Data Protection
Unauthorized Transmission Of Data Vector Icon Ppt PowerPoint Presentation File Smartart PDF
Presenting unauthorized transmission of data vector icon ppt powerpoint presentation file smartart pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including unauthorized transmission of data vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Data Quality Assurance And Safety Vector Icon Ppt PowerPoint Presentation Gallery Background Image PDF
Presenting data quality assurance and safety vector icon ppt powerpoint presentation gallery background image pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including data quality assurance and safety vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
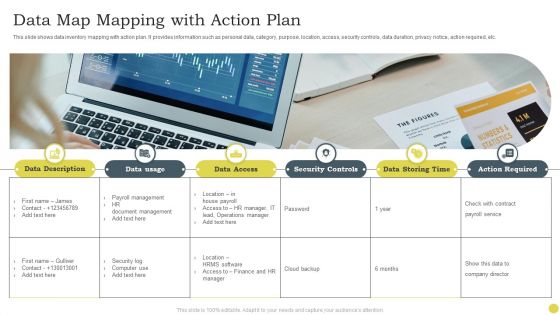
Data Map Mapping With Action Plan Ppt PowerPoint Presentation Gallery Slideshow PDF
This slide shows data inventory mapping with action plan. It provides information such as personal data, category, purpose, location, access, security controls, data duration, privacy notice, action required, etc. Persuade your audience using this Data Map Mapping With Action Plan Ppt PowerPoint Presentation Gallery Slideshow PDF. This PPT design covers six stages, thus making it a great tool to use. It also caters to a variety of topics including Security Controls, Data Storing Time, Payroll Management. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
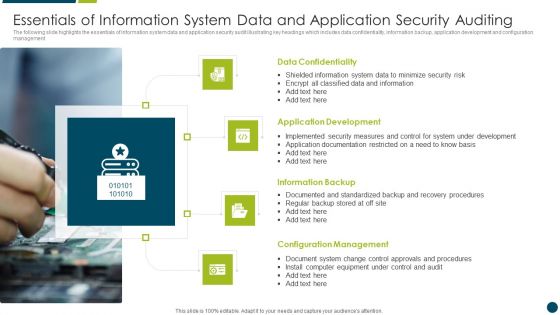
Essentials Of Information System Data And Application Security Auditing Clipart PDF
The following slide highlights the essentials of information system data and application security audit illustrating key headings which includes data confidentiality, information backup, application development and configuration management Persuade your audience using this Essentials Of Information System Data And Application Security Auditing Clipart PDF. This PPT design covers four stages, thus making it a great tool to use. It also caters to a variety of topics including Data Confidentiality, Application Development, Information Backup. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
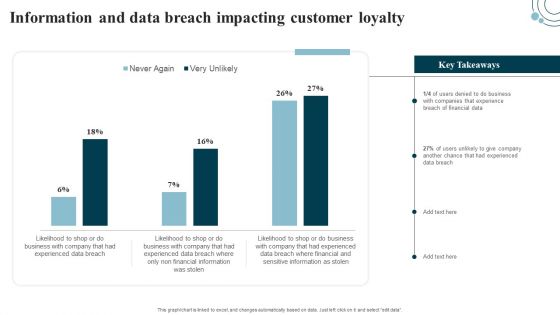
Developing IT Security Strategy Information And Data Breach Impacting Customer Loyalty Template PDF
This graph or chart is linked to excel, and changes automatically based on data. Just left click on it and select edit data. Get a simple yet stunning designed Developing IT Security Strategy Information And Data Breach Impacting Customer Loyalty Template PDF. It is the best one to establish the tone in your meetings. It is an excellent way to make your presentations highly effective. So, download this PPT today from Slidegeeks and see the positive impacts. Our easy-to-edit Developing IT Security Strategy Information And Data Breach Impacting Customer Loyalty Template PDF can be your go-to option for all upcoming conferences and meetings. So, what are you waiting for Grab this template today.

Business Diagram Four Staged Pen Drive Diagram For Data Storage PowerPoint Template
This power point template diagram has been crafted with graphic of four staged pen drive diagram. This PPT contains the concept of data storage. Use this PPT for your business and marketing topics and display related data in a graphical way.

