System Overview

Expansion Strategy Wireless Communication Services Provider Company Profile CP SS V
Mentioned slide outlines business expansion strategies for 5G and fiber network across the globe. It includes strategies such as setting network resiliency bar, connecting with people on the go, connecting first responders, and building a network for the future.Find highly impressive Expansion Strategy Wireless Communication Services Provider Company Profile CP SS V on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Expansion Strategy Wireless Communication Services Provider Company Profile CP SS V for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now

Employee Count Wind Turbines Manufacturer Company Profile CP SS V
The following slide outlines the number of employees of vestas company for five consecutive financial years i.e. From 2018 to 2022. It also showcases diversity and inclusion at workplace through women employees in board and executive management, women in leadership positions, etc.Present like a pro with Employee Count Wind Turbines Manufacturer Company Profile CP SS V. Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
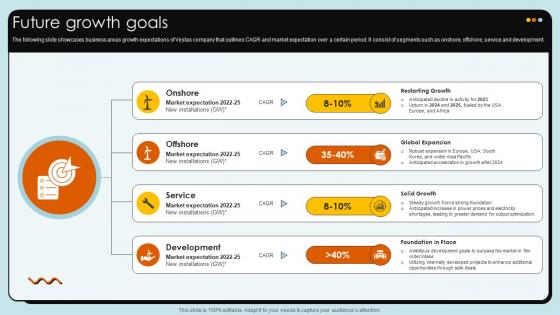
Future Growth Goals Wind Turbines Manufacturer Company Profile CP SS V
The following slide showcases business areas growth expectations of Vestas company that outlines CAGR and market expectation over a certain period. It consist of segments such as onshore, offshore, service and development.Whether you have daily or monthly meetings, a brilliant presentation is necessary. Future Growth Goals Wind Turbines Manufacturer Company Profile CP SS V can be your best option for delivering a presentation. Represent everything in detail using Future Growth Goals Wind Turbines Manufacturer Company Profile CP SS V and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.

Key Competitors Wind Turbines Manufacturer Company Profile CP SS V
The following slide outlines competitor businesses that operate in similar markets and serve a similar customer base as Vestas does. It showcases competitors such as Nordex, Envision Energy, Goldwind, GE Renewable Energy and Siemens Gamesa Renewable Energy.Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Key Competitors Wind Turbines Manufacturer Company Profile CP SS V template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Key Competitors Wind Turbines Manufacturer Company Profile CP SS V that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers

Net Revenue Wind Turbines Manufacturer Company Profile CP SS V
The slide showcases the total revenue gained by Vestas company for five consecutive years, i.e. from FY2018 to FY2022. It outlines the overall revenue attained through the sale of its products offering and services solutions.This Net Revenue Wind Turbines Manufacturer Company Profile CP SS V is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Net Revenue Wind Turbines Manufacturer Company Profile CP SS V features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today

Revenue By Region Wind Turbines Manufacturer Company Profile CP SS V
The slide showcases the total revenue gained in various operating regions of Vestas company for five consecutive years, i.e. from FY2018 to FY2022. It outlines the its geographical areas such as EMEA Europe, Middle East and Africa, Americas and Asia Pacific.Retrieve professionally designed Revenue By Region Wind Turbines Manufacturer Company Profile CP SS V to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You do not have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
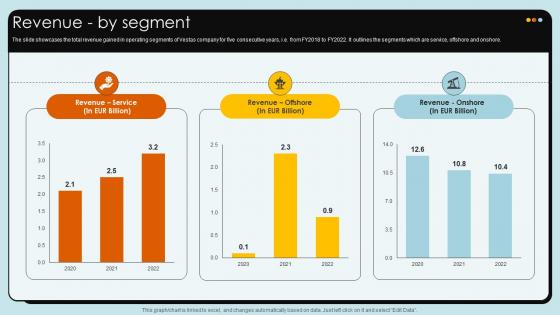
Revenue By Segment Wind Turbines Manufacturer Company Profile CP SS V
The slide showcases the total revenue gained in operating segments of Vestas company for five consecutive years, i.e. from FY2018 to FY2022. It outlines the segments which are service, offshore and onshore.Slidegeeks has constructed Revenue By Segment Wind Turbines Manufacturer Company Profile CP SS V after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.

