Hacking

Series Of Cyber Security Attacks Against Ukraine 2022 Us Is Unmasking Russian Hackers Faster Than Ever Guidelines PDF
This slide represents the rapid announcements made by the united states about russian cyberattacks against ukraine within the 48 hours of the cyberwar. Explore a selection of the finest Series Of Cyber Security Attacks Against Ukraine 2022 Us Is Unmasking Russian Hackers Faster Than Ever Guidelines PDF here. With a plethora of professionally designed and pre made slide templates, you can quickly and easily find the right one for your upcoming presentation. You can use our Series Of Cyber Security Atta to effectively convey your message to a wider audience. Slidegeeks has done a lot of research before preparing these presentation templates. The content can be personalized and the slides are highly editable. Grab templates today from Slidegeeks.
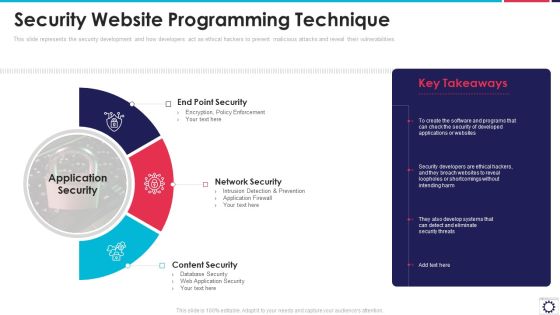
Website Programming IT Security Website Programming Technique Ppt PowerPoint Presentation File Infographics PDF
This slide represents the security development and how developers act as ethical hackers to prevent malicious attacks and reveal their vulnerabilities. Presenting website programming it security website programming technique ppt powerpoint presentation file infographics pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like end point security, network security, content security, application security. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
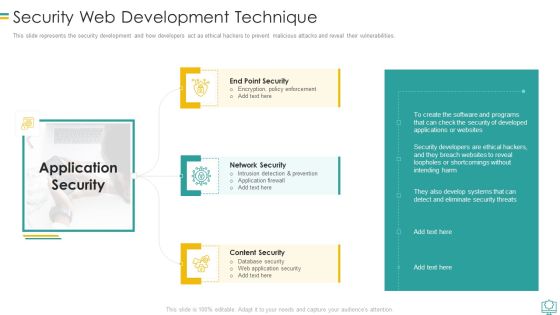
Security Web Development Technique Mockup PDF
This slide represents the security development and how developers act as ethical hackers to prevent malicious attacks and reveal their vulnerabilities.This is a Security Web Development Technique Mockup PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Intrusion Detection And Prevention, Encryption Policy Enforcement, Database Security You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cyber Exploitation IT Budget For New Recruited Professionals Demonstration PDF
This slide represents the budget for newly recruited professionals, including new professionals, number of total posts, annual salaries, and total funding for salaries. Deliver and pitch your topic in the best possible manner with this cyber exploitation it budget for new recruited professionals demonstration pdf. Use them to share invaluable insights on it security analyst, certified ethical hacker, security consultant and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
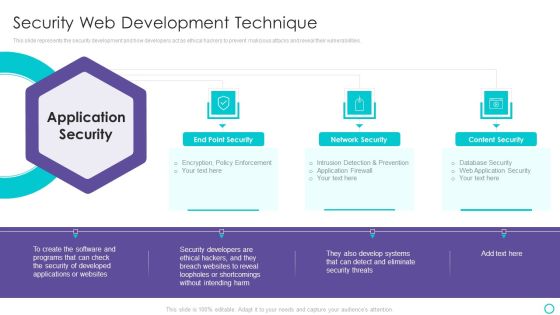
Website Designing And Development Service Security Web Development Technique Themes PDF
This slide represents the security development and how developers act as ethical hackers to prevent malicious attacks and reveal their vulnerabilities.This is a Website Designing And Development Service Security Web Development Technique Themes PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Network Security, Content Security, Loopholes Or Shortcomings You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cyber Exploitation IT Dashboard For Threat Tracking Topics PDF
This slide depicts the dashboard for threat tracking through cyber security measures and ethical hackers by covering monthly threat status, current risk status, threat-based on the role, threats by owners, risk by threats, and threat report. Deliver an awe inspiring pitch with this creative cyber exploitation it dashboard for threat tracking topics pdf bundle. Topics like dashboard for threat tracking can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

IT Career Certifications What Are Certification Ppt PowerPoint Presentation File Files PDF
This template covers IT certification such as Certified ScrumMaster CSM, AWS Certified Solutions Architect Certification, Certified Ethical Hacker CEH etc, qualification and job description. Deliver and pitch your topic in the best possible manner with this IT Career Certifications What Are Certification Ppt PowerPoint Presentation File Files PDF. Use them to share invaluable insights on Certified ScrumMaster, Certified ethical hacker, ITIL Foundation and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Introduction To Black Hat Hackers Crackers Ppt Show Images PDF
Deliver an awe inspiring pitch with this creative introduction to black hat hackers crackers ppt show images pdf bundle. Topics like system, data can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Cyber Exploitation IT Purpose Of Hackers Infographics PDF
This slide describes the common types of cybercrime such as identity theft, computer fraud, privacy breach, electronic money laundering, electronic funds transfer, and so on. This is a cyber exploitation it purpose of hackers infographics pdf template with various stages. Focus and dispense information on ten stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like computer fraud, privacy breach, electronic money laundering, electronic funds transfer, denial of service attacks. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
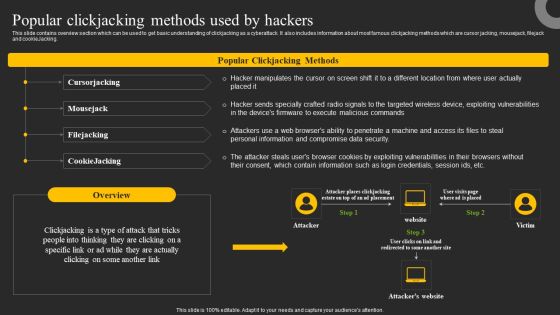
Popular Clickjacking Methods Used By Hackers Ppt Portfolio Microsoft PDF
This slide contains overview section which can be used to get basic understanding of clickjacking as a cyberattack. It also includes information about most famous clickjacking methods which are cursor jacking, mousejack, filejack and cookieJacking. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Popular Clickjacking Methods Used By Hackers Ppt Portfolio Microsoft PDF for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.