IT Security Prepare Data Backup For Sensitive Information Ppt Portfolio Slide Download PDF
This slide represents the preparation of data backup for sensitive information and how data backup should be created and stored within an organization. Presenting it security prepare data backup for sensitive information ppt portfolio slide download pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like prepare data backup for sensitive information. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Regulations Of Security Tokens In Blockchain Technology Securing Your Data Ppt Slide
This slide discusses the regulations of security tokens for data security. The purpose of this slide is to showcase various security token regulations which include D, A, S regulations, etc. Find a pre-designed and impeccable Regulations Of Security Tokens In Blockchain Technology Securing Your Data Ppt Slide The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

Key Data Threats For School Information Management Systems Ppt PowerPoint Presentation Slides Examples PDF
Presenting key data threats for school information management systems ppt powerpoint presentation slides examples pdf to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including malware, theft and loss, unsafe data, negligence, third party apis application programming interface institutions. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Major Techniques For Project Safety IT Information Security Process To Manage Firms Sensitive Data Designs PDF
This slide provides information about information security process in order to manage firms sensitive data in terms of privileged password management, network security audit checklist, etc. Deliver and pitch your topic in the best possible manner with this major techniques for project safety it information security process to manage firms sensitive data designs pdf. Use them to share invaluable insights on privileged password management, daily tasks performed by network administrator, network security audit checklist and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Executing Advance Data Analytics At Workspace Determine Network Management Architecture Graphics PDF
This slide covers details regarding the network management architecture and standard network management platform including management data browser, network discovery, performance data collector. Deliver an awe inspiring pitch with this creative executing advance data analytics at workspace determine network management architecture graphics pdf bundle. Topics like determine network management architecture can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
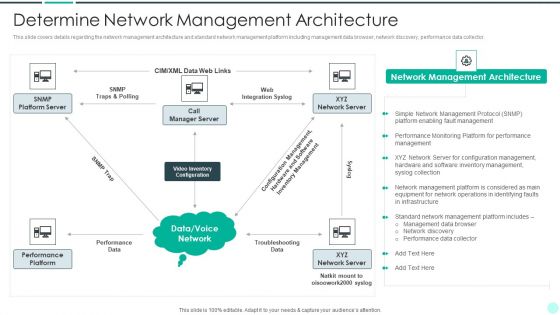
Executing Advance Data Analytics At Workspace Determine Network Management Architecture Brochure PDF
This slide covers details regarding the network management architecture and standard network management platform including management data browser, network discovery, performance data collector. Deliver an awe inspiring pitch with this creative executing advance data analytics at workspace determine network management architecture brochure pdf bundle. Topics like determine network management architecture can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Information Security Key Elements Of Data Security Ppt Pictures Show PDF
