Risk

Opportunities And Threats For Penetrating In New Market Segments Target Market Profile Designs PDF
This is a opportunities and threats for penetrating in new market segments target market profile designs pdf template with various stages. Focus and dispense information on two stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like target market profile. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Opportunities And Threats For Penetrating In New Market Segments Target Market Size Professional PDF
This is a opportunities and threats for penetrating in new market segments target market size professional pdf template with various stages. Focus and dispense information on two stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like prospects, target market. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
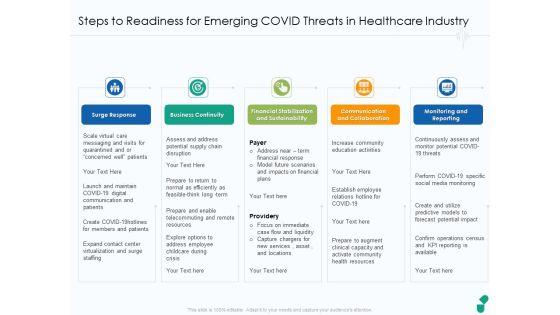
Steps To Readiness For Emerging COVID Threats In Healthcare Industry Ppt Model Slides PDF
This is a steps to readiness for emerging covid threats in healthcare industry ppt model slides pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like surge response, business continuity, financial stabilization and sustainability, communication and collaboration, monitoring and reporting. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Introduce Yourself Swot Analysis Option 2 Of 2 Threats Ppt Summary Layout Ideas PDF
This is a introduce yourself swot analysis option 2 of 2 threats ppt summary layout ideas pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like swot analysis option 2 of 2. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
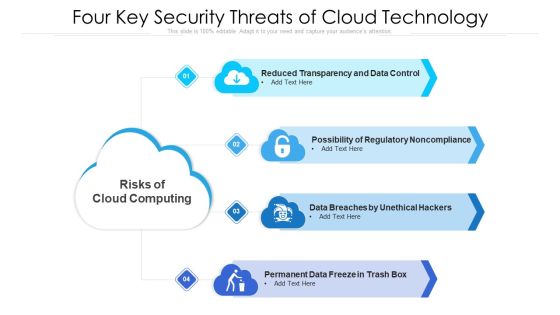
Four Key Security Threats Of Cloud Technology Ppt PowerPoint Presentation Gallery Introduction PDF
Presenting four key security threats of cloud technology ppt powerpoint presentation gallery introduction pdf to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including data breaches by unethical hackers, permanent data freeze in trash box, possibility of regulatory noncompliance. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Key Cloud Computing Threats In It Industry Ppt PowerPoint Presentation Gallery Slides PDF
Persuade your audience using this key cloud computing threats in it industry ppt powerpoint presentation gallery slides pdf. This PPT design covers eight stages, thus making it a great tool to use. It also caters to a variety of topics including complex architecture, legal issues, compliance issues. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
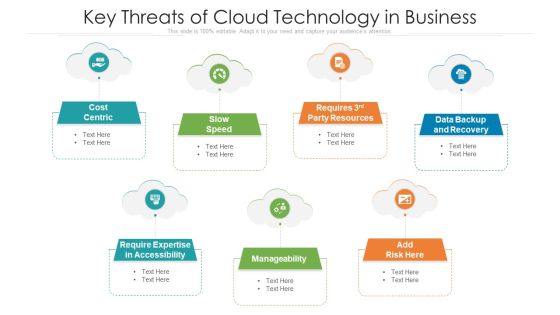
Key Threats Of Cloud Technology In Business Ppt PowerPoint Presentation Gallery Microsoft PDF
Persuade your audience using this key threats of cloud technology in business ppt powerpoint presentation gallery microsoft pdf. This PPT design covers seven stages, thus making it a great tool to use. It also caters to a variety of topics including cost centric, data backup and recovery, manageability. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Major Types Of Cloud Technology System Threats Ppt PowerPoint Presentation File Graphic Images PDF
Persuade your audience using this major types of cloud technology system threats ppt powerpoint presentation file graphic images pdf. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including interception, fabrication, interruption. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Environmental Assessment STEP Analysis For Opportunity And Threat Evaluation Ppt Gallery Templates PDF
This slide shows STEP analysis to analyze likelihood, importance and influence of political, economic, social and technological factors on organizational activities Deliver an awe inspiring pitch with this creative environmental assessment step analysis for opportunity and threat evaluation ppt gallery templates pdf bundle. Topics like economic, technological, social can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