Cybersecurity Risk Scorecard Information Security Companies Risk Coverage Scorecard Icons PDF
Deliver an awe inspiring pitch with this creative cybersecurity risk scorecard information security companies risk coverage scorecard icons pdf bundle. Topics like hacker protection, network security, cubit score can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
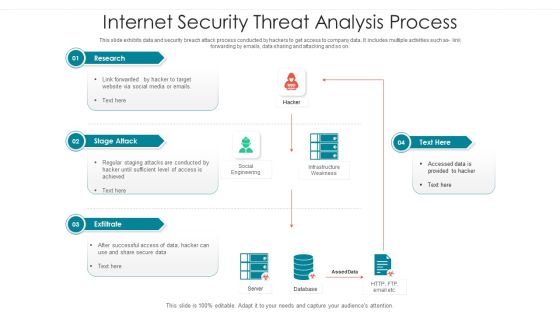
Internet Security Threat Analysis Process Brochure PDF
Following slide showcase how a data breach process is performed by hacker to collect and utilize company data. It includes following activities such as code integration with company software, so on. Showcasing this set of slides titled internet security threat analysis process brochure pdf. The topics addressed in these templates are supply chain attack, execution persistence, defense evasion, exfiltration, keyboard attack. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.

Blockchain Security Solutions Deployment How Fraudsters Attack Blockchain Network Sample PDF
This slide describes the primary attacks that hackers can use to exploit blockchain technology networks. The purpose of this slide is to showcase some basic threats that hackers can use to manipulate a blockchain network, such as phishing attacks, routing attacks, sybil, and 51 percent. Present like a pro with Blockchain Security Solutions Deployment How Fraudsters Attack Blockchain Network Sample PDF Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
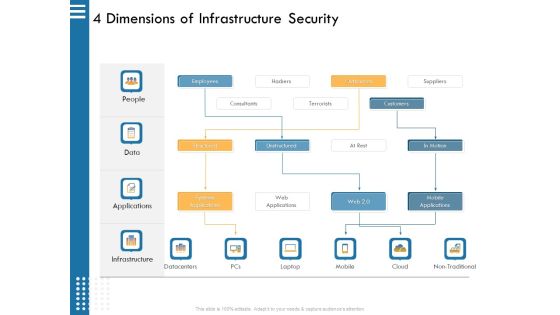
IT Infrastructure Governance 4 Dimensions Of Infrastructure Security Ppt File Example PDF
This is a it infrastructure governance 4 dimensions of infrastructure security ppt file example pdf. template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like employees, outsources, hackers, terrorists, consultants. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
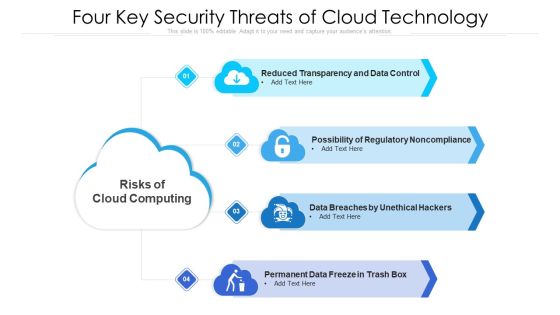
Four Key Security Threats Of Cloud Technology Ppt PowerPoint Presentation Gallery Introduction PDF
Presenting four key security threats of cloud technology ppt powerpoint presentation gallery introduction pdf to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including data breaches by unethical hackers, permanent data freeze in trash box, possibility of regulatory noncompliance. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Russian Cyber Attacks On Ukraine IT Hacker Group Anonymous Has Waged Icons PDF
This slide depicts the anonymous organization and how they have started a cyberwar against Russia by gathering worldwide hackers through Twitter. Deliver and pitch your topic in the best possible manner with this russian cyber attacks on ukraine it hacker group anonymous has waged icons pdf. Use them to share invaluable insights on hacker group anonymous has waged a cyberwar against russia and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Data Wiper Spyware Attack Ukraine And Russia Cyber Warfare Russian Vigilante Hacker Sample PDF
This slide depicts the Russian vigilante hacker who was able to bring down some official Ukrainian websites and one military website along with his group of 6 hackers.Deliver and pitch your topic in the best possible manner with this data wiper spyware attack ukraine and russia cyber warfare russian vigilante hacker sample pdf Use them to share invaluable insights on ukraine and russia cyber warfare russian vigilante hacker and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Hacker With Dark Face In Hoodie Ppt PowerPoint Presentation File Shapes
Presenting this set of slides with name hacker with dark face in hoodie ppt powerpoint presentation file shapes. This is a one stage process. The stage in this process is hacker with dark face in hoodie. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Picture Of Hacker In Mask Hood Ppt PowerPoint Presentation Layouts Inspiration
Presenting this set of slides with name picture of hacker in mask hood ppt powerpoint presentation layouts inspiration. This is a one stage process. The stage in this process is picture of hacker in mask hood. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
Online Crime With Hacker And Spider Vector Icon Ppt PowerPoint Presentation Gallery Examples PDF
Showcasing this set of slides titled online crime with hacker and spider vector icon ppt powerpoint presentation gallery examples pdf. The topics addressed in these templates are online crime with hacker and spider vector icon. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
Hacker Performing Cyber Attack Vector Icon Ppt PowerPoint Presentation Icon Professional PDF
Presenting hacker performing cyber attack vector icon ppt powerpoint presentation icon professional pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including hacker performing cyber attack vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Hackers Breaching Network Safety Through Internet Threats Ppt PowerPoint Presentation File Formats PDF
Presenting hackers breaching network safety through internet threats ppt powerpoint presentation file formats pdf to dispense important information. This template comprises two stages. It also presents valuable insights into the topics including hackers breaching network safety through internet threats. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Icon Of Hacker Launching Cyber Phishing Scams And Attacks Background PDF
Presenting icon of hacker launching cyber phishing scams and attacks background pdf to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including icon of hacker launching cyber phishing scams and attacks. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Hacker Stealing Business Confidential Data Base Through Internet Threats Ppt PowerPoint Presentation File Pictures PDF
Persuade your audience using this hacker stealing business confidential data base through internet threats ppt powerpoint presentation file pictures pdf. This PPT design covers five stages, thus making it a great tool to use. It also caters to a variety of topics including hacker stealing business confidential data base through internet threats. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Various Channels Used By Hackers To Launch Internet Threats Ppt PowerPoint Presentation File Show PDF
Presenting various channels used by hackers to launch internet threats ppt powerpoint presentation file show pdf to dispense important information. This template comprises two stages. It also presents valuable insights into the topics including various channels used by hackers to launch internet threats. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Vector Illustrating Hacker Launching Internet Threats Through Malware Ppt PowerPoint Presentation Icon Backgrounds PDF
Persuade your audience using this vector illustrating hacker launching internet threats through malware ppt powerpoint presentation icon backgrounds pdf. This PPT design covers three stages, thus making it a great tool to use. It also caters to a variety of topics including vector illustrating hacker launching internet threats through malware. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Data Wiper Spyware Attack Hacker Group Anonymous Has Waged A Cyberwar Against Russia Guidelines PDF
This slide depicts the anonymous organization and how they have started a cyberwar against Russia by gathering worldwide hackers through Twitter.Deliver and pitch your topic in the best possible manner with this data wiper spyware attack hacker group anonymous has waged a cyberwar against russia guidelines pdf Use them to share invaluable insights on russian government, according to subsequent, belarusian government and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Internet Security Threat Analysis Process By Backdoor Graphics PDF
This slide exhibits data and security breach attack process conducted by hackers to get access to company data. It includes multiple activities such as link forwarding by emails, data sharing and attacking and so on. Showcasing this set of slides titled internet security threat analysis process by backdoor graphics pdf. The topics addressed in these templates are exfiltrate, stage attack, research. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
Ukraine Cyberwarfare Hacker Group Anonymous Has Waged A Cyberwar Against Russia Icons Pdf
This slide depicts the anonymous organization and how they have started a cyberwar against Russia by gathering worldwide hackers through Twitter. This is a ukraine cyberwarfare hacker group anonymous has waged a cyberwar against russia icons pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like the organization was accused of taking down the websites of the Russian energy company Gazprom, the state controlled Russian news channel RT, and many Russian and Belarusian government entities. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Data Wiper Spyware Attack US Is Unmasking Russian Hackers Faster Than Ever Mockup PDF
This slide represents the rapid announcements made by the United States about Russian cyberattacks against Ukraine within the 48 hours of the cyberwar. This is a data wiper spyware attack us is unmasking russian hackers faster than ever mockup pdf template with various stages. Focus and dispense information on seven stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like blamed russian operatives, russian main intelligence, emerging technologies You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Ukraine Cyberwarfare Us Is Unmasking Russian Hackers Faster Than Ever Rules Pdf
This slide represents the rapid announcements made by the United States about Russian cyberattacks against Ukraine within the 48 hours of the cyberwar. This is a ukraine cyberwarfare us is unmasking russian hackers faster than ever rules pdf template with various stages. Focus and dispense information on seven stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like demonstrates how attribution has become a critical tactic of cyber warfare, quickness with which us and uk authorities, cyberattack has been staged to cause fear in ukraine. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
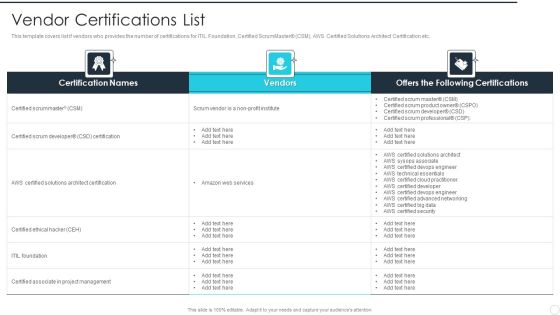
IT Career Certifications Vendor Certifications List Ppt PowerPoint Presentation File Background Designs PDF
This template covers list if vendors who provides the number of certifications for ITIL Foundation, Certified ScrumMaster CSM, AWS Certified Solutions Architect Certification etc. Deliver an awe inspiring pitch with this creative IT Career Certifications Vendor Certifications List Ppt PowerPoint Presentation File Background Designs PDF bundle. Topics like Certified Scrummaster, Certified Scrum Developer, Certified Ethical Hacker can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Information Technology Certifications Advantages Training Cost And Exam Cost Demonstration PDF
This template covers training cost and exam cost for certified scrum developer CSD certification certified scrummaster CSM, AWS certified solutions architect certification etc. Deliver an awe inspiring pitch with this creative Information Technology Certifications Advantages Training Cost And Exam Cost Demonstration PDF bundle. Topics like Certified ScrumMaster, Certified Scrum Developer, Certified Ethical Hacker can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Information Technology Certifications Advantages What Are Certification Themes PDF
This template covers IT certification such as certified scrum master CSM, AWS certified solutions architect certification, certified ethical hacker CEH etc, qualification and job description. Deliver and pitch your topic in the best possible manner with this Information Technology Certifications Advantages What Are Certification Themes PDF. Use them to share invaluable insights on Certified ScrumMaster, Architect Certification, ITIL Foundation and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Information Technology Certifications Advantages IT Certification Career Path Diagrams PDF
This template covers the career path to become a certified professional including available courses for certified scrum developer CSD certification certified scrum master CSM etc. Deliver an awe inspiring pitch with this creative Information Technology Certifications Advantages IT Certification Career Path Diagrams PDF bundle. Topics like Certified Scrum Developer, Certified ScrumMaster, Certified Ethical Hacker can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