This slide represents the different elements of data security such as application security, network security, information security, etc. Presenting information security key elements of data security ppt pictures show pdf to provide visual cues and insights. Share and navigate important information on eight stages that need your due attention. This template can be used to pitch topics like network security, application security, cloud security, operational security, information security. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Executive Information Database System Why We Need Data Warehouse Clipart PDF
This slide represents the need for a data warehouse in the organization, such as data quality, single point for all data for all users, and the complicated problems that can be solved through a data warehouse.Deliver an awe inspiring pitch with this creative Executive Information Database System Why We Need Data Warehouse Clipart PDF bundle. Topics like Security Considerations, Separation Between, Operating Systems can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
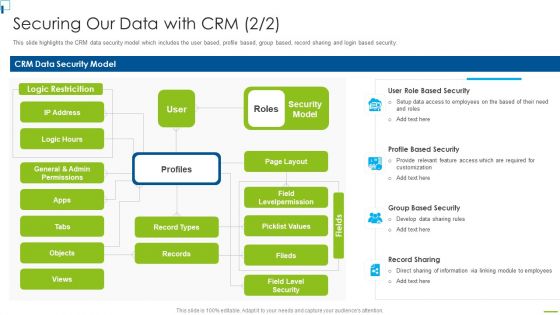
Designing And Deployment Securing Our Data With CRM Ppt PowerPoint Presentation File Backgrounds PDF
This slide highlights the CRM data security model which includes the user based, profile based, group based, record sharing and login based security. This is a designing and deployment securing our data with crm ppt powerpoint presentation file backgrounds pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like crm data security model, security model, profile based security, record sharing, group based security. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
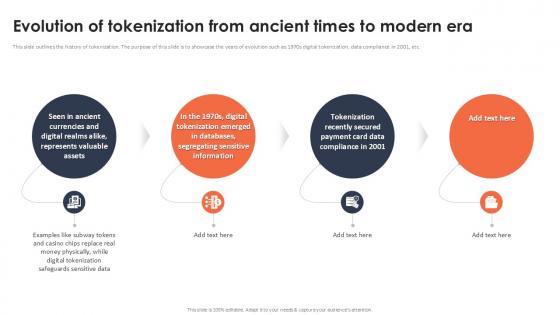
Evolution Of Tokenization From Ancient Times To Modern Era Securing Your Data Ppt Powerpoint
This slide outlines the history of tokenization. The purpose of this slide is to showcase the years of evolution such as 1970s digital tokenization, data compliance in 2001, etc. Make sure to capture your audiences attention in your business displays with our gratis customizable Evolution Of Tokenization From Ancient Times To Modern Era Securing Your Data Ppt Powerpoint These are great for business strategies, office conferences, capital raising or task suggestions. If you desire to acquire more customers for your tech business and ensure they stay satisfied, create your own sales presentation with these plain slides.
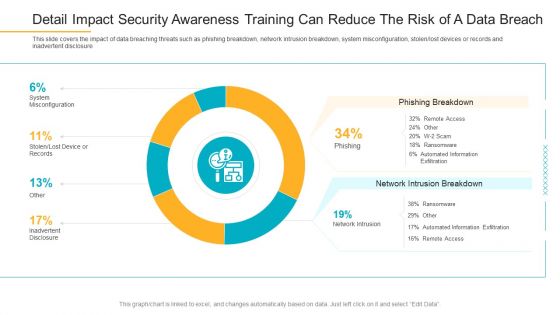
Detail Impact Security Awareness Training Can Reduce The Risk Of A Data Breach Information PDF
This slide covers the impact of data breaching threats such as phishing breakdown, network intrusion breakdown, system misconfiguration, stolen or lost devices or records and inadvertent disclosure. Deliver an awe-inspiring pitch with this creative detail impact security awareness training can reduce the risk of a data breach information pdf bundle. Topics like phishing breakdown, network intrusion breakdown, system misconfiguration can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Best Practices To Increase Data Transparency In Workforce Management Demonstration PDF
This slide represents best practices adopted in workforce management to improve employee data privacy. It provides information regarding ethics, compliance, data security, limit data and internal audit. Presenting Best Practices To Increase Data Transparency In Workforce Management Demonstration PDF to dispense important information. This template comprises eight stages. It also presents valuable insights into the topics including Employee Privacy, Data Collection, Determine. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