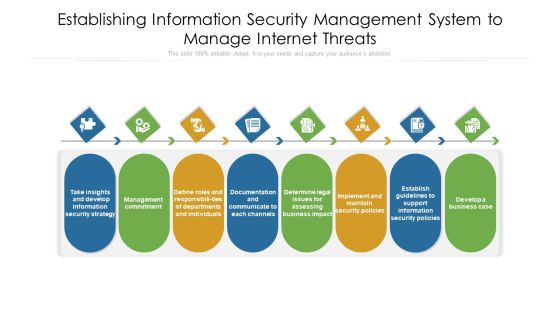
Establishing Information Security Management System To Manage Internet Threats Ppt PowerPoint Presentation File Visuals PDF
Persuade your audience using this establishing information security management system to manage internet threats ppt powerpoint presentation file visuals pdf. This PPT design covers eight stages, thus making it a great tool to use. It also caters to a variety of topics including documentation, departments, management. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Agenda For Executing Security Management Program To Mitigate Threats And Safeguard Confidential Organizational Data Clipart PDF
Presenting Agenda for executing security management program to mitigate threats and safeguard confidential organizational data clipart pdf to provide visual cues and insights. Share and navigate important information on six stages that need your due attention. This template can be used to pitch topics like effective response procedures, intentional or otherwise, enable organizational. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
Executing Security Management Program To Mitigate Threats And Safeguard Confidential Organizational Data Roadmap Professional PDF
Presenting Executing security management program to mitigate threats and safeguard confidential organizational data roadmap professional pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like roadmap. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
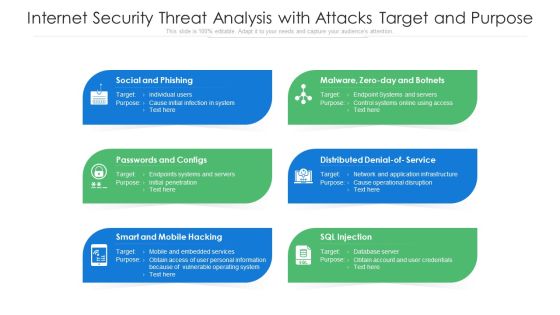
Internet Security Threat Analysis With Attacks Target And Purpose Ppt PowerPoint Presentation Pictures Structure PDF
Presenting internet security threat analysis with attacks target and purpose ppt powerpoint presentation pictures structure pdf to dispense important information. This template comprises six stages. It also presents valuable insights into the topics including social and phishing, passwords and configs, smart and mobile hacking. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Internet Security Threat Analysis With Tactics And Victims Ppt PowerPoint Presentation Infographic Template Format Ideas PDF
Showcasing this set of slides titled internet security threat analysis with tactics and victims ppt powerpoint presentation infographic template format ideas pdf. The topics addressed in these templates are fake installation, hack the bidding models, hack the identity. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
Determine Phases Of Threat Attack Disrupting IT Project Safety Ppt File Icons PDF
Presenting determine phases of threat attack disrupting it project safety ppt file icons pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like social media, systems, network, target, email. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
Mitigation Strategies For Operational Threat Post It Notes Ppt Visual Aids Inspiration PDF
This is a mitigation strategies for operational threat post it notes ppt visual aids inspiration pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like post it notes. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
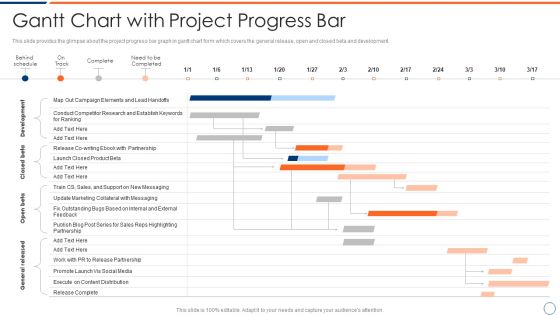
How To Intensify Project Threats Gantt Chart With Project Progress Bar Elements PDF
This slide provides the glimpse about the project progress bar graph in gantt chart form which covers the general release, open and closed beta and development. Deliver an awe inspiring pitch with this creative how to intensify project threats gantt chart with project progress bar elements pdf bundle. Topics like development, closed beta, open beta, general released. can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
