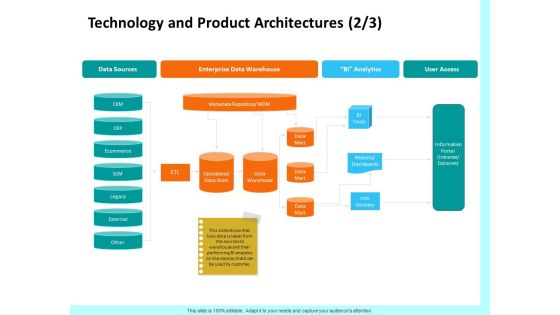
Firm Productivity Administration Technology And Product Architectures Access Background PDF
Presenting this set of slides with name firm productivity administration technology and product architectures access background pdf. This is a one stage process. The stages in this process are data sources, enterprise data warehouse, bi analytics, user access, crm, erp, ecommerce, scm. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
Icon For Server Database Access Management Background PDF
Persuade your audience using this Icon For Server Database Access Management Background PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Server Database, Access, Management. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Cloud Based Identify And Access Management Technique Introduction PDF
Presenting Cloud Based Identify And Access Management Technique Introduction PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Cloud Based Identify, Access Management, Technique. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Identify And Access Management Technique Icon Information PDF
Showcasing this set of slides titled Identify And Access Management Technique Icon Information PDF. The topics addressed in these templates are Identify, Access Management, Technique. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
Identify And Access Management Technique Mechanism Icon Information PDF
Persuade your audience using this Identify And Access Management Technique Mechanism Icon Information PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Identify, Access Management, Technique Mechanism. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Market Access With Arrow Icon Ppt PowerPoint Presentation File Smartart
Presenting this set of slides with name market access with arrow icon ppt powerpoint presentation file smartart. This is a one stage process. The stage in this process is market access with arrow icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
Zero Trust Network Access Architecture Overview Icons PDF
This slide gives an overview of zero trust network access architecture. The purpose of this slide is to showcase the ZTNA architecture and its benefits, covering granting safe and fast access, protecting reliable remote access, protecting sensitive data and apps, stopping insider threats, and so on. Retrieve professionally designed Zero Trust Network Access Architecture Overview Icons PDF to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.

Memcache Technology IT Limit Ip Access With Firewalls Pictures PDF
This slide explains how IP access is limited with firewalls, including setting up firewall rules to limit the computers. This is a memcache technology it limit ip access with firewalls pictures pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like limit ip access with firewalls. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
System Access To Management Ppt PowerPoint Presentation Topics
This is a system access to management ppt powerpoint presentation topics. This is a five stage process. The stages in this process are business, management, analysis, strategy, success, process.

Identity Access Management Lifecycle Ppt Powerpoint Slide Presentation Guidelines
This is a identity access management lifecycle ppt powerpoint slide presentation guidelines. This is a five stage process. The stages in this process are relationship begins, provisioning, authentication, authorization, self service, compliance, deprovisioning, password management, relationship ends.
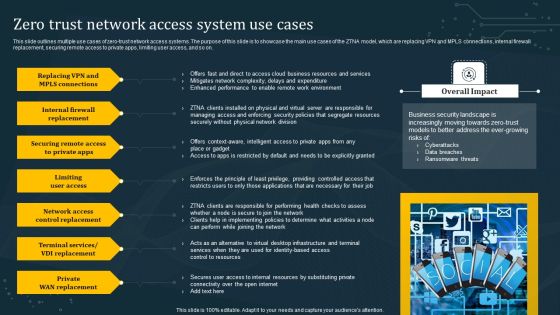
Zero Trust Network Access System Use Cases Summary PDF
This slide outlines multiple use cases of zero-trust network access systems. The purpose of this slide is to showcase the main use cases of the ZTNA model, which are replacing VPN and MPLS connections, internal firewall replacement, securing remote access to private apps, limiting user access, and so on. Boost your pitch with our creative Zero Trust Network Access System Use Cases Summary PDF. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.