How Generative AI Tools Work Ppt Powerpoint Presentation AI CD V

Wine Lounge Business Plan Powerpoint Presentation Slides BP V

Marketing Project Performance Benchmarking To Enhance Business Revenue CRP CD V
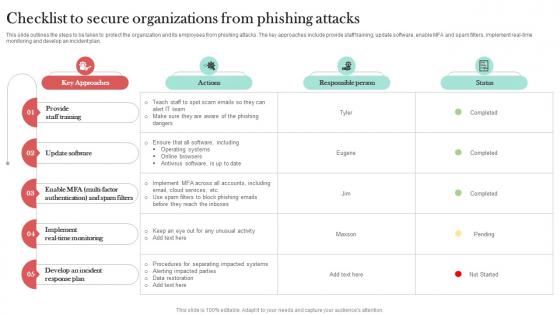
Checklist To Secure Organizations From Man In The Middle Phishing IT
This slide outlines the steps to be taken to protect the organization and its employees from phishing attacks. The key approaches include provide staff training, update software, enable MFA and spam filters, implement real-time monitoring and develop an incident plan. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Checklist To Secure Organizations From Man In The Middle Phishing IT template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Checklist To Secure Organizations From Man In The Middle Phishing IT that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers

Guidelines To Stay Safe From Phishing Scams Man In The Middle Phishing IT
This slide outlines the various preventive measures to stay safe from phishing attacks. These include know how to spot phishing scams, avoid clicking that link, install free anti-phishing extensions, change passwords regularly, install firewalls, never miss updates, etc. Explore a selection of the finest Guidelines To Stay Safe From Phishing Scams Man In The Middle Phishing IT here. With a plethora of professionally designed and pre-made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Guidelines To Stay Safe From Phishing Scams Man In The Middle Phishing IT to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.
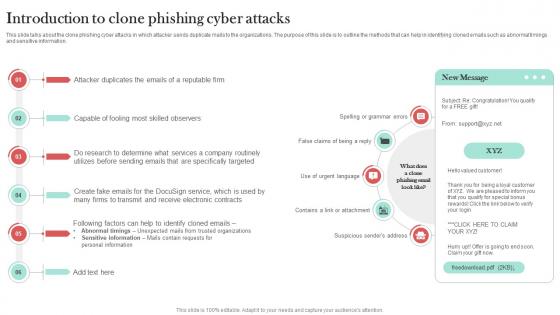
Introduction To Clone Phishing Cyber Man In The Middle Phishing IT
This slide talks about the clone phishing cyber attacks in which attacker sends duplicate mails to the organizations. The purpose of this slide is to outline the methods that can help in identifying cloned emails such as abnormal timings and sensitive information. This Introduction To Clone Phishing Cyber Man In The Middle Phishing IT from Slidegeeks makes it easy to present information on your topic with precision. It provides customization options, so you can make changes to the colors, design, graphics, or any other component to create a unique layout. It is also available for immediate download, so you can begin using it right away. Slidegeeks has done good research to ensure that you have everything you need to make your presentation stand out. Make a name out there for a brilliant performance.

Pharming Phishing Types And Prevention Man In The Middle Phishing IT
This slide demonstrates the different types pf pharming phishing scams. The primary types include malware-based pharming and DNS pharming. This slide also outlines the ways which helps to prevent a pharming attack such as verify the URL, install VPN, etc. Want to ace your presentation in front of a live audience Our Pharming Phishing Types And Prevention Man In The Middle Phishing IT can help you do that by engaging all the users towards you. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy-to-edit and downloadable. Use these for both personal and commercial use.
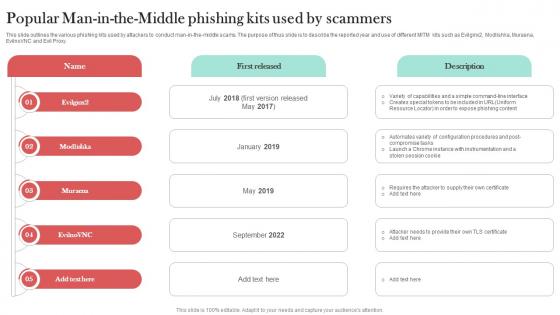
Popular Man In The Middle Phishing Kits Man In The Middle Phishing IT
This slide outlines the various phishing kits used by attackers to conduct man-in-the-middle scams. The purpose of thus slide is to describe the reported year and use of different MITM kits such as Evilginx2, Modlishka, Muraena, EvilnoVNC and Evil Proxy. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Popular Man In The Middle Phishing Kits Man In The Middle Phishing IT a try. Our experts have put a lot of knowledge and effort into creating this impeccable Popular Man In The Middle Phishing Kits Man In The Middle Phishing IT. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today