About Identity Theft Overview And Techniques Data Breach Prevention Download Pdf
This slide talks about the major crime committed by phishers, named as identity theft. The purpose of this slide is to outline the ways of stealing information, such as robbery, computer fraud, social networking sites, mail theft, and dumpster diving. Create an editable About Identity Theft Overview And Techniques Data Breach Prevention Download Pdf that communicates your idea and engages your audience. Whether you are presenting a business or an educational presentation, pre-designed presentation templates help save time. About Identity Theft Overview And Techniques Data Breach Prevention Download Pdf is highly customizable and very easy to edit, covering many different styles from creative to business presentations. Slidegeeks has creative team members who have crafted amazing templates. So, go and get them without any delay.

Project Security Administration IT Information Security Process To Manage Firms Sensitive Data Contd Graphics PDF
This slide provides information about information security process in order to manage firms sensitive data in terms of firewall audit checklist, VPN configuration, penetrating testing. Deliver and pitch your topic in the best possible manner with this project security administration it information security process to manage firms sensitive data contd graphics pdf. Use them to share invaluable insights on firewall audit checklist, vpn configuration, penetrating testing and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Detail Impact Security Awareness Training Can Reduce The Risk Of A Data Breach Professional PDF
This slide covers the impact of data breaching threats such as phishing breakdown, network intrusion breakdown, system misconfiguration, stolen or lost devices or records and inadvertent disclosure. Deliver an awe-inspiring pitch with this creative detail impact security awareness training can reduce the risk of a data breach professional pdf bundle. Topics like phishing breakdown, network intrusion breakdown can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Detail Impact Security Awareness Training Can Reduce The Risk Of A Data Breach Icons PDF
This slide covers the impact of data breaching threats such as phishing breakdown, network intrusion breakdown, system misconfiguration, stolen or lost devices or records and inadvertent disclosure. Deliver an awe-inspiring pitch with this creative detail impact security awareness training can reduce the risk of a data breach icons pdf bundle. Topics like phishing breakdown, network intrusion breakdown can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Developing Firm Security Strategy Plan Information Security Process To Manage Firms Sensitive Data Contd Brochure PDF
This slide provides information about information security process in order to manage firms sensitive data in terms of firewall audit checklist, VPN configuration, penetrating testing. Presenting developing firm security strategy plan information security process to manage firms sensitive data contd brochure pdf to provide visual cues and insights. Share and navigate important information on three stages that need your due attention. This template can be used to pitch topics like firewall audit checklist, vpn configuration, penetrating testing. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
Information Technology Team Data Security And Communication Plan Icon Graphics PDF
Presenting Information Technology Team Data Security And Communication Plan Icon Graphics PDF to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including Information Technology, Team Data Security, Communication Plan Icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
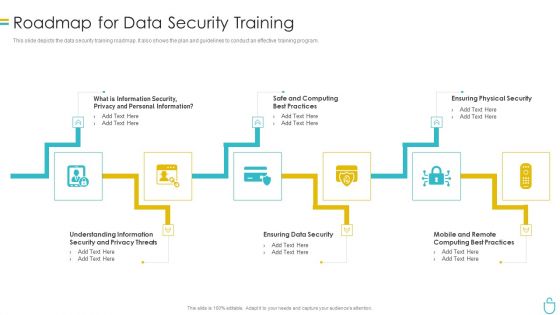
Information Security Roadmap For Data Security Training Ppt Model Show PDF
This slide depicts the data security training roadmap. It also shows the plan and guidelines to conduct an effective training program. This is a information security roadmap for data security training ppt model show pdf template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like information security, ensuring data security, ensuring physical security. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
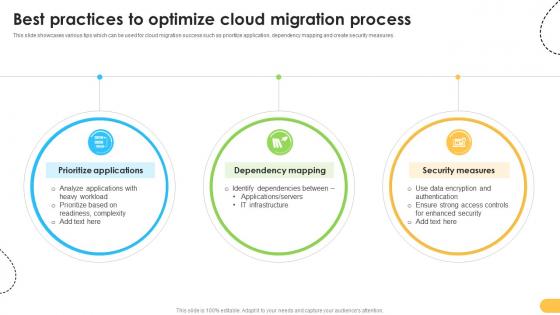
Best Practices To Optimize Cloud Migration Process Data Migration From On Premises
This slide showcases various tips which can be used for cloud migration success such as prioritize application, dependency mapping and create security measures. There are so many reasons you need a Best Practices To Optimize Cloud Migration Process Data Migration From On Premises. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.
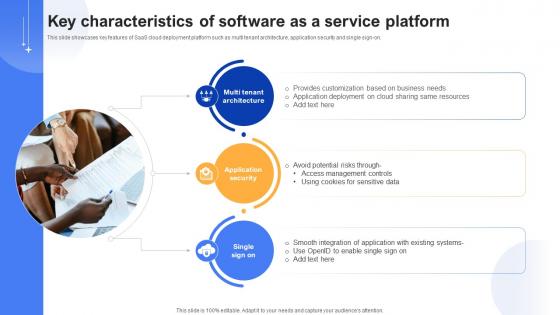
Effective Data Migration Key Characteristics Of Software As A Service Platform
This slide showcases key features of SaaS cloud deployment platform such as multi tenant architecture, application security and single sign-on. Are you searching for a Effective Data Migration Key Characteristics Of Software As A Service Platform that is uncluttered, straightforward, and original Its easy to edit, and you can change the colors to suit your personal or business branding. For a presentation that expresses how much effort you have put in, this template is ideal With all of its features, including tables, diagrams, statistics, and lists, its perfect for a business plan presentation. Make your ideas more appealing with these professional slides. Download Effective Data Migration Key Characteristics Of Software As A Service Platform from Slidegeeks today.