Difference Identity Access Management Ppt PowerPoint Presentation Outline Introduction Cpb
Presenting this set of slides with name difference identity access management ppt powerpoint presentation outline introduction cpb. This is an editable Powerpoint five stages graphic that deals with topics like difference identity access management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Ethical Hacking Phase 3 Gaining Access Ppt Pictures Vector PDF
This slide represents the gaining access phase of ethical hacking and how access can be gained through a phishing attack, man in the middle, brute force attack, and so on. This is a ethical hacking phase 3 gaining access ppt pictures vector pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like system, required. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Parallel Computing Processing Introduction To Switched Memory Access Icons PDF
This slide represents the introduction to switched memory access, and a crossbar switch is installed to connect processors. Processors use shared memory in blocks, and connections between processors are made through a crossbar switch. Deliver and pitch your topic in the best possible manner with this Parallel Computing Processing Introduction To Switched Memory Access Icons PDF. Use them to share invaluable insights on Introduction To Switched, Memory Access and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Critical Principles Of Zero Trust Network Access Model Graphics PDF
This slide illustrates the key principles of zero trust network access model, including their impact. The purpose of this slide is to highlight the primary principles of the ZTNA model, including least privilege access, micro-segmentation, MFA, device validation, and monitoring everything. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Critical Principles Of Zero Trust Network Access Model Graphics PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Critical Principles Of Zero Trust Network Access Model Graphics PDF that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers
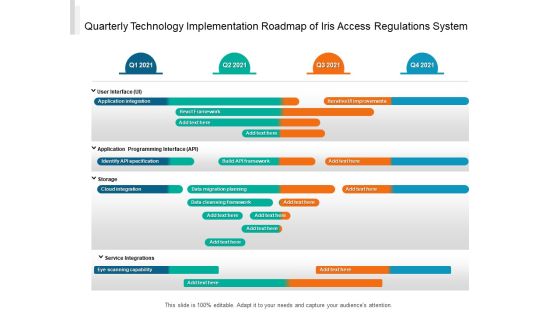
Quarterly Technology Implementation Roadmap Of Iris Access Regulations System Topics
We present our quarterly technology implementation roadmap of iris access regulations system topics. This PowerPoint layout is easy to edit so you can change the font size, font type, color, and shape conveniently. In addition to this, the PowerPoint layout is Google Slides compatible, so you can share it with your audience and give them access to edit it. Therefore, download and save this well researched quarterly technology implementation roadmap of iris access regulations system topics in different formats like PDF, PNG, and JPG to smoothly execute your business plan.

Addressing 5G Era Spectrum Bands Access And Pricing Clipart PDF
This slide provides details regarding various 5G era spectrum in terms of 5G spectrum bands, spectrum access and spectrum pricing. This is a Addressing 5G Era Spectrum Bands Access And Pricing Clipart PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Spectrum Bands, Spectrum Access, Spectrum Pricing. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Data Access Systems Ppt PowerPoint Presentation Layouts Gridlines Cpb
Presenting this set of slides with name data access systems ppt powerpoint presentation layouts gridlines cpb. This is an editable Powerpoint eight stages graphic that deals with topics like data access systems to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
User Access Provisioning Process Ppt PowerPoint Presentation Portfolio Layouts Cpb
Presenting this set of slides with name user access provisioning process ppt powerpoint presentation portfolio layouts cpb. This is an editable Powerpoint four stages graphic that deals with topics like user access provisioning process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Access Review Process Ppt PowerPoint Presentation Show Graphic Images Cpb
Presenting this set of slides with name access review process ppt powerpoint presentation show graphic images cpb. This is an editable Powerpoint four stages graphic that deals with topics like access review process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Access Management Roles Responsibilities Ppt PowerPoint Presentation Ideas Example Cpb
Presenting this set of slides with name access management roles responsibilities ppt powerpoint presentation ideas example cpb. This is an editable Powerpoint three stages graphic that deals with topics like access management roles responsibilities to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Business Value Identity Access Management Ppt PowerPoint Presentation Summary Cpb
Presenting this set of slides with name business value identity access management ppt powerpoint presentation summary cpb. This is an editable Powerpoint three stages graphic that deals with topics like business value identity access management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Secure Access Management Ppt PowerPoint Presentation Pictures Layout Cpb Pdf
Presenting this set of slides with name secure access management ppt powerpoint presentation pictures layout cpb pdf. This is an editable Powerpoint five stages graphic that deals with topics like secure access management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Pillars Of Cloud Access Security Broker Ppt Show Background PDF
This slide represents the four major pillars of cloud access security broker. The purpose of this slide is to showcase the main pillars of implementing a cloud access security broker. The pillars include compliance, visibility, threat protection, and data security. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Pillars Of Cloud Access Security Broker Ppt Show Background PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable Pillars Of Cloud Access Security Broker Ppt Show Background PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.