Preventive Measures For Man In The Middle Man In The Middle Phishing IT
This slide outlines the various methods of preventing man-in-the-middle cyber attacks. The purpose of this slide is to explain how users can protect themselves from MITM scams. These include secure connections, avoid phishing emails, endpoint security, etc. Get a simple yet stunning designed Preventive Measures For Man In The Middle Man In The Middle Phishing IT. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Preventive Measures For Man In The Middle Man In The Middle Phishing IT can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.

Preventive Measures To Avoid Watering Man In The Middle Phishing IT
This slide outlines the various preventive measures to avoid watering hole phishing attacks. The purpose of this slide is to help in protecting users from watering hole scams. The key steps include vulnerability scanning, security patches, input validation, etc. Present like a pro with Preventive Measures To Avoid Watering Man In The Middle Phishing IT. Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.

Primary Techniques Employed In Phishing Man In The Middle Phishing IT
This slide demonstrates the ways utilized by phishers to attack victims. The purpose of this slide is to outline the different methods used by attackers to trick victims. The primary means of attacks are text messages, emails and phone calls from unknown sources. Slidegeeks is here to make your presentations a breeze with Primary Techniques Employed In Phishing Man In The Middle Phishing IT With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first

Targeted Industries Of Cyber Phishing Man In The Middle Phishing IT
This slide represents the statistics of most targeted industries of phishing scams. The purpose of this slide is to outline the various sectors which are more prone to phishing attacks. These industries are retail, manufacturing, food and beverage, tech, etc. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Targeted Industries Of Cyber Phishing Man In The Middle Phishing IT to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.
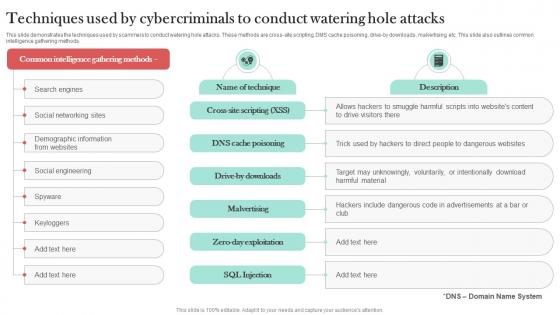
Techniques Used By Cybercriminals To Man In The Middle Phishing IT
This slide demonstrates the techniques used by scammers to conduct watering hole attacks. These methods are cross-site scripting, DMS cache poisoning, drive-by downloads, malvertising, etc. This slide also outlines common intelligence gathering methods. This modern and well-arranged Techniques Used By Cybercriminals To Man In The Middle Phishing IT provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint, no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.

Warning Signs To Recognize Phishing Email Man In The Middle Phishing IT
This slide talks about the warning signs that can help the user to recognize phishing email. The purpose of this slide is to outline the signs of phishing mails such as no greeting, misleading hyperlinks, unauthorized attachments, spelling and grammatical errors, etc. Slidegeeks has constructed Warning Signs To Recognize Phishing Email Man In The Middle Phishing IT after conducting extensive research and examination. These presentation templates are constantly being generated and modified based on user preferences and critiques from editors. Here, you will find the most attractive templates for a range of purposes while taking into account ratings and remarks from users regarding the content. This is an excellent jumping-off point to explore our content and will give new users an insight into our top-notch PowerPoint Templates.

Forecasts Ai Chatbot Service Market Entry Strategy
The slide outlines future projections showing the estimated growth of the B2B business for five years after launch. It assists businesses in determining the direction of future trends.Slidegeeks is here to make your presentations a breeze with Forecasts Ai Chatbot Service Market Entry Strategy With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first

