AI PPT Maker
Templates
PPT Bundles
Design Services
Business PPTs
Business Plan
Management
Strategy
Introduction PPT
Roadmap
Self Introduction
Timelines
Process
Marketing
Agenda
Technology
Medical
Startup Business Plan
Cyber Security
Dashboards
SWOT
Proposals
Education
Pitch Deck
Digital Marketing
KPIs
Project Management
Product Management
Artificial Intelligence
Target Market
Communication
Supply Chain
Google Slides
Research Services
 One Pagers
One PagersAll Categories
-
Home
- Customer Favorites
- Business Risks
Business Risks
Problem Diagnosis Ppt PowerPoint Presentation Complete Deck With Slides
Boost your confidence and team morale with this well-structured Problem Diagnosis Ppt PowerPoint Presentation Complete Deck With Slides. This prefabricated set gives a voice to your presentation because of its well-researched content and graphics. Our experts have added all the components very carefully, thus helping you deliver great presentations with a single click. Not only that, it contains a set of fifteen slides that are designed using the right visuals, graphics, etc. Various topics can be discussed, and effective brainstorming sessions can be conducted using the wide variety of slides added in this complete deck. Apart from this, our PPT design contains clear instructions to help you restructure your presentations and create multiple variations. The color, format, design anything can be modified as deemed fit by the user. Not only this, it is available for immediate download. So, grab it now.

Analyse And Rank Impact Of Cyber Threat Ppt PowerPoint Presentation Diagram PDF
The following slide highlights the prioritization of cyber security threats to minimize possibility of likelihood and severity. It mainly includes elements such as vulnerability, threat, source, likelihood, impact and ranking etc. Do you have an important presentation coming up Are you looking for something that will make your presentation stand out from the rest Look no further than Analyse And Rank Impact Of Cyber Threat Ppt PowerPoint Presentation Diagram PDF. With our professional designs, you can trust that your presentation will pop and make delivering it a smooth process. And with Slidegeeks, you can trust that your presentation will be unique and memorable. So why wait Grab Analyse And Rank Impact Of Cyber Threat Ppt PowerPoint Presentation Diagram PDF today and make your presentation stand out from the rest.

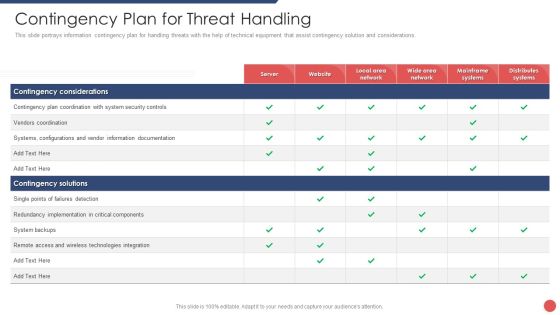
Information And Technology Security Operations Contingency Plan For Threat Handling Clipart PDF
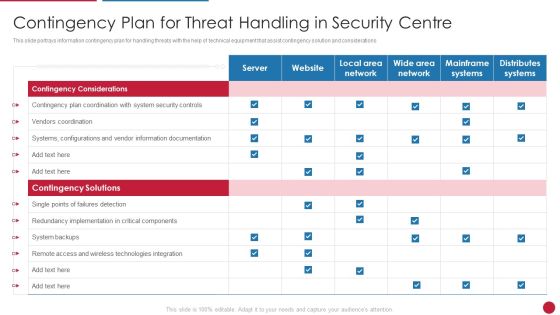
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an awe inspiring pitch with this creative information and technology security operations contingency plan for threat handling clipart pdf bundle. Topics like contingency considerations, mainframe systems, security, implementation, technologies integration can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Security Functioning Centre Contingency Plan For Threat Handling Ppt Layouts Outline PDF
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an awe inspiring pitch with this creative security functioning centre contingency plan for threat handling ppt layouts outline pdf bundle. Topics like technologies integration, server, distributes systems can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
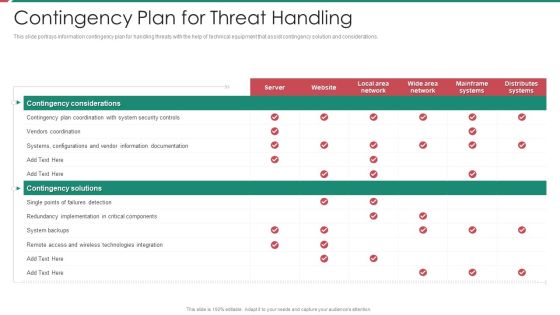
Security And Process Integration Contingency Plan For Threat Handling Template PDF