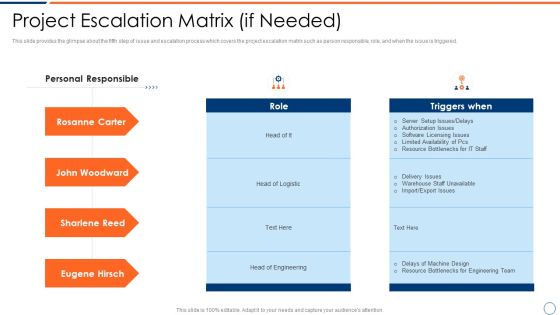
How To Intensify Project Threats Project Escalation Matrix If Needed Introduction PDF
This slide provides the glimpse about the fifth step of issue and escalation process which covers the project escalation matrix such as person responsible, role, and when the issue is triggered. Deliver an awe inspiring pitch with this creative how to intensify project threats project escalation matrix if needed introduction pdf bundle. Topics like project escalation matrix if needed can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
How To Intensify Project Threats Project Performance Tracking And Reporting Structure PDF
This slide provides the glimpse about the fourth step of issue and escalation process which covers the project name, start and finish, work duration, costs, etc. Deliver an awe inspiring pitch with this creative how to intensify project threats project performance tracking and reporting structure pdf bundle. Topics like project name, start and finish, work duration, costs can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

How To Intensify Project Threats Project Validation And Prioritization Brochure PDF
This slide provides the glimpse about the second step of issue and escalation process which covers the project validation and prioritization along with the features and different projects initiatives. Deliver and pitch your topic in the best possible manner with this how to intensify project threats project validation and prioritization brochure pdf. Use them to share invaluable insights on strategic fit, economic impact, feasibility and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

How To Intensify Project Threats Escalation Procedure Work Instruction Elements PDF
This is a how to intensify project threats escalation procedure work instruction elements pdf template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like level of notification, level of on site support, coverage hours that machine is down. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
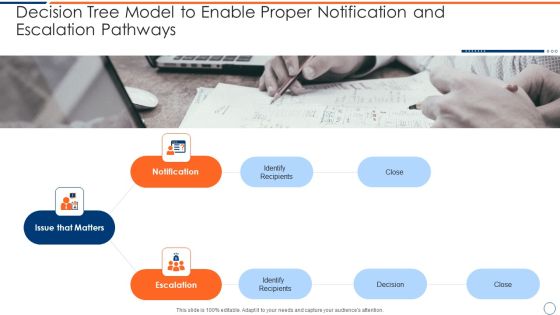
How To Intensify Project Threats Decision Tree Model To Enable Proper Notification Topics PDF
Presenting how to intensify project threats decision tree model to enable proper notification topics pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like issue that matters, notification, escalation. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
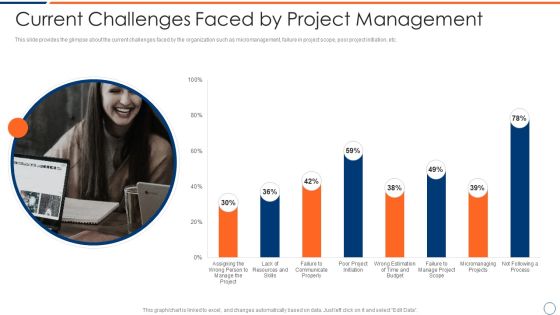
How To Intensify Project Threats Current Challenges Faced By Project Management Elements PDF
This slide provides the glimpse about the current challenges faced by the organization such as micromanagement, failure in project scope, poor project initiation, etc. Deliver an awe inspiring pitch with this creative how to intensify project threats current challenges faced by project management elements pdf bundle. Topics like resources, budget, process, communicate can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

How To Intensify Project Threats Dashboard For Managing Project Issues Inspiration PDF
This slide provides the glimpse about the KPI for managing project issues in the organization wherein focus is on project health, tasks, progress, time, cost and workload. Deliver and pitch your topic in the best possible manner with this how to intensify project threats dashboard for managing project issues inspiration pdf. Use them to share invaluable insights on time, cost, workload, progress, tasks and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

How To Intensify Project Threats Delay And Over Run Cost In The Projects Topics PDF