What Are Certification Technology License For IT Professional Background PDF
This template covers IT certification such as Certified ScrumMaster CSM, AWS Certified Solutions Architect Certification, Certified Ethical Hacker CEH etc, qualification and job description.Deliver and pitch your topic in the best possible manner with this What Are Certification Technology License For IT Professional Background PDF. Use them to share invaluable insights on Architect Certification, Accredited Solutions, Project Management and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Software Checklist To Respond Cyber Security Cases Action Plan Ppt PowerPoint Presentation File Visuals PDF
This slide provides checklist of operating systems used in responding to cyber threat incidents. The purpose of this checklist is to use most appropriate software to respond and to reduce risk. It includes incidents such as information leakage, password change, data stealing etc. Pitch your topic with ease and precision using this Software Checklist To Respond Cyber Security Cases Action Plan Ppt PowerPoint Presentation File Visuals PDF. This layout presents information on Cyber Security, Confidential Information Leakage, Hacker Changed Password. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
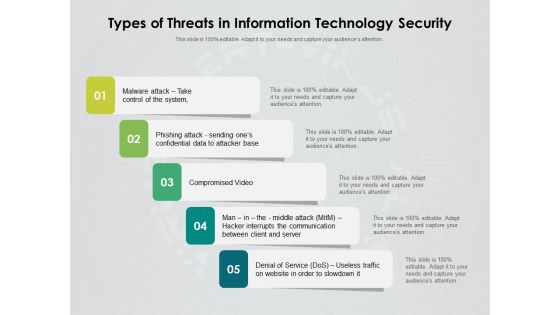
Types Of Threats In Information Technology Security Ppt PowerPoint Presentation Inspiration Rules PDF
Persuade your audience using this types of threats in information technology security ppt powerpoint presentation inspiration rules pdf. This PPT design covers five stages, thus making it a great tool to use. It also caters to a variety of topics including malware attack take control of the system, phishing attack sending ones confidential data to attacker base, compromised video, man in the middle attack hacker interrupts the communication between client and server, denial of service dos, useless traffic on website in order to slowdown it. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Organizing Security Awareness Determining The Actors Behind Most Significant Cyber Mockup PDF
The purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Organizing Security Awareness Determining The Actors Behind Most Significant Cyber Mockup PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.

Common And Prevalent Sources Of Cyber Security Incident Ppt Gallery Themes PDF
The given slide depicts some common sources of cybersecurity threats. It comprises of corporate spies, malicious insiders, hacktivists, terrorist groups, hackers, criminal groups etc. Persuade your audience using this Common And Prevalent Sources Of Cyber Security Incident Ppt Gallery Themes PDF. This PPT design covers seven stages, thus making it a great tool to use. It also caters to a variety of topics including Corporate Spies, Malicious Insiders, Terrorist Group, Hacktivists. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.