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an awe inspiring pitch with this creative security and process integration contingency plan for threat handling template pdf bundle. Topics like contingency considerations, mainframe systems, security, implementation, technologies integration can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Contingency Plan For Managing Threats To Ensure IT Project Safety Ppt Icon Layout Ideas PDF
This slide provides information regarding contingency plan for managing threats to ensure IT project safety with aid of technical equipment ensuring contingency plans. Deliver and pitch your topic in the best possible manner with this contingency plan for managing threats to ensure it project safety ppt icon layout ideas pdf. Use them to share invaluable insights on system, security, technologies, implementation and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Mitigating Cybersecurity Threats And Vulnerabilities Contingency Plan For Cyber Infographics PDF
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver and pitch your topic in the best possible manner with this mitigating cybersecurity threats and vulnerabilities contingency plan for cyber infographics pdf. Use them to share invaluable insights on contingency solutions, contingency considerations and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Security Information And Event Management Real Time Assessment Of Security Threats Template PDF
This slide covers the SIEM dashboard which focuses on threat activity, log and event trend, log source, impacted hosts, log classification. Deliver an awe inspiring pitch with this creative security information and event management real time assessment of security threats template pdf bundle. Topics like security information and event management dashboard can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
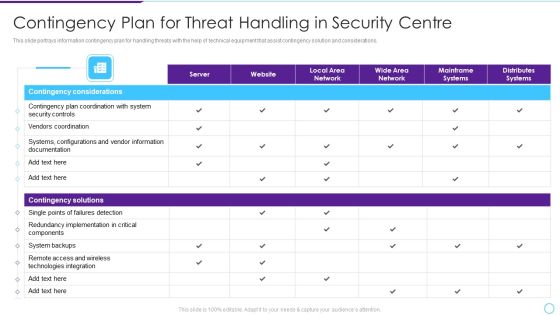
Intelligent Infrastructure Contingency Plan For Threat Handling In Security Centre Mockup PDF
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver an awe inspiring pitch with this creative Intelligent Infrastructure Contingency Plan For Threat Handling In Security Centre Mockup PDF bundle. Topics like Contingency Considerations, Contingency Solutions, Server, Local Area Network, Local Area Network can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Facilitating IT Intelligence Architecture Contingency Plan For Threat Handling In Security Centre Professional PDF
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations Deliver and pitch your topic in the best possible manner with this Facilitating IT Intelligence Architecture Contingency Plan For Threat Handling In Security Centre Professional PDF Use them to share invaluable insights on Contingency Solutions, Contingency Considerations, Information Documentation and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

5G Technology Development For Digital Transformation Key Security Considerations For 5G For Threat Handling Themes PDF
This slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Here you can discover an assortment of the finest PowerPoint and Google Slides templates. With these templates, you can create presentations for a variety of purposes while simultaneously providing your audience with an eye catching visual experience. Download 5G Technology Development For Digital Transformation Key Security Considerations For 5G For Threat Handling Themes PDF to deliver an impeccable presentation. These templates will make your job of preparing presentations much quicker, yet still, maintain a high level of quality. Slidegeeks has experienced researchers who prepare these templates and write high quality content for you. Later on, you can personalize the content by editing the 5G Technology Development For Digital Transformation Key Security Considerations For 5G For Threat Handling Themes PDF.