This slide provides the glimpse about the delay and over run project costs graph wherein the number of projects has been monitored, along with delayed projects and cost overrun. Deliver an awe inspiring pitch with this creative how to intensify project threats delay and over run cost in the projects topics pdf bundle. Topics like monitored, delayed projects, cost overrun can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
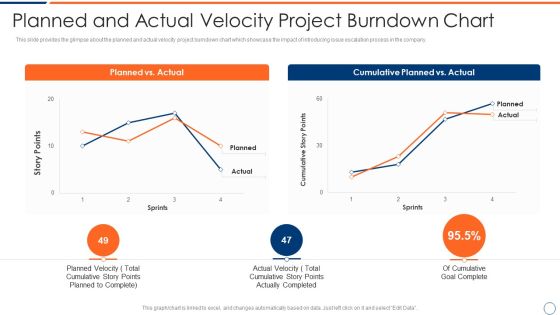
How To Intensify Project Threats Planned And Actual Velocity Project Burndown Chart Summary PDF
This slide provides the glimpse about the planned and actual velocity project burndown chart which showcase the impact of introducing issue escalation process in the company. Deliver an awe inspiring pitch with this creative how to intensify project threats planned and actual velocity project burndown chart summary pdf bundle. Topics like planned vs actual, cumulative planned vs actual can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

How To Intensify Project Threats Project Issues Management Dashboard Clipart PDF
This slide provides the glimpse about the project issues wherein focus is on number of reported issues, unresolved issues and issues allocated per resources. Deliver and pitch your topic in the best possible manner with this how to intensify project threats project issues management dashboard clipart pdf. Use them to share invaluable insights on project issues management dashboard and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Cyber Security Administration In Organization Budget For Effective Threat Management At Workplace Structure PDF
Firm has prepared a budget for managing cybersecurity by optimizing various functional areas. It also provides information about the software used and the duration required for implementation. Deliver an awe inspiring pitch with this creative cyber security administration in organization budget for effective threat management at workplace structure pdf bundle. Topics like incident management, onboarding, process, release can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Solution Evaluation Criteria Assessment And Threat Impact Matrix Table Of Contents Sample PDF
Presenting solution evaluation criteria assessment and threat impact matrix table of contents sample pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like analysis, management, requirements, organizational. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
Agenda For Solution Evaluation Criteria Assessment And Threat Impact Matrix Summary PDF
This is a agenda for solution evaluation criteria assessment and threat impact matrix summary pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like analyze, determine, organization, value, severity matrix. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Solution Evaluation Criteria Assessment And Threat Impact Matrix Solution Assessment And Validation Model Graphics PDF
This slide shows the details on tasks involved in allocate requirements stage of solution assessment and validation along with the categories of requirements. Deliver an awe inspiring pitch with this creative solution evaluation criteria assessment and threat impact matrix solution assessment and validation model graphics pdf bundle. Topics like allocate requirements categories, allocate requirements description can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Competitive Advantage Real Time Assessment Of Security Threats SIEM Pictures PDF
This slide covers the competitive advantage scoring for security information and event management based on different factors such as value, deployment, ease of use, support, etc. Deliver an awe inspiring pitch with this creative competitive advantage real time assessment of security threats siem pictures pdf bundle. Topics like siem competitive advantage can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