Certification Information Technology Professionals Top Hiring Industries For IT Certification Icons PDF
This template covers top hiring industries for certification courses such as ITIL foundation certification, project management professional certification and many others This is a certification information technology professionals salary in different countries icons pdf template with various stages. Focus and dispense information on one stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like project management, ethical hacker, architect certification, developer. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Certification Information Technology Professionals What Are Certification Infographics PDF
This template covers IT certification such as Certified ScrumMaster CSM, AWS Certified Solutions Architect Certification, Certified Ethical Hacker CEH etc, qualification and job description This is a certification information technology professionals what are certification infographics pdf template with various stages. Focus and dispense information on six stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like certification, preparation, fundamentals, practitioners. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Information Technology Certifications Advantages Vendor Certifications List Graphics PDF
This template covers list if vendors who provides the number of certifications for ITIL foundation, certified scrummaster CSM, AWS certified solutions architect certification etc. This is a Information Technology Certifications Advantages Vendor Certifications List Graphics PDF template with various stages. Focus and dispense information on three stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Certified ScrumMaster, Certified Scrum Developer, Certified Ethical Hacker. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Information Technology Certifications Advantages Who Should Take Which Cert Ideas PDF
This template covers details on who should take certified solutions and certification course for certified associate in project management, certified scrum developer CSD certification etc. Presenting Information Technology Certifications Advantages Who Should Take Which Cert Ideas PDF to provide visual cues and insights. Share and navigate important information on two stages that need your due attention. This template can be used to pitch topics like Certified ScrumMaster, Certified Scrum Deve, Certified Ethical Hacker. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Information Technology Certifications Advantages Why Companies Hire Professionals Sample PDF
This template covers reasons why company wants to hire certified professionals for ITIL Foundation certified scrummaster CSM,AWS Certififed solutions architect certification etc. This is a Information Technology Certifications Advantages Why Companies Hire Professionals Sample PDF template with various stages. Focus and dispense information on two stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Certified ScrumMaster, Certified Scrum Developer, Certified Ethical Hacker. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
Block To Multiple Values Lin Centre And On Arms Ppt Business Plan Template PowerPoint Slides
We present our block to multiple values lin centre and on arms ppt business plan template PowerPoint Slides.Download and present our Business PowerPoint Templates because Our PowerPoint Templates and Slides are innately eco-friendly. Their high recall value negate the need for paper handouts. Download our Puzzles or Jigsaws PowerPoint Templates because You are an avid believer in ethical practices. Highlight the benefits that accrue with our PowerPoint Templates and Slides. Present our Shapes PowerPoint Templates because Our PowerPoint Templates and Slides are conceived by a dedicated team. Use them and give form to your wondrous ideas. Download our Process and Flows PowerPoint Templates because You should Ascend the ladder of success with ease. Our PowerPoint Templates and Slides will provide strong and sturdy steps. Present our Leadership PowerPoint Templates because Our PowerPoint Templates and Slides will let Your superior ideas hit the target always and everytime.Use these PowerPoint slides for presentations relating to abstract, binary, business, code, commerce, communication, computer, concept, connect, connection, corporate, cyberspace, data, digital, download, ecommerce, electronic, futuristic, global, hacker, information, internet, multiple, network, networking, online, program, programming, security, software, tech, technology, values. The prominent colors used in the PowerPoint template are Blue, Gray, White.
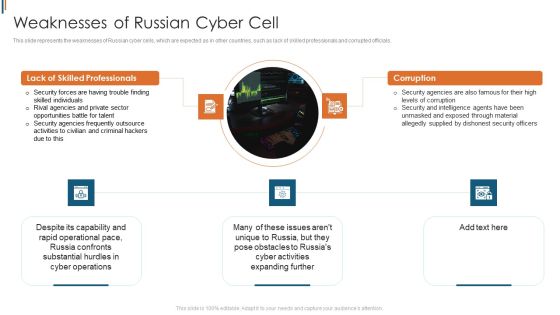
Ukraine Cyberwarfare Weaknesses Of Russian Cyber Cell Brochure Pdf
This slide represents the weaknesses of Russian cyber cells, which are expected as in other countries, such as lack of skilled professionals and corrupted officials. Presenting ukraine cyberwarfare weaknesses of russian cyber cell brochure pdf to provide visual cues and insights. Share and navigate important information on five stages that need your due attention. This template can be used to pitch topics like security forces are having trouble finding skilled individuals, rival agencies and private sector opportunities battle for talent, security agencies frequently outsource activities to civilian and criminal hackers due to this. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Major 5G Protection And Privacy Challenges Themes PDF
The following slide highlights the top safety and protection challenges in 5G network to safeguard sensitive data from hackers. It includes elements such as architecture, security and encryption, location and data privacy etc. Presenting Major 5G Protection And Privacy Challenges Themes PDF to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including Data Privacy, Location Privacy, Security And Encryption. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Naas Integrated Solution IT Virtual Private Network VPN Model Overview Designs PDF
This slide represents the overview of the virtual private network, including its benefits, such as protecting customer information from hackers, preventing internet service provider companies and websites from selling customer data, and so on. Deliver an awe inspiring pitch with this creative Naas Integrated Solution IT Virtual Private Network VPN Model Overview Designs PDF bundle. Topics like Secured Communication, Business, Information can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Russian Cyber Attacks On Ukraine IT Ukraine And Russia Cyber Warfare Impact Information PDF