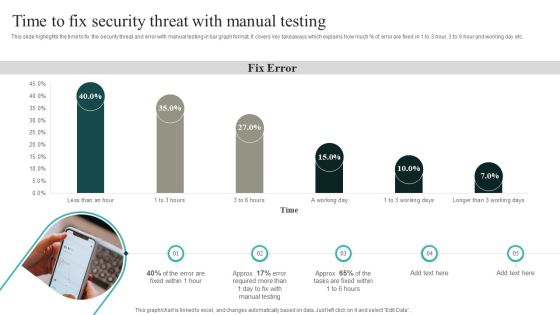
IT Security Automation Systems Guide Time To Fix Security Threat With Manual Testing Topics PDF
This slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Formulating a presentation can take up a lot of effort and time, so the content and message should always be the primary focus. The visuals of the PowerPoint can enhance the presenters message, so our IT Security Automation Systems Guide Time To Fix Security Threat With Manual Testing Topics PDF was created to help save time. Instead of worrying about the design, the presenter can concentrate on the message while our designers work on creating the ideal templates for whatever situation is needed. Slidegeeks has experts for everything from amazing designs to valuable content, we have put everything into IT Security Automation Systems Guide Time To Fix Security Threat With Manual Testing Topics PDF
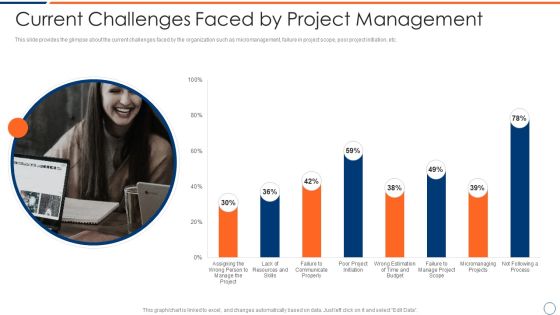
How To Intensify Project Threats Current Challenges Faced By Project Management Elements PDF
This slide provides the glimpse about the current challenges faced by the organization such as micromanagement, failure in project scope, poor project initiation, etc. Deliver an awe inspiring pitch with this creative how to intensify project threats current challenges faced by project management elements pdf bundle. Topics like resources, budget, process, communicate can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

How To Intensify Project Threats Dashboard For Managing Project Issues Inspiration PDF
This slide provides the glimpse about the KPI for managing project issues in the organization wherein focus is on project health, tasks, progress, time, cost and workload. Deliver and pitch your topic in the best possible manner with this how to intensify project threats dashboard for managing project issues inspiration pdf. Use them to share invaluable insights on time, cost, workload, progress, tasks and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Evolving BI Infrastructure Contingency Plan For Threat Handling In Security Centre Pictures PDF
This slide portrays information contingency plan for handling threats with the help of technical equipment that assist contingency solution and considerations. Deliver and pitch your topic in the best possible manner with this evolving bi infrastructure contingency plan for threat handling in security centre pictures pdf. Use them to share invaluable insights on server, website, local area network, wide area network, mainframe systems, distributes systems and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Project Security Administration IT Contingency Plan For Managing Threats To Ensure It Project Safety Mockup PDF
This slide provides information regarding contingency plan for managing threats to ensure IT project safety with aid of technical equipment ensuring contingency plans. Deliver an awe inspiring pitch with this creative project security administration it contingency plan for managing threats to ensure it project safety mockup pdf bundle. Topics like distributes systems, mainframe systems, wide area network, local area network, website can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Cyber Safety Incident Management Key Activities Checklist Associated To Insider Threat Program Download PDF
This slide provides details regarding checklist associated to insider threat program in terms of plan and collect, review and analyze and strategic framework development. Deliver and pitch your topic in the best possible manner with this cyber safety incident management key activities checklist associated to insider threat program download pdf. Use them to share invaluable insights on plan and collet, review and analyze, develop strategic framework, key activities and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
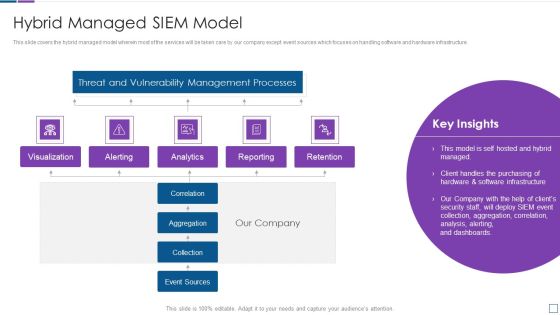
Real Time Assessment Of Security Threats Hybrid Managed SIEM Model Brochure PDF
This slide covers the hybrid managed model wherein most of the services will be taken care by our company except event sources which focuses on handling software and hardware infrastructure. Deliver an awe inspiring pitch with this creative real time assessment of security threats hybrid managed siem model brochure pdf bundle. Topics like threat and vulnerability management processes, reporting, retention, correlation, collection can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

5G Evolution Architectural Technology Key Security Considerations For 5G For Threat Handling Sample PDF
This slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver and pitch your topic in the best possible manner with this 5G Evolution Architectural Technology Key Security Considerations For 5G For Threat Handling Sample PDF Use them to share invaluable insights on Concerns To Catered, Handling Initiatives, Implementing Middleware and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Key Security Considerations For 5G For Threat Handling 5G Network Architecture Instructions Diagrams PDF
This slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. Deliver and pitch your topic in the best possible manner with this Key Security Considerations For 5G For Threat Handling 5G Network Architecture Instructions Diagrams PDF. Use them to share invaluable insights on Nodes Authentication, Rule Consistency, Policy Enforcement and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Comparative Analysis Of Insider Threat In Cyber Security Detection Software Guidelines PDF
This slide shows comparison of software available for detecting insider threat. It provides information about tools, features, user reviews, detection rate, free trial and pricing. Pitch your topic with ease and precision using this Comparative Analysis Of Insider Threat In Cyber Security Detection Software Guidelines PDF. This layout presents information on User Reviews, Detection Rate, Free Trial. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Insider Threat In Cyber Security Discovery Flowchart Of IT Company Template PDF
This slide shows information technology company flowchart indicating insider threat discovery. It provides information such as user request for service, authentication check, starting session, role based access control RBAC, permission checks, etc. Persuade your audience using this Insider Threat In Cyber Security Discovery Flowchart Of IT Company Template PDF. This PPT design covers one stages, thus making it a great tool to use. It also caters to a variety of topics including Terminate Session, Allow Access, Authentication Service. Download this PPT design now to present a convincing pitch that not only emphasizes the topic but also showcases your presentation skills.
Insider Threat In Cyber Security Tracking Dashboard With User Details Portrait PDF
This slide shows user details tracked by insider threat dashboard. It provides information such as exposure events, file activity, archive, document, image, pdf, ppt, scripts, etc. Pitch your topic with ease and precision using this Insider Threat In Cyber Security Tracking Dashboard With User Details Portrait PDF. This layout presents information on Private Data, Exposure Events, User Activity, File Activity, Over Time. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

IT Security Automation Tools Integration Time To Fix Security Threat With Manual Testing Template PDF
This slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much percent of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc. Deliver and pitch your topic in the best possible manner with this IT Security Automation Tools Integration Time To Fix Security Threat With Manual Testing Template PDF. Use them to share invaluable insights on Manual Testing, Fix Error, 3 Working Days and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Security Automation To Analyze And Mitigate Cyberthreats Time To Fix Security Threat Ideas PDF
This slide highlights the time to fix the security threat and error with manual testing in bar graph format. It covers key takeaways which explains how much of error are fixed in 1 to 3 hour, 3 to 6 hour and working day etc.The best PPT templates are a great way to save time, energy, and resources. Slidegeeks have 100 precent editable powerpoint slides making them incredibly versatile. With these quality presentation templates, you can create a captivating and memorable presentation by combining visually appealing slides and effectively communicating your message. Download Security Automation To Analyze And Mitigate Cyberthreats Time To Fix Security Threat Ideas PDF from Slidegeeks and deliver a wonderful presentation.
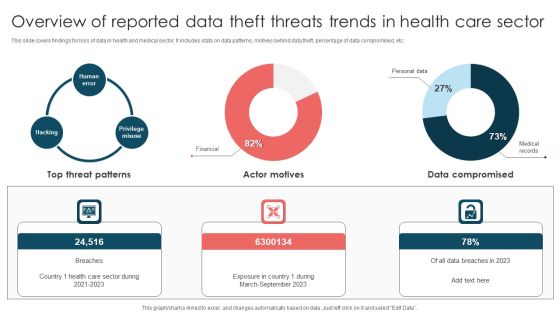
Overview Of Reported Data Theft Threats Trends In Health Care Sector Introduction PDF
This slide covers findings for loss of data in health and medical sector. It includes stats on data patterns, motives behind data theft, percentage of data compromised, etc. Pitch your topic with ease and precision using this Overview Of Reported Data Theft Threats Trends In Health Care Sector Introduction PDF. This layout presents information on Top Threat Patterns, Exposure Country, March To September 2023. It is also available for immediate download and adjustment. So, changes can be made in the color, design, graphics or any other component to create a unique layout.