Increasing Business Awareness With Insurance Marketing Strategies Strategy CD V

Smart Grid Working Ppt Powerpoint Presentation Complete Deck With Slides
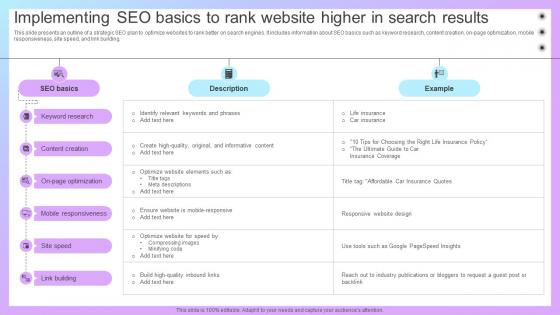
Increasing Business Awareness Implementing SEO Basics To Rank Website Higher Strategy SS V
This slide presents an outline of a strategic SEO plan to optimize websites to rank better on search engines. It includes information about SEO basics such as keyword research, content creation, on-page optimization, mobile responsiveness, site speed, and link building. This Increasing Business Awareness Implementing SEO Basics To Rank Website Higher Strategy SS V is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The Increasing Business Awareness Implementing SEO Basics To Rank Website Higher Strategy SS V features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today
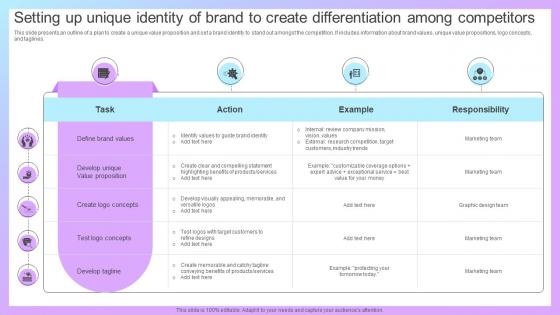
Increasing Business Awareness Setting Up Unique Identity Of Brand To Create Strategy SS V
This slide presents an outline of a plan to create a unique value proposition and set a brand identity to stand out amongst the competition. It includes information about brand values, unique value propositions, logo concepts, and taglines. If you are looking for a format to display your unique thoughts, then the professionally designed Increasing Business Awareness Setting Up Unique Identity Of Brand To Create Strategy SS V is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Increasing Business Awareness Setting Up Unique Identity Of Brand To Create Strategy SS V and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.

Increasing Business Awareness Social Media Marketing Campaign To Promote Strategy SS V
This slide outlines a social media marketing plan to advertise various insurance products online. It includes information about insurance product, goal, audience, delivery, call to action, content and message. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Increasing Business Awareness Social Media Marketing Campaign To Promote Strategy SS V and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.

Zero Trust Network Access Ppt Powerpoint Presentation Complete Deck With Slides

A50 Zero Trust Network Access Architecture Workflow
This slide outlines the workflow of zero trust network access architecture. The purpose of this slide is to showcase the various steps of the ZTNA model workflow, including user authentication, grant access, monitoring of user sessions, and threat response. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate A50 Zero Trust Network Access Architecture Workflow for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.

Zero Trust Network Access Before Vs After Zero Trust Network Access Implementation
This slide outlines the problems with the legacy virtual private network security model and how ZTNA can overcome those challenges. The purpose of this slide is to showcase the various VPN challenges and ZTNA solutions for those problems. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Zero Trust Network Access Before Vs After Zero Trust Network Access Implementation and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.
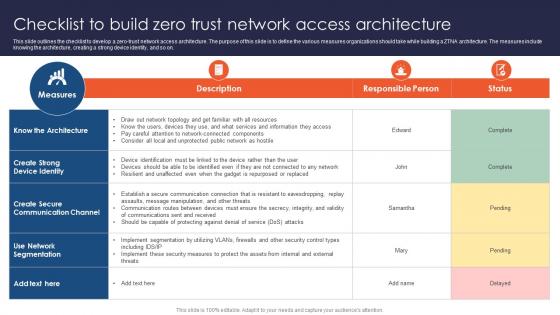
Zero Trust Network Access Checklist To Build Zero Trust Network Access Architecture
This slide outlines the checklist to develop a zero-trust network access architecture. The purpose of this slide is to define the various measures organizations should take while building a ZTNA architecture. The measures include knowing the architecture, creating a strong device identity, and so on. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Zero Trust Network Access Checklist To Build Zero Trust Network Access Architecture to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.