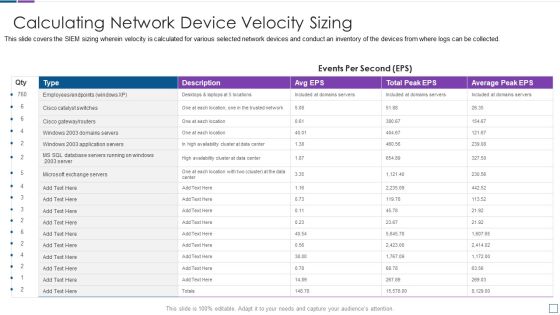
Real Time Assessment Of Security Threats Calculating Network Device Velocity Sizing Portrait PDF
This slide covers the SIEM sizing wherein velocity is calculated for various selected network devices and conduct an inventory of the devices from where logs can be collected. Deliver an awe inspiring pitch with this creative real time assessment of security threats calculating network device velocity sizing portrait pdf bundle. Topics like calculating network device velocity sizing can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
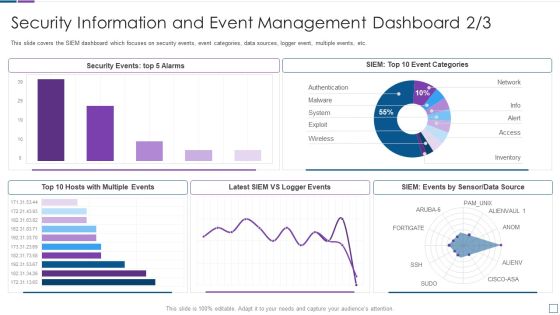
Real Time Assessment Of Security Threats Security Information And Event Management Dashboard Infographics PDF
This slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Deliver an awe inspiring pitch with this creative real time assessment of security threats security information and event management dashboard infographics pdf bundle. Topics like security information and event management dashboard can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
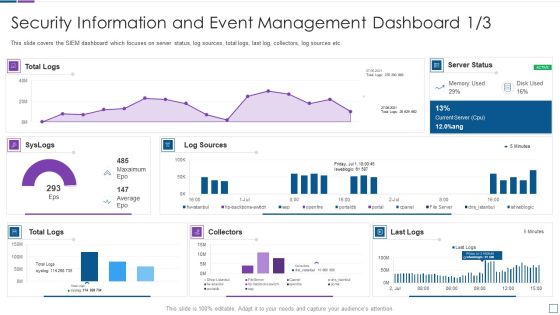
Real Time Assessment Of Security Threats Security Information And Event Management Microsoft PDF
This slide covers the SIEM dashboard which focuses on server status, log sources, total logs, last log, collectors, log sources etc. Deliver and pitch your topic in the best possible manner with this real time assessment of security threats security information and event management microsoft pdf. Use them to share invaluable insights on security information and event management dashboard and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Real Time Assessment Of Security Threats Various SIEM Cost Plans Offered By Our Company Topics PDF
This slide covers the different costs plan offered by our company such as basic, intermediate, advanced, learning model costs. Deliver an awe inspiring pitch with this creative real time assessment of security threats various siem cost plans offered by our company topics pdf bundle. Topics like annual costs of tools, annual cost of personnel, one time cost can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Real Time Assessment Of Security Threats Estimating Total Cost Of Ownership Of SIEM Icons PDF
This slide covers the total cost of ownership incurred by SIEM services which focuses on the costs of hardware, software, infrastructure, and support.Deliver an awe inspiring pitch with this creative real time assessment of security threats estimating total cost of ownership of siem icons pdf bundle. Topics like hardware, infrastructure, software, support can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Real Time Assessment Of Security Threats Log Management Services Metrics Slides PDF
This is a real time assessment of security threats log management services metrics slides pdf template with various stages. Focus and dispense information on eight stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like configurations, log management, metrics, virtualization, databases. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Real Time Assessment Of Security Threats How SIEM Works Inspiration PDF
Presenting real time assessment of security threats how siem works inspiration pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like correlation, behavior analytics, taxonomy, normalization. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Real Time Assessment Of Security Threats Our SIEM Companys Milestones Slides PDF