Critical Measures For Ensuring Contingency Plan For Threat Handling At Workplace Graphics PDF
This slide portrays information contingency plan for handling threats at workplace with the help of technical equipment that assist contingency solution and considerations. Slidegeeks is one of the best resources for PowerPoint templates. You can download easily and regulate Critical Measures For Ensuring Contingency Plan For Threat Handling At Workplace Graphics PDF for your personal presentations from our wonderful collection. A few clicks is all it takes to discover and get the most relevant and appropriate templates. Use our Templates to add a unique zing and appeal to your presentation and meetings. All the slides are easy to edit and you can use them even for advertisement purposes.
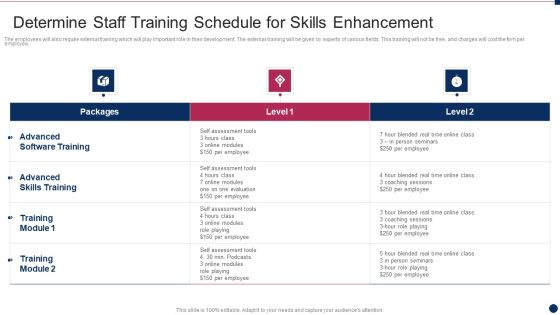
Threat Management At Workplace Determine Staff Training Schedule For Skills Enhancement Graphics Pdf
The employees will also require external training which will play important role in their development. The external training will be given by experts of various fields. This training will not be free, and charges will cost the firm per employee. Deliver and pitch your topic in the best possible manner with this threat management at workplace determine staff training schedule for skills enhancement graphics pdf. Use them to share invaluable insights on advanced skills training, advanced software training, blended real time and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Threat Control Dashboard With High And Average Levels Ppt PowerPoint Presentation File Outline PDF
Presenting this set of slides with name threat control dashboard with high and average levels ppt powerpoint presentation file outline pdf. The topics discussed in these slides are governance, industrials, monitored. This is a completely editable PowerPoint presentation and is available for immediate download. Download now and impress your audience.

Opportunities And Threats For Penetrating In New Market Segments Local Partner Selection Professional PDF
Deliver an awe inspiring pitch with this creative opportunities and threats for penetrating in new market segments local partner selection professional pdf bundle. Topics like technical capabilities, industry attractiveness, unique competencies, complementary capabilities can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
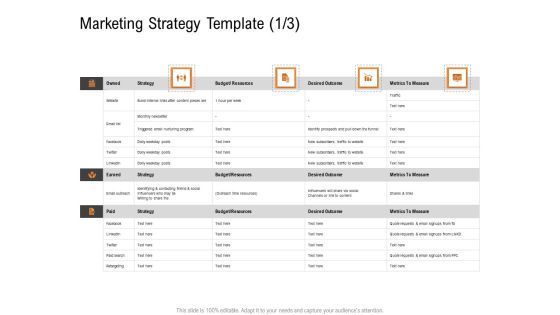
Opportunities And Threats For Penetrating In New Market Segments Marketing Strategy Template Budget Structure PDF
Deliver an awe inspiring pitch with this creative opportunities and threats for penetrating in new market segments marketing strategy template budget structure pdf bundle. Topics like strategy, budget or resources, desired outcome, metrics to measure can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
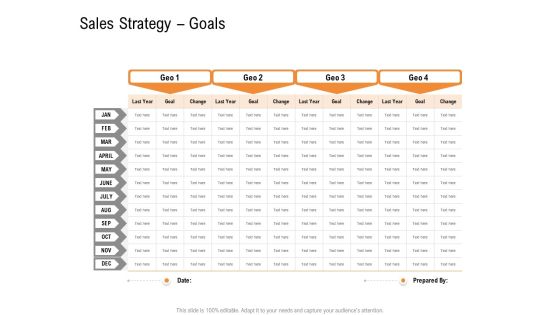
Opportunities And Threats For Penetrating In New Market Segments Sales Strategy Goals Professional PDF