Open Access Box With Gears Ppt PowerPoint Presentation Inspiration Demonstration
This is a open access box with gears ppt powerpoint presentation inspiration demonstration. This is a six stage process. The stages in this process are computer software, operating system, open source.

Open Access Collaborative Customizable Sharable Ppt PowerPoint Presentation File Backgrounds
This is a open access collaborative customizable sharable ppt powerpoint presentation file backgrounds. This is a seven stage process. The stages in this process are computer software, operating system, open source.

Benefits Access Management Ppt PowerPoint Presentation Professional Smartart Cpb
Presenting this set of slides with name benefits access management ppt powerpoint presentation professional smartart cpb. This is an editable Powerpoint four stages graphic that deals with topics like benefits access management to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Identity Access Management Framework Ppt PowerPoint Presentation Portfolio Summary Cpb
Presenting this set of slides with name identity access management framework ppt powerpoint presentation portfolio summary cpb. This is an editable Powerpoint four stages graphic that deals with topics like identity access management framework to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
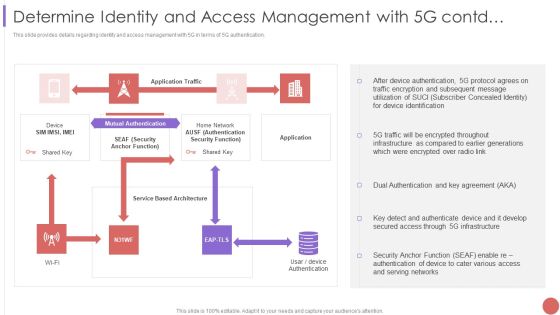
Determine Identity And Access Management With 5G Contd Structure PDF
This slide provides details regarding identity and access management with 5G in terms of 5G authentication. Deliver and pitch your topic in the best possible manner with this Determine Identity And Access Management With 5G Contd Structure PDF Use them to share invaluable insights on Mutual Authentication, Device Authentication, Traffic Encryption and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Determine Identity And Access Management With 5G Contd Information PDF
This slide provides details regarding identity and access management with 5G in terms of 5G authentication. Deliver and pitch your topic in the best possible manner with this Determine Identity And Access Management With 5G Contd Information PDF. Use them to share invaluable insights on Application Traffic, Security, Network and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Application Of AI For Database Access Governance Summary PDF
This slide represents the applications of artificial intelligence systems for data access governance. The purpose of this slide is to demonstrate the AI application in secure data access. The use cases include threat detection and prediction, system configuration, adaptability, data interpretation, and predictive forecasting. Presenting Application Of AI For Database Access Governance Summary PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Prediction, System Configuration, Adaptability. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Database Access Security Measures For Businesses Portrait PDF
This slide represents the security measures for data access within an organization. This template aims to demonstrate secure data access techniques and their benefits. The components include workforce training, implementing a data-centric security plan, deploying a multi-factor authentication policy, etc. Pitch your topic with ease and precision using this Database Access Security Measures For Businesses Portrait PDF. This layout presents information on Methods, Benefits, Actions. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Access Provisioning Lifecycle Ppt PowerPoint Presentation Show Cpb Pdf
Presenting this set of slides with name access provisioning lifecycle ppt powerpoint presentation show cpb pdf. This is an editable Powerpoint four stages graphic that deals with topics like access provisioning lifecycle to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Next Generation Access Ppt PowerPoint Presentation Portfolio Design Ideas Cpb
Presenting this set of slides with name next generation access ppt powerpoint presentation portfolio design ideas cpb. This is an editable Powerpoint six stages graphic that deals with topics like next generation access to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Maximizing Access To Public Information Availability Rules PDF
This slide represents maximizing access to public data availability such as increase data availability, default, public data disclosure, decision making, data quality and data governance. Presenting maximizing access to public information availability rules pdf to dispense important information. This template comprises seven stages. It also presents valuable insights into the topics including data governance, data quality, decision making. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