This slide depicts the Russian vigilante hacker who was able to bring down some official Ukrainian websites and one military website along with his group of 6 hackers. Deliver an awe inspiring pitch with this creative russian cyber attacks on ukraine it ukraine and russia cyber warfare impact information pdf bundle. Topics like ukraine and russia cyber warfare russian vigilante hacker can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Agile Product Life Process Management Role Of Product Manager In Lifecycle Phases Clipart PDF
This slide shows the role of product manager in lifecycle phases such as subject expert, growth hacker, retention strategist and solution seeker with goal and focus areas. This is a agile product life process management role of product manager in lifecycle phases clipart pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like retention strategist, growth hacker, subject expert, solution seeker. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Product Lifecycle Management IT Role Of Product Manager In Lifecycle Phases Themes PDF
This slide shows the role of product manager in lifecycle phases such as subject expert, growth hacker, retention strategist and solution seeker with goal and focus areas. This is a product lifecycle management it role of product manager in lifecycle phases themes pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like subject expert, growth hacker, retention strategist, solution seeker . You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
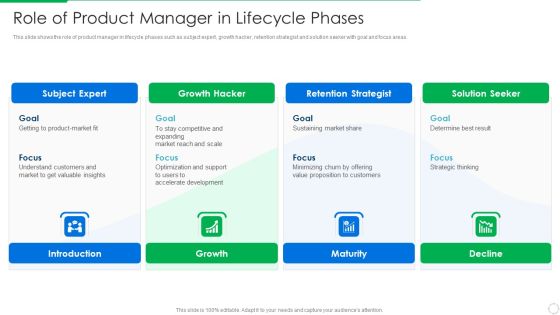
PLM Execution In Company Role Of Product Manager In Lifecycle Phases Sample PDF
This slide shows the role of product manager in lifecycle phases such as subject expert, growth hacker, retention strategist and solution seeker with goal and focus areas. This is a plm execution in company role of product manager in lifecycle phases sample pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like subject expert, growth hacker, retention strategist. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
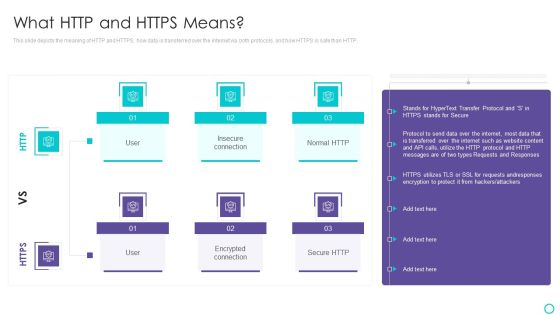
Website Designing And Development Service What HTTP And HTTPS Means Information PDF
This slide depicts the meaning of HTTP and HTTPS, how data is transferred over the internet via both protocols, and how HTTPS is safe than HTTP.Deliver an awe inspiring pitch with this creative Website Designing And Development Service What HTTP And HTTPS Means Information PDF bundle. Topics like Encrypted Connection, Transferred Over The Internet, Hackers Or Attackers can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Information Technology Threat Mitigation Methods Information Technology Risks Form Human Threat Source Ideas PDF
This slide highlights the IT risks form human threat source which includes hacker, computer criminal, terrorist, insiders and industrial espionage with threat description and threat actions. Deliver an awe inspiring pitch with this creative Information Technology Threat Mitigation Methods Information Technology Risks Form Human Threat Source Ideas PDF bundle. Topics like Computer Criminal, Industrial Espionage, System Intrusion can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
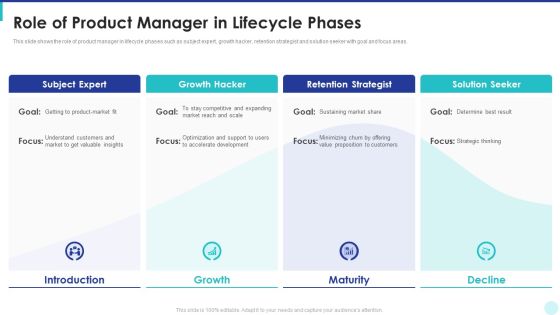
Optimization Of Product Development Life Cycle Role Of Product Manager In Lifecycle Phases Demonstration PDF
This slide shows the role of product manager in lifecycle phases such as subject expert, growth hacker, retention strategist and solution seeker with goal and focus areas. Presenting optimization of product development life cycle role of product manager in lifecycle phases demonstration pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like introduction, growth, maturity, decline. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
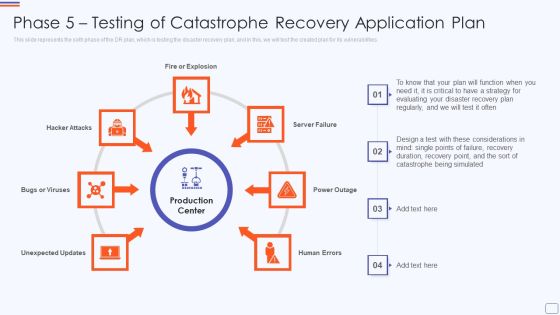
Phase 5 Testing Of Catastrophe Recovery Application Plan Mockup PDF
This slide represents the sixth phase of the DR plan, which is testing the disaster recovery plan, and in this, we will test the created plan for its vulnerabilities. Presenting phase 5 testing of catastrophe recovery application plan mockup pdf to provide visual cues and insights. Share and navigate important information on seven stages that need your due attention. This template can be used to pitch topics like fire or explosion, hacker attacks, server failure, power outage, human errors. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
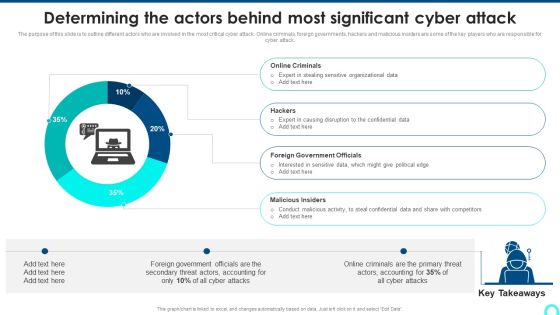
Determining The Actors Behind Most Significant Cyber Attack Download PDF
The purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Deliver and pitch your topic in the best possible manner with this Determining The Actors Behind Most Significant Cyber Attack Download PDF. Use them to share invaluable insights on Online Criminals, Causing Disruption, Government Officials and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Data Breach Threats Stats On Social Media Platforms And Incident Sources Introduction PDF
This slide covers trends on social media data breach incidents reported. It also includes various sources of data theft such as malicious outsider, accidental loss, malicious insider, hacker, etc. Pitch your topic with ease and precision using this Data Breach Threats Stats On Social Media Platforms And Incident Sources Introduction PDF. This layout presents information on Number Breach, Total Incidents, Malicious Insider. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Various Cyber Threats Existing At Workplace Ppt Infographic Template Designs Download PDF
This slide provides information regarding various types of cyberthreats existing at workspace in terms of malware, ransomware, etc. The sources of cyber threats include criminal groups, hackers, etc. From laying roadmaps to briefing everything in detail, our templates are perfect for you. You can set the stage with your presentation slides. All you have to do is download these easy-to-edit and customizable templates. Various Cyber Threats Existing At Workplace Ppt Infographic Template Designs Download PDF will help you deliver an outstanding performance that everyone would remember and praise you for. Do download this presentation today.