Zero Trust Network Access Future And Emerging Trends In ZTNA Model
This slide outlines the future outlook and emerging trends in the zero trust network architecture model. The purpose of this slide is to showcase the various emerging future trends in the ZTNA model, including artificial intelligence, SASE, edge computing, the Internet of Things, and so on. Presenting this PowerPoint presentation, titled Zero Trust Network Access Future And Emerging Trends In ZTNA Model, with topics curated by our researchers after extensive research. This editable presentation is available for immediate download and provides attractive features when used. Download now and captivate your audience. Presenting this Zero Trust Network Access Future And Emerging Trends In ZTNA Model. Our researchers have carefully researched and created these slides with all aspects taken into consideration. This is a completely customizable Zero Trust Network Access Future And Emerging Trends In ZTNA Model that is available for immediate downloading. Download now and make an impact on your audience. Highlight the attractive features available with our PPTs.
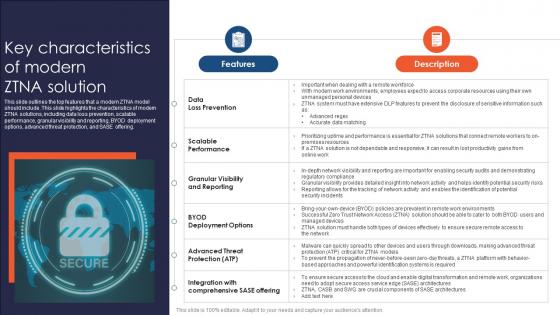
Zero Trust Network Access Key Characteristics Of Modern ZTNA Solution
This slide outlines the top features that a modern ZTNA model should include. This slide highlights the characteristics of modern ZTNA solutions, including data loss prevention, scalable performance, granular visibility and reporting, BYOD deployment options, advanced threat protection, and SASE offering. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye-catching visual experience. Download Zero Trust Network Access Key Characteristics Of Modern ZTNA Solution to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high-quality content for you. Later on, you can personalize the content by editing the Zero Trust Network Access Key Characteristics Of Modern ZTNA Solution.

Zero Trust Network Access Main Pillars Of Zero Network Trust Access
This slide outlines the critical pillars of the zero network trust access model. The purpose of this slide is to showcase the primary pillars of ZTNA, including users, devices, networks, infrastructure, applications, data, visibility and analytics, and orchestration and automation. Do you know about Slidesgeeks Zero Trust Network Access Main Pillars Of Zero Network Trust Access These are perfect for delivering any kind od presentation. Using it, create PowerPoint presentations that communicate your ideas and engage audiences. Save time and effort by using our pre-designed presentation templates that are perfect for a wide range of topic. Our vast selection of designs covers a range of styles, from creative to business, and are all highly customizable and easy to edit. Download as a PowerPoint template or use them as Google Slides themes.
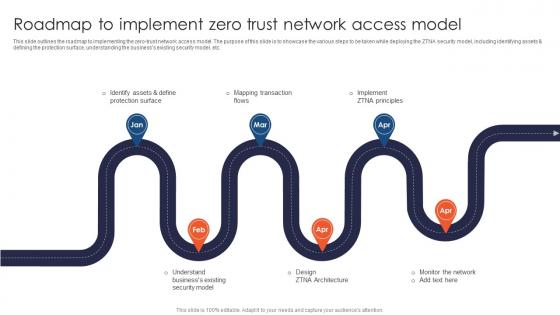
Zero Trust Network Access Roadmap To Implement Zero Trust Network Access Model