User Access Provisioning Process Ppt PowerPoint Presentation Example Cpb
Presenting this set of slides with name user access provisioning process ppt powerpoint presentation example cpb. This is an editable Powerpoint three stages graphic that deals with topics like user access provisioning process to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Secure Access Lock Clipart Ppt PowerPoint Presentation Summary File Formats
This is a secure access lock clipart ppt powerpoint presentation summary file formats. This is a four stage process. The stages in this process are computer software, operating system, open source.
Secure Server Access Ppt PowerPoint Presentation Icon Show Cpb
Presenting this set of slides with name secure server access ppt powerpoint presentation icon show cpb. This is an editable Powerpoint four stages graphic that deals with topics like secure server access to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Enterprise Access Governance Ppt PowerPoint Presentation Model Mockup Cpb
Presenting this set of slides with name enterprise access governance ppt powerpoint presentation model mockup cpb. This is an editable Powerpoint four stages graphic that deals with topics like enterprise access governance to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Secure Data Access Ppt PowerPoint Presentation Inspiration Guidelines Cpb
Presenting this set of slides with name secure data access ppt powerpoint presentation inspiration guidelines cpb. This is an editable Powerpoint four stages graphic that deals with topics like secure data access to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Individual Access Security Ppt PowerPoint Presentation Design Ideas Cpb
Presenting this set of slides with name individual access security ppt powerpoint presentation design ideas cpb. This is an editable Powerpoint three stages graphic that deals with topics like individual access security to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Provider Access Ppt PowerPoint Presentation Summary Graphics Pictures Cpb Pdf
Presenting this set of slides with name provider access ppt powerpoint presentation summary graphics pictures cpb pdf. This is an editable Powerpoint six stages graphic that deals with topics like provider access to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Sensitive Access Analysis Ppt PowerPoint Presentation Styles Influencers Cpb Pdf
Presenting this set of slides with name sensitive access analysis ppt powerpoint presentation styles influencers cpb pdf. This is an editable Powerpoint six stages graphic that deals with topics like sensitive access analysis to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Access Database Replication Ppt PowerPoint Presentation Inspiration Show Cpb Pdf
Presenting this set of slides with name access database replication ppt powerpoint presentation inspiration show cpb pdf. This is an editable Powerpoint three stages graphic that deals with topics like access database replication to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.

Secure Database Access Methods For Cloud Computing Formats PDF
This slide describes the various methods to access the data stored in a cloud environment securely. The purpose of this slide is to represent secure data access for cloud computing users. The methods include cloud-based access through a relational database management system, cloud-based data warehousing and a cloud data lake. Persuade your audience using this Secure Database Access Methods For Cloud Computing Formats PDF. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including Cloud Data Lake, Data Warehousing, Cloud Service Provider. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Multiple Access Techniques Ppt PowerPoint Presentation Summary Portrait Cpb
Presenting this set of slides with name multiple access techniques ppt powerpoint presentation summary portrait cpb. This is an editable Powerpoint four stages graphic that deals with topics like multiple access techniques to help convey your message better graphically. This product is a premium product available for immediate download and is 100 percent editable in Powerpoint. Download this now and use it in your presentations to impress your audience.
Market Access Strategy Example Powerpoint Slide Background Picture
This is a market access strategy example powerpoint slide background picture. This is a four stage process. The stages in this process are resource allocation, market assessment, economic modelling, product assessment.

Main Pillars Of Zero Network Trust Access Sample PDF
This slide outlines the critical pillars of the zero network trust access model. The purpose of this slide is to showcase the primary pillars of ZTNA, including users, devices, networks, infrastructure, applications, data, visibility and analytics, and orchestration and automation. Presenting this PowerPoint presentation, titled Main Pillars Of Zero Network Trust Access Sample PDF, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Main Pillars Of Zero Network Trust Access Sample PDF. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Main Pillars Of Zero Network Trust Access Sample PDF that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.