Data Safety Symbol Information Security Gear Ppt PowerPoint Presentation Complete Deck
Presenting this set of slides with name data safety symbol information security gear ppt powerpoint presentation complete deck. The topics discussed in these slides are information, security, data, database server, financial information, gear wheel. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Customer Relationship Management Software Implementation Steps Enable Data Security Formats PDF
This slide covers two ways of enabling data security in CRM systems. It includes options such as IP restrictions and two-factor authentication. Deliver an awe inspiring pitch with this creative Customer Relationship Management Software Implementation Steps Enable Data Security Formats PDF bundle. Topics like Security And Compliance, Factor Authentication, Security Accounts can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Cloud Security Threats Loss Of Data Cloud Computing Security IT Ppt Infographics Graphic Tips PDF
This slide represents the data loss threat of cloud security it is essential to secure organization data and create backups. This is a cloud security threats loss of data cloud computing security it ppt infographics graphic tips pdf template with various stages. Focus and dispense information on four stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like locations, cloud service, strategies, organization. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.

Cloud Information Security Cloud Security Threats Loss Of Data Ppt Layouts Example PDF
This slide represents the data loss threat of cloud security, it is essential to secure organization data and create backups. Presenting Cloud Information Security Cloud Security Threats Loss Of Data Ppt Layouts Example PDF to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like Provider Wisely, Procedures Strategies, Storage Locations. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
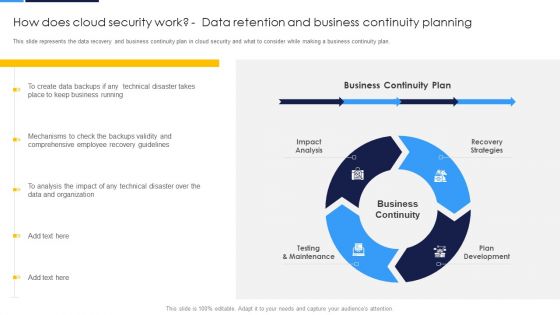
Cloud Security Assessment How Does Cloud Security Work Data Retention And Business Continuity Planning Sample PDF
This slide describes how a cloud security system works and what controls or measures are implemented to secure the data over the cloud.This is a Cloud Security Assessment How Does Cloud Security Work Data Retention And Business Continuity Planning Sample PDF template with various stages. Focus and dispense information on five stages using this creative set, that comes with editable features. It contains large content boxes to add your information on topics like Data Security, Access Management, Business Continuity. You can also showcase facts, figures, and other relevant content using this PPT layout. Grab it now.
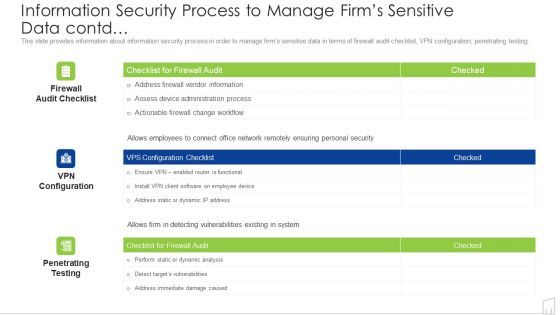
Information Security Process To Manage Firms Sensitive Data Contd Ppt Portfolio Portrait PDF
Deliver and pitch your topic in the best possible manner with this information security process to manage firms sensitive data contd ppt portfolio portrait pdf. Use them to share invaluable insights on information security process to manage firms sensitive data contd and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
Cloud Data Management And Security Model Vector Icon Ppt PowerPoint Presentation File Background PDF
Presenting cloud data management and security model vector icon ppt powerpoint presentation file background pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including cloud data management and security model vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Data Security Private Cloud Vector Icon Ppt PowerPoint Presentation Icon Layouts PDF
Presenting data security private cloud vector icon ppt powerpoint presentation icon layouts pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including data security private cloud vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Security For Cloud Based Systems Icon To Reduce Data Breaches Download PDF
Presenting Security For Cloud Based Systems Icon To Reduce Data Breaches Download PDF to dispense important information. This template comprises Three stages. It also presents valuable insights into the topics including Security For Cloud, Based Systems Icon, Reduce Data Breaches . This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Company Data Security And Management Vector Icon Ppt PowerPoint Presentation Gallery Template PDF
Showcasing this set of slides titled company data security and management vector icon ppt powerpoint presentation gallery template pdf. The topics addressed in these templates are company data security and management vector icon. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
Securing Stored Data Vector Icon Ppt PowerPoint Presentation File Outline PDF
Presenting this set of slides with name securing stored data vector icon ppt powerpoint presentation file outline pdf. This is a one stage process. The stage in this process is securing stored data vector icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
Data Security Management Vector Icon Ppt PowerPoint Presentation Gallery Background PDF
Presenting data security management vector icon ppt powerpoint presentation gallery background pdf to dispense important information. This template comprises one stages. It also presents valuable insights into the topics including data security management vector icon. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.