This slide provides the milestones of our company such as foundation year, revenue generation, profitability, etc. Presenting real time assessment of security threats our siem companys milestones slides pdf to provide visual cues and insights. Share and navigate important information on six stages that need your due attention. This template can be used to pitch topics like our siem companys milestones. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
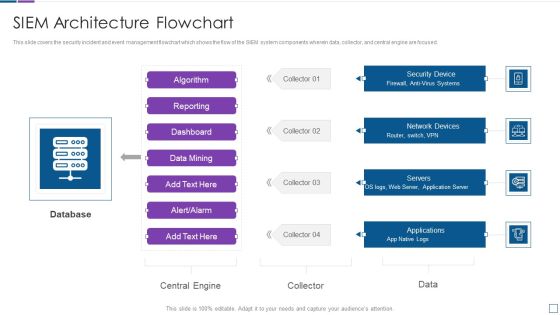
Real Time Assessment Of Security Threats SIEM Architecture Flowchart Sample PDF
This slide covers the security incident and event management flowchart which shows the flow of the SIEM system components wherein data, collector, and central engine are focused. Deliver an awe inspiring pitch with this creative real time assessment of security threats siem architecture flowchart sample pdf bundle. Topics like database, network devices, security device, servers, applications can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
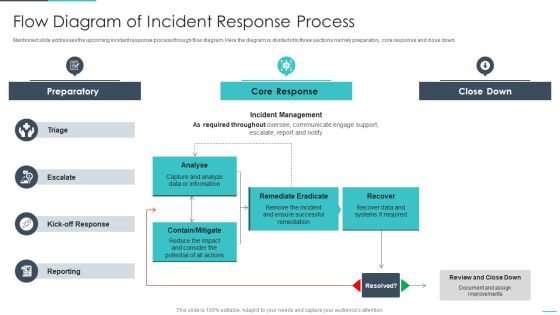
Handling Cyber Threats Digital Era Flow Diagram Of Incident Response Process Ppt Infographics Inspiration PDF
Mentioned slide addresses the upcoming incident response process through flow diagram. Here the diagram is divided into three sections namely preparatory, core response and close down. Deliver an awe inspiring pitch with this creative handling cyber threats digital era flow diagram of incident response process ppt infographics inspiration pdf bundle. Topics like preparatory, remediate eradicate, analyse can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Handling Cyber Threats Digital Era Security Lifecycle Ppt Summary Brochure PDF
This is a handling cyber threats digital era security lifecycle ppt summary brochure pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like security lifecycle. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
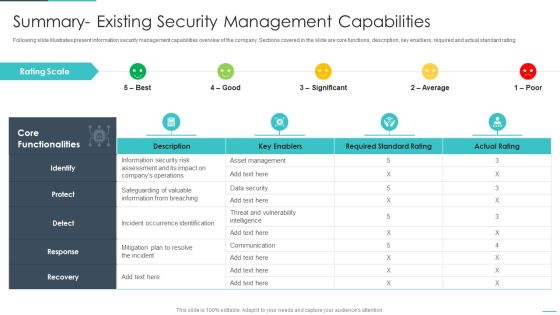
Handling Cyber Threats Digital Era Summary Existing Security Management Capabilities Ppt File Demonstration PDF
Following slide illustrates present information security management capabilities overview of the company. Sections covered in the slide are core functions, description, key enablers, required and actual standard rating. Deliver an awe inspiring pitch with this creative handling cyber threats digital era summary existing security management capabilities ppt file demonstration pdf bundle. Topics like summary existing security management capabilities can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
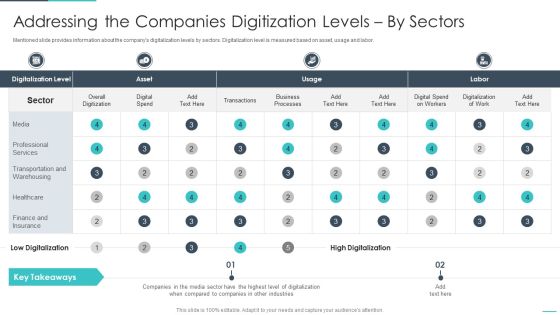
Handling Cyber Threats Digital Era Addressing The Companies Digitization Ppt Portfolio Smartart PDF
Mentioned slide provides information about the companys digitalization levels by sectors. Digitalization level is measured based on asset, usage and labor. Deliver and pitch your topic in the best possible manner with this andling cyber threats digital era addressing the companies digitization ppt portfolio smartart pdf. Use them to share invaluable insights on addressing the companies digitization levels by sectors and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
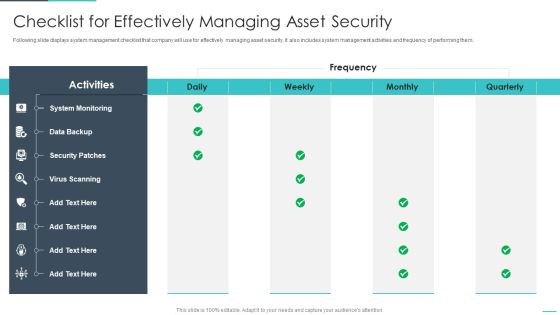
Handling Cyber Threats Digital Era Checklist For Effectively Managing Asset Security Ppt Slides Example File PDF
Following slide displays system management checklist that company will use for effectively managing asset security. It also includes system management activities and frequency of performing them. Deliver an awe inspiring pitch with this creative handling cyber threats digital era checklist for effectively managing asset security ppt slides example file pdf bundle. Topics like checklist for effectively managing asset security can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