Secure Access Service Edge Use Cases Ppt Outline Images PDF
This slide represents the use cases of secure access service edge within an organization. The purpose of this slide is to demonstrate the various use cases of the SASE model, including rapid response to network demand, support for IoT and edge computing, VPN replacement, performance assurance and so on. Explore a selection of the finest Secure Access Service Edge Use Cases Ppt Outline Images PDF here. With a plethora of professionally designed and pre made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Secure Access Service Edge Use Cases Ppt Outline Images PDF to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.

Training Program For Zero Trust Network Access Model Microsoft PDF
This slide outlines the training program for implementing the zero-trust network access model in the organization. The purpose of this slide is to highlight the training agenda, objectives, system requirements, mode of training and cost of the training. This Training Program For Zero Trust Network Access Model Microsoft PDF is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Training Program For Zero Trust Network Access Model Microsoft PDF features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today

Database Access Management Checklist For Businesses Formats PDF
This slide outlines the checklist for data access management in an organization. The purpose of this slide is to enlist all the crucial tasks and steps. The key points include creating an inventory, identifying data ownership and location of data, creating security groups, conducting regular data audits, and creating a certification program. Showcasing this set of slides titled Database Access Management Checklist For Businesses Formats PDF. The topics addressed in these templates are Description, Status, Comments. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Identification Access Lifecycle Framework Of IT Company Portrait PDF
This slide depicts identity identification lifecycle model of information technology IT company. It provides information about identity onboarding, identity management, account management, entitlement management and access management.Persuade your audience using this identification access lifecycle framework of it company portrait pdf This PPT design covers five stages, thus making it a great tool to use. It also caters to a variety of topics including identity onboarding, identity management, account management Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Key Pillars Of Identify And Access Management Technique Topics PDF
This slide shows main features of an effective IAM strategy. The purpose of this strategy is to highlight major components of IAM strategy. It include features such as provisioning identities, access security certification and security management , etc. Presenting Key Pillars Of Identify And Access Management Technique Topics PDF to dispense important information. This template comprises five stages. It also presents valuable insights into the topics including Provisioning Identities, Security Certification, Security Management. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Working Functions Of Zero Trust Network Access Architecture Introduction PDF
This slide gives an overview of the working features of zero trust network access architecture. The purpose of this slide is to highlight the various functions that ZTNA architecture performs, including identification, protection, detection and response to threats. Explore a selection of the finest Working Functions Of Zero Trust Network Access Architecture Introduction PDF here. With a plethora of professionally designed and pre-made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Working Functions Of Zero Trust Network Access Architecture Introduction PDF to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.

Zero Trust Network Access ZTNA Introduction Structure PDF
This slide represents the overview of zero trust network access, including its, benefits and principles. The purpose of this slide is to demonstrate the overview, principles and benefits of ZTNA. The primary benefits include seamless user experience, effortless scale, no need for legacy applications, etc. There are so many reasons you need a Zero Trust Network Access ZTNA Introduction Structure PDF. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.

Zero Trust Network Access User Flow Overview Mockup PDF
This slide describes the overview of zero trust network access user flow. The purpose of this slide is to showcase how the user moves into a network when the ZTNA security model is applied. The key components include a remote user, MFA, security policies, a cloud data center and a branch office. Create an editable Zero Trust Network Access User Flow Overview Mockup PDF that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. Zero Trust Network Access User Flow Overview Mockup PDF is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.
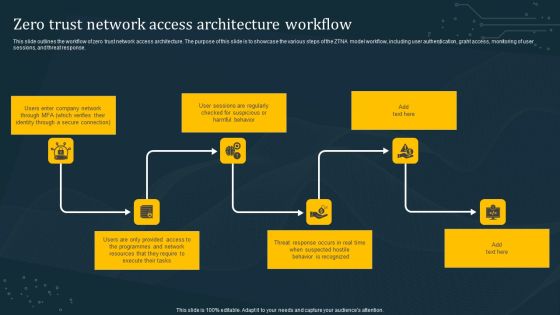
Zero Trust Network Access Architecture Workflow Microsoft PDF
This slide outlines the workflow of zero trust network access architecture. The purpose of this slide is to showcase the various steps of the ZTNA model workflow, including user authentication, grant access, monitoring of user sessions, and threat response. Slidegeeks has constructed Zero Trust Network Access Architecture Workflow Microsoft PDF after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.
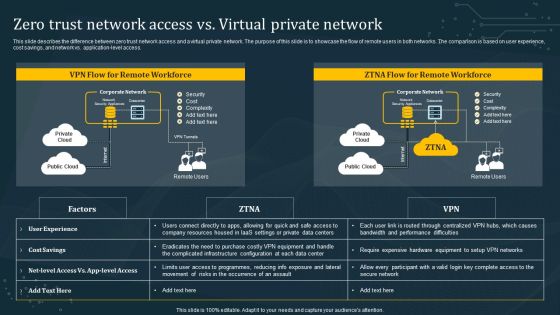
Zero Trust Network Access Vs Virtual Private Network Ideas PDF
This slide describes the difference between zero trust network access and a virtual private network. The purpose of this slide is to showcase the flow of remote users in both networks. The comparison is based on user experience, cost savings, and network vs. application-level access. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Zero Trust Network Access Vs Virtual Private Network Ideas PDF for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.