Zero Trust Network Access Steps To Implement Zero Trust Network Access Model
This slide outlines the crucial steps to implement the zero trust network access model in an organization. The purpose of this slide is to highlight the key steps to perform to deploy the ZTNA model. The steps include identifying assets, defining protection surface, understanding the businesss security model, etc. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Zero Trust Network Access Steps To Implement Zero Trust Network Access Model template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Zero Trust Network Access Steps To Implement Zero Trust Network Access Model that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers
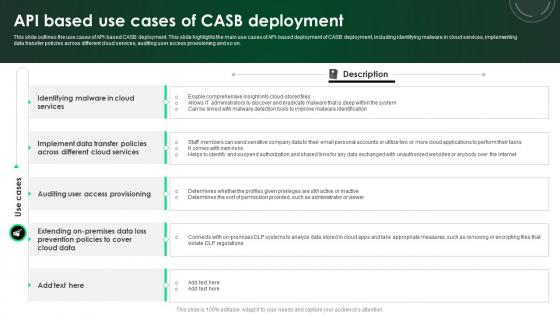
CASB 2 0 IT API Based Use Cases Of CASB Deployment
This slide outlines the use cases of API-based CASB deployment. This slide highlights the main use cases of API-based deployment of CASB deployment, including identifying malware in cloud services, implementing data transfer policies across different cloud services, auditing user access provisioning and so on. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate CASB 2 0 IT API Based Use Cases Of CASB Deployment for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
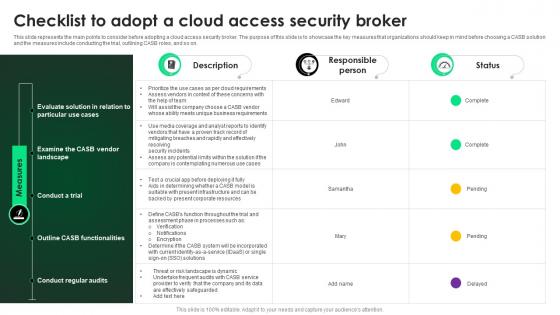
CASB 2 0 IT Checklist To Adopt A Cloud Access Security Broker
This slide represents the main points to consider before adopting a cloud access security broker. The purpose of this slide is to showcase the key measures that organizations should keep in mind before choosing a CASB solution and the measures include conducting the trial, outlining CASB roles, and so on. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward CASB 2 0 IT Checklist To Adopt A Cloud Access Security Broker template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal CASB 2 0 IT Checklist To Adopt A Cloud Access Security Broker that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers.
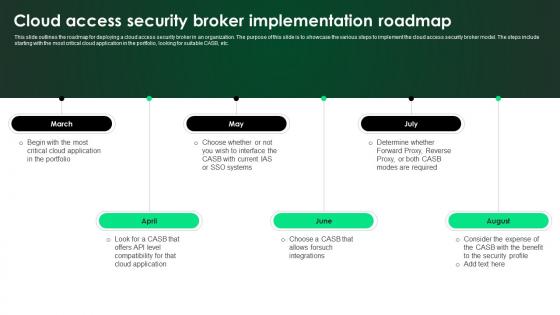
CASB 2 0 IT Cloud Access Security Broker Implementation Roadmap
This slide outlines the roadmap for deploying a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to implement the cloud access security broker model. The steps include starting with the most critical cloud application in the portfolio, looking for suitable CASB, etc. Welcome to our selection of the CASB 2 0 IT Cloud Access Security Broker Implementation Roadmap. These are designed to help you showcase your creativity and bring your sphere to life. Planning and Innovation are essential for any business that is just starting out. This collection contains the designs that you need for your everyday presentations. All of our PowerPoints are 100Percent editable, so you can customize them to suit your needs. This multi-purpose template can be used in various situations. Grab these presentation templates today.
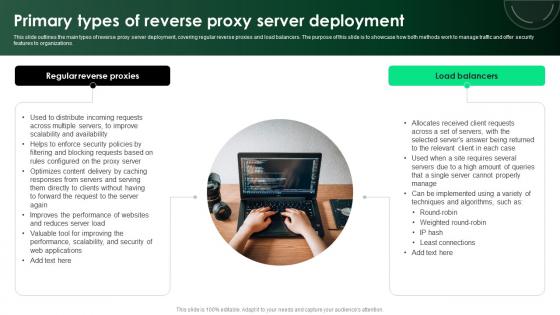
CASB 2 0 IT Primary Types Of Reverse Proxy Server Deployment
This slide outlines the main types of reverse proxy server deployment, covering regular reverse proxies and load balancers. The purpose of this slide is to showcase how both methods work to manage traffic and offer security features to organizations. Present like a pro with CASB 2 0 IT Primary Types Of Reverse Proxy Server Deployment. Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.

CASB 2 0 IT Pros And Cons Of API Scanning CASB Deployment
This slide outlines the advantages and disadvantages of the API scanning cloud access security broker deployment model. This slide aims to highlight the pros and cons of the API scanning deployment model and the benefits include no impact on user experience, taking only a few hours to configure, etc. Slidegeeks is here to make your presentations a breeze with CASB 2 0 IT Pros And Cons Of API Scanning CASB Deployment With our easy-to-use and customizable templates, you can focus on delivering your ideas rather than worrying about formatting. With a variety of designs to choose from, you are sure to find one that suits your needs. And with animations and unique photos, illustrations, and fonts, you can make your presentation pop. So whether you are giving a sales pitch or presenting to the board, make sure to check out Slidegeeks first

CASB 2 0 IT Reverse Proxy Vs Forward Proxy
This slide outlines the comparison between reverse proxy and forward proxy based on features. The purpose of this slide is to highlight the key differences between reverse proxy and forward proxy based on the features such as function, position, IP address, purpose, caching, SSL or TLS termination, performance, and implementation. If you are looking for a format to display your unique thoughts, then the professionally designed CASB 2 0 IT Reverse Proxy Vs Forward Proxy is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download CASB 2 0 IT Reverse Proxy Vs Forward Proxy and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.