Deliver an awe inspiring pitch with this creative opportunities and threats for penetrating in new market segments sales strategy goals professional pdf bundle. Topics like sales strategy goals can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Opportunities And Threats For Penetrating In New Market Segments Expansion Goals Inspiration PDF
Deliver an awe inspiring pitch with this creative opportunities and threats for penetrating in new market segments expansion goals inspiration pdf bundle. Topics like expansion goals can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
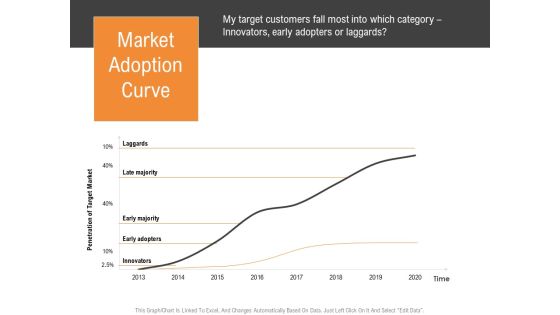
Opportunities And Threats For Penetrating In New Market Segments Market Adoption Curve Elements PDF
Deliver and pitch your topic in the best possible manner with this opportunities and threats for penetrating in new market segments market adoption curve elements pdf. Use them to share invaluable insights on market adoption curve and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
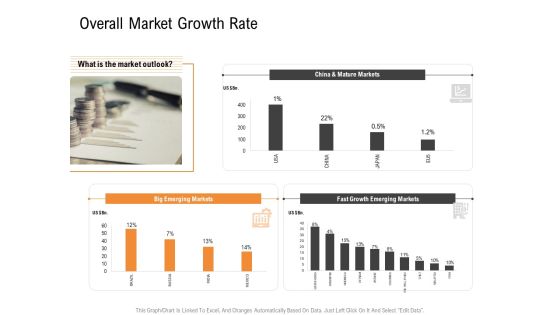
Opportunities And Threats For Penetrating In New Market Segments Overall Market Growth Rate Summary PDF
Deliver an awe inspiring pitch with this creative opportunities and threats for penetrating in new market segments overall market growth rate summary pdf bundle. Topics like overall market growth rate can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Table Of Contents For How To Intensify Project Threats Information PDF
Deliver an awe inspiring pitch with this creative table of contents for how to intensify project threats information pdf bundle. Topics like challenges and solutions, current state analysis, implementation plan, project management dashboard, escalation team details can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
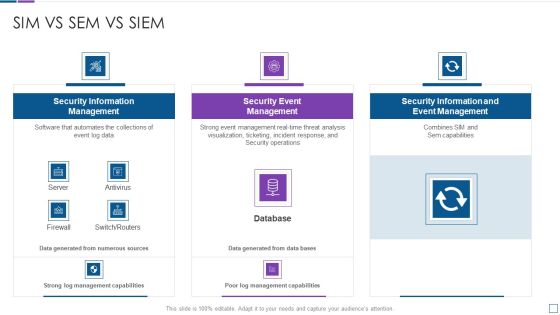
Real Time Assessment Of Security Threats Sim Vs Sem Vs SIEM Diagrams PDF
Deliver an awe inspiring pitch with this creative real time assessment of security threats sim vs sem vs siem diagrams pdf bundle. Topics like security information management, security event management, security information and event management can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Table Of Contents For Developing Cyber Security Threat Awareness Staff Training Program Contd Topics PDF
Deliver an awe inspiring pitch with this creative Table Of Contents For Developing Cyber Security Threat Awareness Staff Training Program Contd Topics PDF bundle. Topics like Security Awareness, Current Assessment, Security Standard can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Table Of Contents For Developing Cyber Security Threat Awareness Staff Training Program Slide Microsoft PDF
Deliver and pitch your topic in the best possible manner with this Table Of Contents For Developing Cyber Security Threat Awareness Staff Training Program Slide Microsoft PDF. Use them to share invaluable insights on Current Assessment, Determining Actors, Understanding Frequency and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Estimating Total Cost Of Ownership Of SIEM Real Time Assessment Of Security Threats Infographics PDF