Issues Classification Impact And Solutions In Cybersecurity Pictures PDF
This slide presents categories of issues faced in cybersecurity along with impact and solutions, helpful in safeguarding organisation from hackers. It includes malware, password theft, traffic interception an phishing attack Pitch your topic with ease and precision using this Issues Classification Impact And Solutions In Cybersecurity Pictures PDF. This layout presents information on Malware, Password Theft, Traffic Interception. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.
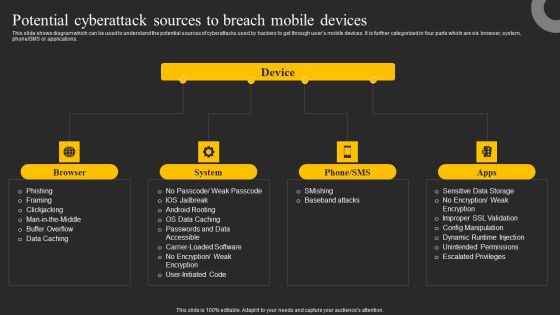
Potential Cyberattack Sources To Breach Mobile Devices Ppt Infographics Graphics Template PDF
This slide shows diagram which can be used to understand the potential sources of cyberattacks used by hackers to get through users mobile devices. It is further categorized in four parts which are via browser, system, phone or SMS or applications. Make sure to capture your audiences attention in your business displays with our gratis customizable Potential Cyberattack Sources To Breach Mobile Devices Ppt Infographics Graphics Template PDF. These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.
Role Of Project Management In Product Life Cycle Phases Infographics PDF
This slide showcase management roles at every phase of product lifecycle manager to reduce or ramp up product in market and includes shortening product development. It include elements such as subject expert, growth hacker, retention strategist and solution seeker. Pitch your topic with ease and precision using this Role Of Project Management In Product Life Cycle Phases Infographics PDF. This layout presents information on Goals, Developing Product, Faster Growth. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