Statistical Tools For Evidence End To End HR Data And Analytics Management
This slide represents the concise overview of the problem, the proposed solution, and the achieved result for end-to-end HR data and analytics management. The outcomes are providing predictive reporting capabilities, boost platform security, etc. Coming up with a presentation necessitates that the majority of the effort goes into the content and the message you intend to convey. The visuals of a PowerPoint presentation can only be effective if it supplements and supports the story that is being told. Keeping this in mind our experts created Statistical Tools For Evidence End To End HR Data And Analytics Management to reduce the time that goes into designing the presentation. This way, you can concentrate on the message while our designers take care of providing you with the right template for the situation.
Firewall For Online Data Security Vector Icon Ppt PowerPoint Presentation Ideas Sample PDF
Presenting this set of slides with name firewall for online data security vector icon ppt powerpoint presentation ideas sample pdf. This is a three stage process. The stages in this process are firewall for online data security vector icon. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Comparative Analysis Of Security And Utility Token Securing Your Data Ppt Template
This slide highlights the differences between security and utility tokens. The purpose of this slide is to compare security and utility tokens on various aspects such as purpose, expectations, scam potential, etc. Whether you have daily or monthly meetings, a brilliant presentation is necessary. Comparative Analysis Of Security And Utility Token Securing Your Data Ppt Template can be your best option for delivering a presentation. Represent everything in detail using Comparative Analysis Of Security And Utility Token Securing Your Data Ppt Template and make yourself stand out in meetings. The template is versatile and follows a structure that will cater to your requirements. All the templates prepared by Slidegeeks are easy to download and edit. Our research experts have taken care of the corporate themes as well. So, give it a try and see the results.

Cloud Security Assessment Cloud Security Threats Loss Of Data Topics PDF
This slide represents the data loss threat of cloud security it is essential to secure organization data and create backups.Presenting Cloud Security Assessment Cloud Security Threats Loss Of Data Topics PDF to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like Storage Locations, Natural Disasters, Massive Impact. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.

Statistical Data Supporting Steps Taken To Enhance Cyber Ppt Powerpoint Presentation File Outline Pdf
This slide represents the steps taken by cyber security incident management teams of varied enterprises in order to minimize its impact on business operations. It includes steps such as hire skilled individuals etc. The best PPT templates are a great way to save time, energy, and resources. Slidegeeks have 100 percent editable powerpoint slides making them incredibly versatile. With these quality presentation templates, you can create a captivating and memorable presentation by combining visually appealing slides and effectively communicating your message. Download Statistical Data Supporting Steps Taken To Enhance Cyber Ppt Powerpoint Presentation File Outline Pdf from Slidegeeks and deliver a wonderful presentation.