CASB 2 0 IT Steps To Deploy Cloud Access Security Broker
This slide outlines the steps to implement a cloud access security broker in an organization. The purpose of this slide is to showcase the various steps to keep in mind while deploying a CASB model into a business and the steps include the deployment path, deployment model and releasing model. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward CASB 2 0 IT Steps To Deploy Cloud Access Security Broker template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal CASB 2 0 IT Steps To Deploy Cloud Access Security Broker that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers
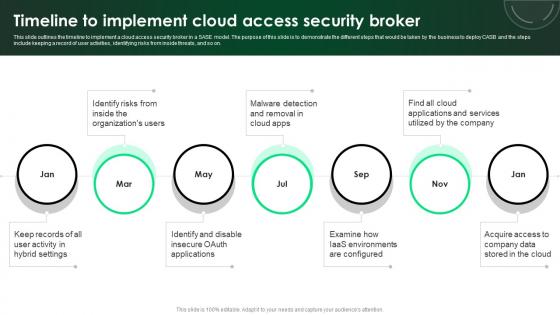
CASB 2 0 IT Timeline To Implement Cloud Access Security Broker
This slide outlines the timeline to implement a cloud access security broker in a SASE model. The purpose of this slide is to demonstrate the different steps that would be taken by the business to deploy CASB and the steps include keeping a record of user activities, identifying risks from inside threats, and so on. Make sure to capture your audiences attention in your business displays with our gratis customizable CASB 2 0 IT Timeline To Implement Cloud Access Security Broker. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.
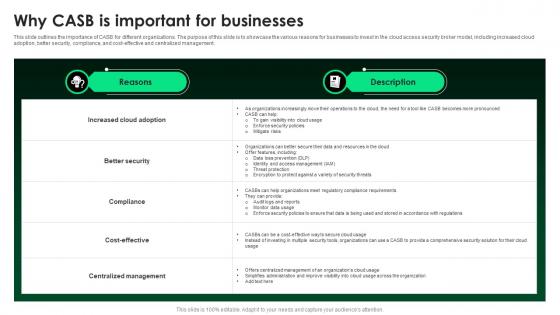
CASB 2 0 IT Why CASB Is Important For Businesses
This slide outlines the importance of CASB for different organizations. The purpose of this slide is to showcase the various reasons for businesses to invest in the cloud access security broker model, including increased cloud adoption, better security, compliance, and cost-effective and centralized management. This CASB 2 0 IT Why CASB Is Important For Businesses is perfect for any presentation, be it in front of clients or colleagues. It is a versatile and stylish solution for organizing your meetings. The CASB 2 0 IT Why CASB Is Important For Businesses features a modern design for your presentation meetings. The adjustable and customizable slides provide unlimited possibilities for acing up your presentation. Slidegeeks has done all the homework before launching the product for you. So, do not wait, grab the presentation templates today

Automated Workflow Software Funding Pitch Deck For Company Ppt Template
This Automated Workflow Software Funding Pitch Deck For Company Ppt Template is a primer on how to capitalize on business opportunities through planning, innovation, and market intelligence. The content-ready format of the complete deck will make your job as a decision-maker a lot easier. Use this ready-made PowerPoint Template to help you outline an extensive and legible plan to capture markets and grow your company on the right path, at an exponential pace. What is even more amazing is that this presentation is completely editable and 100 percent customizable. This Thirty Three slide complete deck helps you impress a roomful of people with your expertise in business and even presentation. Craft such a professional and appealing presentation for that amazing recall value. Download now.