IT System Risk Management Guide Information Technology Risks Form Human Threat Source Mockup PDF
This slide highlights the IT risks form human threat source which includes hacker, computer criminal, terrorist, insiders and industrial espionage with threat description and threat actions. Whether you have daily or monthly meetings, a brilliant presentation is necessary. IT System Risk Management Guide Information Technology Risks Form Human Threat Source Mockup PDF can be your best option for delivering a presentation. Represent everything in detail using IT System Risk Management Guide Information Technology Risks Form Human Threat Source Mockup PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.

Information Technology Risks Form Human Threat Source Summary PDF
This slide highlights the IT risks form human threat source which includes hacker, computer criminal, terrorist, insiders and industrial espionage with threat description and threat actions. If you are looking for a format to display your unique thoughts, then the professionally designed Information Technology Risks Form Human Threat Source Summary PDF is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Information Technology Risks Form Human Threat Source Summary PDF and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.
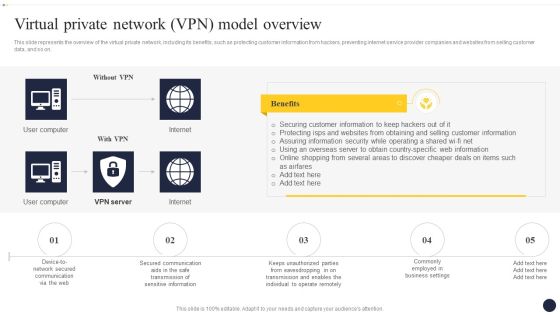
Integrating Naas Service Model To Enhance Virtual Private Network VPN Model Background PDF
This slide represents the overview of the virtual private network, including its benefits, such as protecting customer information from hackers, preventing internet service provider companies and websites from selling customer data, and so on. Are you searching for a Integrating Naas Service Model To Enhance Virtual Private Network VPN Model Background PDF that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort youve put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Integrating Naas Service Model To Enhance Virtual Private Network VPN Model Background PDF from Slidegeeks today.

Integrating Naas Service Model Virtual Private Network Vpn Model Overview Ppt Summary Visuals PDF
This slide represents the overview of the virtual private network, including its benefits, such as protecting customer information from hackers, preventing internet service provider companies and websites from selling customer data, and so on. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest. Look no further than Integrating Naas Service Model Virtual Private Network Vpn Model Overview Ppt Summary Visuals PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Integrating Naas Service Model Virtual Private Network Vpn Model Overview Ppt Summary Visuals PDF today and make your presentation stand out from the rest.

Prevention Of Information Determining The Actors Behind Most Significant Cyber Attack Diagrams PDF
The purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Present like a pro with Prevention Of Information Determining The Actors Behind Most Significant Cyber Attack Diagrams PDF Create beautiful presentations together with your team, using our easy-to-use presentation slides. Share your ideas in real-time and make changes on the fly by downloading our templates. So whether youre in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.

Naas Architectural Framework Virtual Private Network VPN Model Overview Portrait PDF
This slide represents the overview of the virtual private network, including its benefits, such as protecting customer information from hackers, preventing internet service provider companies and websites from selling customer data, and so on. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Naas Architectural Framework Virtual Private Network VPN Model Overview Portrait PDF for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.