Vector For Cloud Data Management And Security Model Ppt PowerPoint Presentation File Graphics Design PDF
Presenting vector for cloud data management and security model ppt powerpoint presentation file graphics design pdf to dispense important information. This template comprises three stages. It also presents valuable insights into the topics including vector for cloud data management and security model. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Four Steps Arrow For Business Data Security Process Ppt PowerPoint Presentation File Background Image PDF
Presenting four steps arrow for business data security process ppt powerpoint presentation file background image pdf to dispense important information. This template comprises four stages. It also presents valuable insights into the topics including four steps arrow for business data security process. This is a completely customizable PowerPoint theme that can be put to use immediately. So, download it and address the topic impactfully.
Data Governance And Security Model Vector Icon Ppt PowerPoint Presentation Show PDF
Pitch your topic with ease and precision using this data governance and security model vector icon ppt powerpoint presentation show pdf. This layout presents information on data governance and security model vector icon It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Secured Big Data Cloud Architecture And Structure Ppt PowerPoint Presentation Gallery Example PDF
Presenting this set of slides with name secured big data cloud architecture and structure ppt powerpoint presentation gallery example pdf. The topics discussed in these slide is secured big data cloud architecture and structure. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Execution Of ICT Strategic Plan Data Encryption Model For Effective Information Security Guidelines PDF
This slide represents data encryption model for effective information security. It includes data encoding, data decoding, backup repository etc. Crafting an eye catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Execution Of ICT Strategic Plan Data Encryption Model For Effective Information Security Guidelines PDF template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Execution Of ICT Strategic Plan Data Encryption Model For Effective Information Security Guidelines PDF that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers.
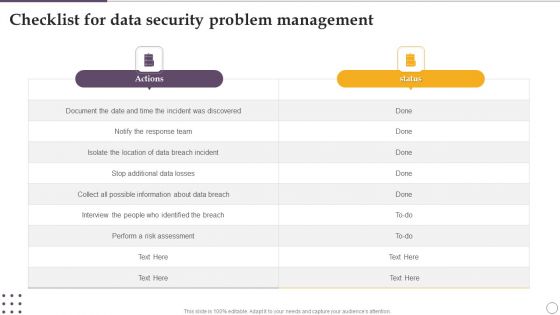
Checklist For Data Security Problem Management Ppt Visual Aids Deck PDF
Showcasing this set of slides titled Checklist For Data Security Problem Management Ppt Visual Aids Deck PDF. The topics addressed in these templates are Actions, Risk Assessment, About Data Breach. All the content presented in this PPT design is completely editable. Download it and make adjustments in color, background, font etc. as per your unique business setting.
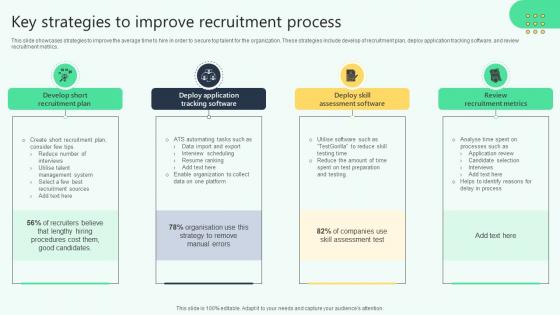
Key Strategies To Improve Recruitment Process Analysing Hr Data For Effective Decision Making
This slide showcases strategies to improve the average time to hire in order to secure top talent for the organization. These strategies include develop of recruitment plan, deploy application tracking software, and review recruitment metrics. Find a pre-designed and impeccable Key Strategies To Improve Recruitment Process Analysing Hr Data For Effective Decision Making. The templates can ace your presentation without additional effort. You can download these easy-to-edit presentation templates to make your presentation stand out from others. So, what are you waiting for Download the template from Slidegeeks today and give a unique touch to your presentation.