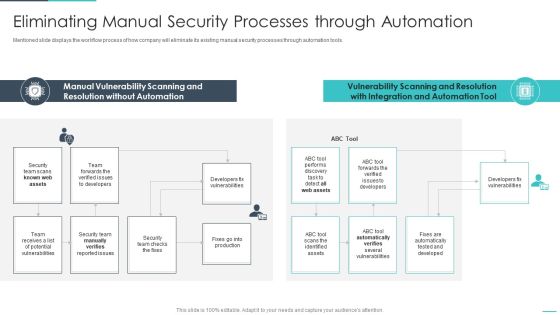
Handling Cyber Threats Digital Era Eliminating Manual Security Processes Ppt Show Influencers PDF
Mentioned slide displays the workflow process of how company will eliminate its existing manual security processes through automation tools. Deliver and pitch your topic in the best possible manner with this handling cyber threats digital era eliminating manual security processes ppt show influencers pdf. Use them to share invaluable insights on eliminating manual security processes through automation and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Handling Cyber Threats Digital Era Information Security Program Framework Ppt Model Summary PDF
Mentioned slide portrays the key components of companys information security framework. Components covered are context and leadership, evaluation and direction, prevention, detection etc. Deliver and pitch your topic in the best possible manner with this handling cyber threats digital era information security program framework ppt model summary pdf. Use them to share invaluable insights on information security program framework key components and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
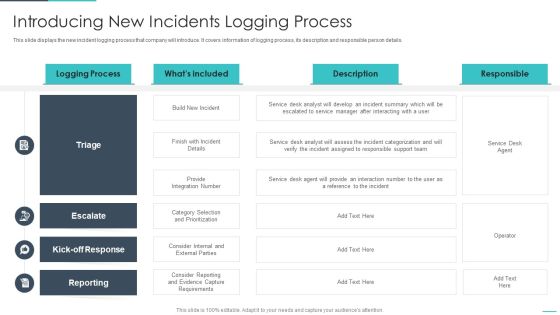
Handling Cyber Threats Digital Era Introducing New Incidents Logging Process Ppt Slides Graphic Images PDF
This slide displays the new incident logging process that company will introduce. It covers information of logging process, its description and responsible person details. Deliver an awe inspiring pitch with this creative handling cyber threats digital era introducing new incidents logging process ppt slides graphic images pdf bundle. Topics like introducing new incidents logging process can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Handling Cyber Threats Digital Era Overview Of New IT Policy Framework Ppt Summary Guidelines PDF
This slide demonstrate the new information technology policy framework of the company focusing on security and data usage policies. Deliver and pitch your topic in the best possible manner with this handling cyber threats digital era overview of new it policy framework ppt summary guidelines pdf. Use them to share invaluable insights on overview of new it policy framework and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Handling Cyber Threats Digital Era Determining The Priority Requirements Ppt Outline Visual Aids PDF
This slide demonstrates the priority requirements of companies while buying IoT products. Strong cybersecurity is the topmost priority of companies followed by reliability and compatibility. Deliver an awe inspiring pitch with this creative handling cyber threats digital era determining the priority requirements ppt outline visual aids pdf bundle. Topics like determining the priority requirements for buying iot products can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
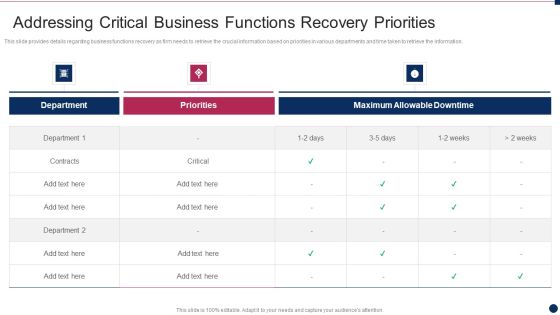
Threat Management At Workplace Addressing Critical Business Functions Recovery Priorities Formats Pdf
This slide provides details regarding business functions recovery as firm needs to retrieve the crucial information based on priorities in various departments and time taken to retrieve the information. Deliver an awe inspiring pitch with this creative threat management at workplace addressing critical business functions recovery priorities formats pdf bundle. Topics like priorities, department, maximum allowable downtime can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Threat Management At Workplace Evaluating Financial Practices In Firm Ideas Pdf