Datafy Primary Layers Of Datafication Technology Structure PDF
This slide describes the four layers of datafication technology, including community, care, capacities, and data. The community layer has public and private actors, experts, professionals, hackers, and innovators and the data layer contains tracking, measurement, content and metadata, and detectors. Retrieve professionally designed Datafy Primary Layers Of Datafication Technology Structure PDF to effectively convey your message and captivate your listeners. Save time by selecting pre-made slideshows that are appropriate for various topics, from business to educational purposes. These themes come in many different styles, from creative to corporate, and all of them are easily adjustable and can be edited quickly. Access them as PowerPoint templates or as Google Slides themes. You dont have to go on a hunt for the perfect presentation because Slidegeeks got you covered from everywhere.
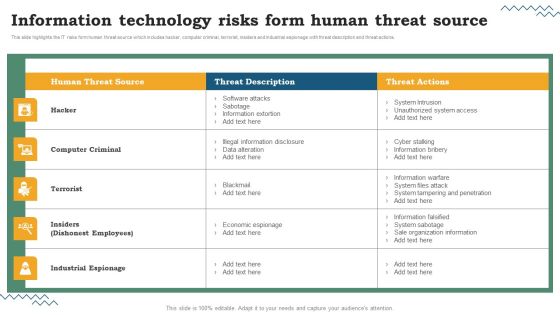
Risk Evaluation Of Information Technology Systems Information Technology Risks Form Human Threat Source Structure PDF
This slide highlights the IT risks form human threat source which includes hacker, computer criminal, terrorist, insiders and industrial espionage with threat description and threat actions. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Risk Evaluation Of Information Technology Systems Information Technology Risks Form Human Threat Source Structure PDF can be your best option for delivering a presentation. Represent everything in detail using Risk Evaluation Of Information Technology Systems Information Technology Risks Form Human Threat Source Structure PDF and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.
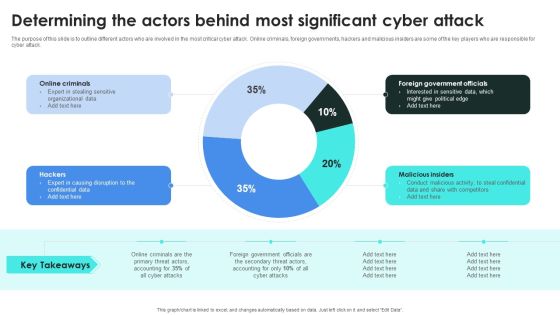
Implementing Cybersecurity Awareness Program To Prevent Attacks Determining The Actors Behind Designs PDF
The purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Present like a pro with Implementing Cybersecurity Awareness Program To Prevent Attacks Determining The Actors Behind Designs PDF Create beautiful presentations together with your team, using our easy to use presentation slides. Share your ideas in real time and make changes on the fly by downloading our templates. So whether you are in the office, on the go, or in a remote location, you can stay in sync with your team and present your ideas with confidence. With Slidegeeks presentation got a whole lot easier. Grab these presentations today.
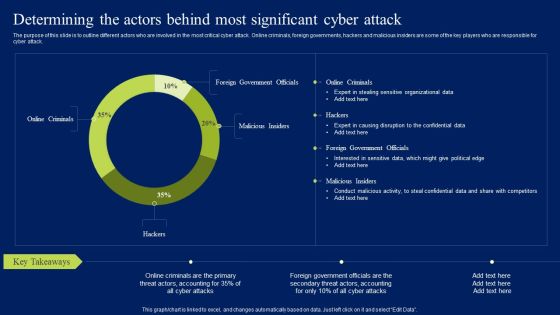
Determining The Actors Behind Most Significant Cyber Attack Ppt Layouts Mockup PDF
The purpose of this slide is to outline different actors who are involved in the most critical cyber attack. Online criminals, foreign governments, hackers and malicious insiders are some of the key players who are responsible for cyber attack. Want to ace your presentation in front of a live audience Our Determining The Actors Behind Most Significant Cyber Attack Ppt Layouts Mockup PDF can help you do that by engaging all the users towards you.. Slidegeeks experts have put their efforts and expertise into creating these impeccable powerpoint presentations so that you can communicate your ideas clearly. Moreover, all the templates are customizable, and easy-to-edit and downloadable. Use these for both personal and commercial use.

Fake Mobile Banking Apps To Steal Funds Ppt Summary Example PDF
This slide shows overview of how fake mobile banking applications works to steal users sensitive information and funds. It also includes details about channels used by hackers to distribute these applications. Do you have to make sure that everyone on your team knows about any specific topic I yes, then you should give Fake Mobile Banking Apps To Steal Funds Ppt Summary Example PDF a try. Our experts have put a lot of knowledge and effort into creating this impeccable Fake Mobile Banking Apps To Steal Funds Ppt Summary Example PDF. You can use this template for your upcoming presentations, as the slides are perfect to represent even the tiniest detail. You can download these templates from the Slidegeeks website and these are easy to edit. So grab these today.
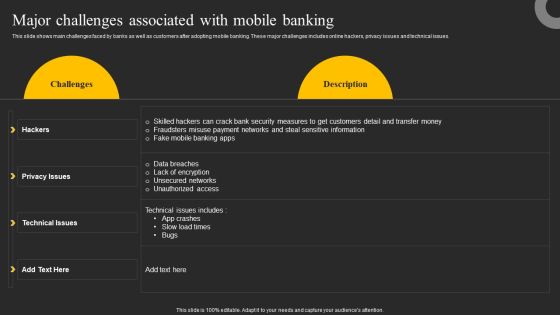
Major Challenges Associated With Mobile Banking Ppt Show Maker PDF
This slide shows main challenges faced by banks as well as customers after adopting mobile banking. These major challenges includes online hackers, privacy issues and technical issues. Find highly impressive Major Challenges Associated With Mobile Banking Ppt Show Maker PDF on Slidegeeks to deliver a meaningful presentation. You can save an ample amount of time using these presentation templates. No need to worry to prepare everything from scratch because Slidegeeks experts have already done a huge research and work for you. You need to download Major Challenges Associated With Mobile Banking Ppt Show Maker PDF for your upcoming presentation. All the presentation templates are 100 percent editable and you can change the color and personalize the content accordingly. Download now.

 Home
Home