Types Of Cloud Migration Testing Methods Data Migration From On Premises
This slide showcases various cloud migration testing models used to analyze application performance such as system, security, recovery testing. Take your projects to the next level with our ultimate collection of Types Of Cloud Migration Testing Methods Data Migration From On Premises. Slidegeeks has designed a range of layouts that are perfect for representing task or activity duration, keeping track of all your deadlines at a glance. Tailor these designs to your exact needs and give them a truly corporate look with your own brand colors they will make your projects stand out from the rest
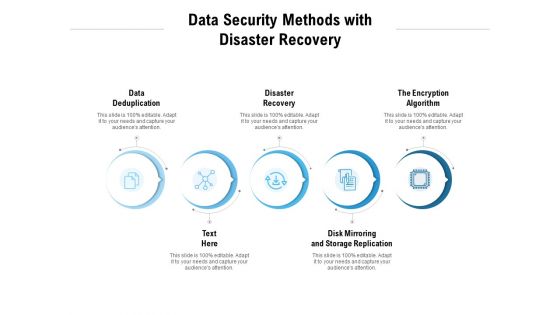
Data Security Methods With Disaster Recovery Ppt PowerPoint Presentation Pictures Vector
Presenting this set of slides with name data security methods with disaster recovery ppt powerpoint presentation pictures vector. This is a five stage process. The stages in this process are data deduplication, disaster recovery, the encryption algorithm, disk mirroring and storage replication. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.
Information Privacy IT Monitor And Detect Abnormal Activity On Sensitive Data Structure PDF
This slide highlights that you will have continuous monitoring and detection of abnormal activities of all the organizations data. Presenting information privacy it monitor and detect abnormal activity on sensitive data structure pdf to provide visual cues and insights. Share and navigate important information on four stages that need your due attention. This template can be used to pitch topics like monitor and detect abnormal activity on sensitive data. In addtion, this PPT design contains high resolution images, graphics, etc, that are easily editable and available for immediate download.
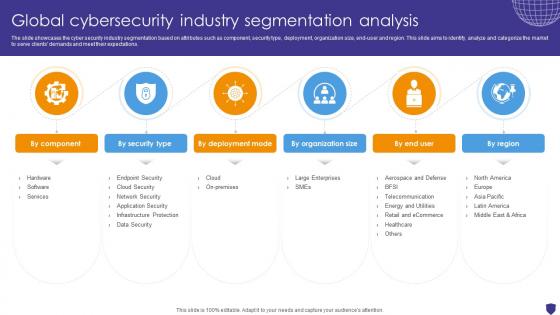
Global Cybersecurity Industry Segmentation Analysis Global Data Security Industry Report IR SS V
The slide showcases the cyber security industry segmentation based on attributes such as component, security type, deployment, organization size, end-user and region. This slide aims to identify, analyze and categorize the market to serve clients demands and meet their expectations. Boost your pitch with our creative Global Cybersecurity Industry Segmentation Analysis Global Data Security Industry Report IR SS V. Deliver an awe-inspiring pitch that will mesmerize everyone. Using these presentation templates you will surely catch everyones attention. You can browse the ppts collection on our website. We have researchers who are experts at creating the right content for the templates. So you do not have to invest time in any additional work. Just grab the template now and use them.

Best Data Security Software Additional Service Offerings For Company Online Database Security Designs PDF
Presenting this set of slides with name best data security software additional service offerings for company online database security designs pdf. This is a three stage process. The stages in this process are software development, security and networking, cloud services. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Best Data Security Software Additional Services For Company Online Database Security Proposal Pictures PDF
Presenting this set of slides with name best data security software additional services for company online database security proposal pictures pdf. The topics discussed in these slides are software development, security and networking, cloud services. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Training Schedule For It Teams To Conduct Tokenization Securing Your Data Ppt Presentation
This slide represents the training schedule for IT teams in an organization to efficiently carry out tokenization. It includes the time slots for training, total days of training, and the modules to be covered in the training. If you are looking for a format to display your unique thoughts, then the professionally designed Training Schedule For It Teams To Conduct Tokenization Securing Your Data Ppt Presentation is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Training Schedule For It Teams To Conduct Tokenization Securing Your Data Ppt Presentation and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.

Application Of Prescriptive Analytics In Supply Chain Data Analytics SS V
This slide outlines various areas where prescriptive analytics may be implemented to improve the working of supply chain. It covers areas such as network design, integrated business planning, inventory optimization with sales and operation execution There are so many reasons you need a Application Of Prescriptive Analytics In Supply Chain Data Analytics SS V. The first reason is you can not spend time making everything from scratch, Thus, Slidegeeks has made presentation templates for you too. You can easily download these templates from our website easily.

Different Phases Of Implementing Tokenization In Ds Securing Your Data Ppt Presentation
This slide highlights the steps for working of tokenization. The purpose of this slide is to outline the various ways of creating token and the phases which include initiating card transaction, producing tokens, etc. Crafting an eye-catching presentation has never been more straightforward. Let your presentation shine with this tasteful yet straightforward Different Phases Of Implementing Tokenization In Ds Securing Your Data Ppt Presentation template. It offers a minimalistic and classy look that is great for making a statement. The colors have been employed intelligently to add a bit of playfulness while still remaining professional. Construct the ideal Different Phases Of Implementing Tokenization In Ds Securing Your Data Ppt Presentation that effortlessly grabs the attention of your audience Begin now and be certain to wow your customers

 Home
Home