Car Manufacturing Company Business Model Powerpoint Ppt Template Bundles BMC V

Global Innovation And Business Solutions Company Profile CP CD V

Micosoft Intensive Growth And Business Strategies Strategy CD V

Candle Business Venture Blueprint Powerpoint Presentation Slides BP V

Data Integration Strategies For Business Success Ppt Powerpoint Presentation Complete Deck With Slides

Pet Care Solution Provider Investor Funding Elevator Pitch Deck Ppt Template

Market Potential UI UX Enhancement Solution Investor Funding Elevator Pitch Deck
The following slide showcases growth opportunity lying in market for an ecommerce company. It outlines market size by year and growth rate of global market. Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Market Potential UI UX Enhancement Solution Investor Funding Elevator Pitch Deck and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.

Complete Us Crypto Tax Guide Cryptocurrency Management With Blockchain
This slide discusses the taxes in the crypto market. The purpose of this slide is to outline the crypto tax criteria used in the United States of America on Bitcoin and Crypto. It also includes the tax range for long-term and short-term capital gains.If you are looking for a format to display your unique thoughts, then the professionally designed Complete Us Crypto Tax Guide Cryptocurrency Management With Blockchain is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Complete Us Crypto Tax Guide Cryptocurrency Management With Blockchain and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.

Contractual And Jurisdictional Issues In Crypto Wallets Cryptocurrency Management With Blockchain
This slide highlights the contractual and jurisdictional issues faced by crypto wallets. The purpose of this slide is to outline the issues such as contractual and jurisdictional issues in crypto wallets.Are you in need of a template that can accommodate all of your creative concepts This one is crafted professionally and can be altered to fit any style. Use it with Google Slides or PowerPoint. Include striking photographs, symbols, depictions, and other visuals. Fill, move around, or remove text boxes as desired. Test out color palettes and font mixtures. Edit and save your work, or work with colleagues. Download Contractual And Jurisdictional Issues In Crypto Wallets Cryptocurrency Management With Blockchain and observe how to make your presentation outstanding. Give an impeccable presentation to your group and make your presentation unforgettable.

Benefits And Drawbacks Of Gray Box Testing Gray Box Testing Best Practices
This slide outlines the benefits and drawbacks of gray box testing. The purpose of this slide is to showcase the advantages and disadvantages such as limited access, lack of resources, and so on. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Benefits And Drawbacks Of Gray Box Testing Gray Box Testing Best Practices a try. Our experts have put a lot of knowledge and effort into creating this impeccable Benefits And Drawbacks Of Gray Box Testing Gray Box Testing Best Practices. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today

Roadmap To Implement Manual Testing In Company Gray Box Testing Best Practices
This slide outlines the deployment for software testing. The purpose of this slide is to highlight the steps that an organization should take while implementing software testing including, analysing static code, unit testing and so on. This modern and well-arranged Roadmap To Implement Manual Testing In Company Gray Box Testing Best Practices provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint, no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.

Timeline For Conducting Manual Testing In Organization Gray Box Testing Best Practices
This slide outlines the timeline for executing manual testing. The purpose of this slide is to showcase the different steps performed while implementing software testing, including preparation, strategy, test case design, and so on. Are you searching for a Timeline For Conducting Manual Testing In Organization Gray Box Testing Best Practices that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Timeline For Conducting Manual Testing In Organization Gray Box Testing Best Practices from Slidegeeks today.
Decoding Nestles Marketing Game Plan Strategy CD V
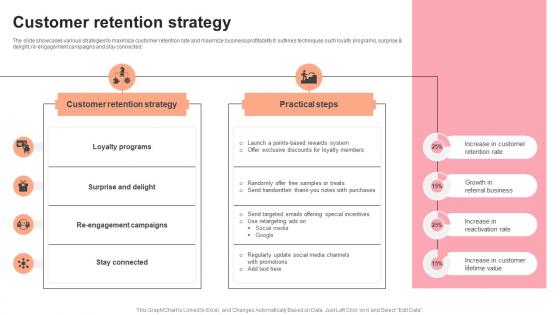
Customer Retention Strategy Pastry Shop Market Entry Plan GTM SS V
The slide showcases various strategies to maximize customer retention rate and maximize business profitability It outlines techniques such loyalty programs, surprise and delight, re-engagement campaigns and stay connected. Get a simple yet stunning designed Customer Retention Strategy Pastry Shop Market Entry Plan GTM SS V. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Customer Retention Strategy Pastry Shop Market Entry Plan GTM SS V can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.

 Home
Home