Challenges Of VPN Based Remote Access Solutions Template PDF
This slide outlines the limitations of virtual private network-based remote access services. The purpose of this slide is to showcase the various challenges of the VPN network system and how the zero trust network model can overcome those issues. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Challenges Of VPN Based Remote Access Solutions Template PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Challenges Of VPN Based Remote Access Solutions Template PDF today and make your presentation stand out from the rest

Ethical Hacking Phase 4 Maintaining Access Ppt Professional Grid PDF
This slide represents the maintaining access phase of ethical hacking and how ethical hackers take advantage of it to detect any malicious activities and prevent them. This is a ethical hacking phase 4 maintaining access ppt professional grid pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like system, information, determining. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Addressing 5G Era Spectrum Bands Access And Pricing Download PDF
This slide provides details regarding various 5G era spectrum in terms of 5G spectrum bands, spectrum access and spectrum pricing. Presenting Addressing 5G Era Spectrum Bands Access And Pricing Download PDF to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like Approved Spectrum, Globally Recognized, Operators To Revamp In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Zero Trust Network Access Implementation Challenges Rules PDF
This slide outlines the main challenges of ZTNA implementation. The purpose of this slide is to highlight the primary challenges that organizations face while deploying ZTNA. The challenges include continual management and maintenance, low productivity, security risks, and so on. Presenting this PowerPoint presentation, titled Zero Trust Network Access Implementation Challenges Rules PDF, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Zero Trust Network Access Implementation Challenges Rules PDF. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Zero Trust Network Access Implementation Challenges Rules PDF that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.

Cloud Storage Access Methods Ppt Model Maker PDF
This slide depicts the cloud storage access methods such as web service APIs Application Programming Interface, file based APIs, block-based APIs, and other APIs. This is a cloud storage access methods ppt model maker pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like service, network internet, implement. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Checklist To Build Zero Trust Network Access Architecture Diagrams PDF
This slide outlines the checklist to develop a zero-trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Checklist To Build Zero Trust Network Access Architecture Diagrams PDF can be your best option for delivering a presentation. Represent everything in detail using Checklist To Build Zero Trust Network Access Architecture Diagrams PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.
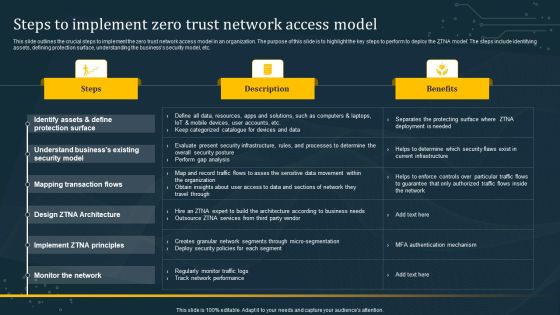
Steps To Implement Zero Trust Network Access Model Graphics PDF
This slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. If your project calls for a presentation, then Slidegeeks is your go-to partner because we have professionally designed, easy-to-edit templates that are perfect for any presentation. After downloading, you can easily edit Steps To Implement Zero Trust Network Access Model Graphics PDF and make the changes accordingly. You can rearrange slides or fill them with different images. Check out all the handy templates

 Home
Home