The firm can track the financial performance by looking the financial practices it follows in order to avoid any early signs of financial distress. Deliver an awe inspiring pitch with this creative threat management at workplace evaluating financial practices in firm ideas pdf bundle. Topics like organization prepare cash flow projections, financial statements on a budget, comprehensive operating budget can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Data Safety Initiatives For Effective IT Security Threats Administration Security Lifecycle Template PDF
This is a data safety initiatives for effective it security threats administration security lifecycle template pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like information system, security controls, monitor, assess, implement, authorize. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Data Safety Initiatives For Effective IT Security Threats Administration Table Of Contents Themes PDF
Presenting data safety initiatives for effective it security threats administration table of contents themes pdf to provide visual cues and insights. Share and navigate important information on eight stages that need your due attention. This template can be used to pitch topics like global market insights, gap identification, defining business priorities, about security program, companies digitization levels. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Agenda For Developing Cyber Security Threat Awareness Staff Training Program Inspiration PDF
This is a Agenda For Developing Cyber Security Threat Awareness Staff Training Program Inspiration PDF template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Agenda. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

IT Threats Response Playbook Addressing The Cyber Incident Logging Process Introduction PDF
This slide displays logging process for a cyber incident logging. It covers information about process ID, procedure, its description and owner details.Deliver and pitch your topic in the best possible manner with this IT Threats Response Playbook Addressing The Cyber Incident Logging Process Introduction PDF. Use them to share invaluable insights on Provide Integration, Responsible Support, Assess The Incident and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

IT Threats Response Playbook Asset Criticality Of Identified System Components Themes PDF
Mentioned slide demonstrates the asset criticality of identified system components. It includes information of system name, component used, impact rating, criticality rating and failure cost.Deliver and pitch your topic in the best possible manner with this IT Threats Response Playbook Asset Criticality Of Identified System Components Themes PDF. Use them to share invaluable insights on Master Terminal, Extremely Critical, Reasonably Critical and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

IT Threats Response Playbook Checklist For Work From Home Data Security Inspiration PDF
This is a IT Threats Response Playbook Checklist For Work From Home Data Security Inspiration PDF template with various stages. Focus and dispense information on one stage using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Security Policies, Incident Reporting, Remote Workstations. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

IT Threats Response Playbook Classifying Various Security Issues And Attacks Professional PDF
Purpose of this slide is to show the classification of different security issues and attacks. Categories covered are majorly internal as well as external issues and attacks.Deliver and pitch your topic in the best possible manner with this IT Threats Response Playbook Classifying Various Security Issues And Attacks Professional PDF. Use them to share invaluable insights on External Issues, Audio Steganography, Malware Injection and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
 Home
Home