This slide covers the cost breakdown of SIEM solution based on initial expenses, recurring expenses and amount saved by the client if they choose our company. Deliver and pitch your topic in the best possible manner with this estimating total cost of ownership of siem real time assessment of security threats infographics pdf. Use them to share invaluable insights on ongoing expenses, cost breakdown, siem solution and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Current Versus Target Level Assessment For Anti Fraud Program Fraud Threat Administration Guide Microsoft PDF
Following slide depicts information about the various levels of an enterprise anti-fraud program. It also delineates details about the organizations current versus targeted level in relation to various program attributes.Deliver an awe inspiring pitch with this creative Current Versus Target Level Assessment For Anti Fraud Program Fraud Threat Administration Guide Microsoft PDF bundle. Topics like Programmed Attribute, Fraud Investigation, Monitoring Activities can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
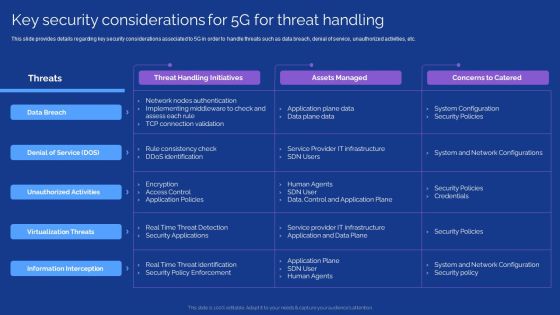
Development Guide For 5G World Key Security Considerations For 5G For Threat Handling Slides PDF
This slide provides details regarding key security considerations associated to 5G in order to handle threats such as data breach, denial of service, unauthorized activities, etc. This modern and well arranged Development Guide For 5G World Key Security Considerations For 5G For Threat Handling Slides PDF provides lots of creative possibilities. It is very simple to customize and edit with the Powerpoint Software. Just drag and drop your pictures into the shapes. All facets of this template can be edited with Powerpoint no extra software is necessary. Add your own material, put your images in the places assigned for them, adjust the colors, and then you can show your slides to the world, with an animated slide included.

Industry Report Of Packaged Food Products Part 1 Kellogg Threats Graphics PDF
If you are looking for a format to display your unique thoughts, then the professionally designed Industry Report Of Packaged Food Products Part 1 Kellogg Threats Graphics PDF is the one for you. You can use it as a Google Slides template or a PowerPoint template. Incorporate impressive visuals, symbols, images, and other charts. Modify or reorganize the text boxes as you desire. Experiment with shade schemes and font pairings. Alter, share or cooperate with other people on your work. Download Industry Report Of Packaged Food Products Part 1 Kellogg Threats Graphics PDF and find out how to give a successful presentation. Present a perfect display to your team and make your presentation unforgettable.
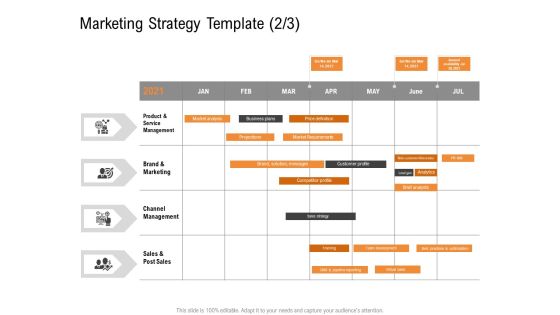
Opportunities And Threats For Penetrating In New Market Segments Marketing Strategy Template Channel Diagrams PDF
Product Launch marketing Plan schedule. Deliver and pitch your topic in the best possible manner with this opportunities and threats for penetrating in new market segments marketing strategy template channel diagrams pdf. Use them to share invaluable insights on product and service management, brand and marketing, channel management, sales and post sales and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.
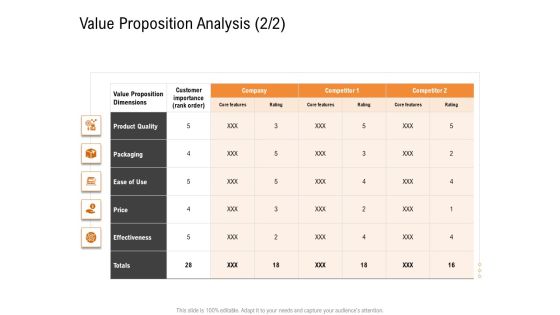
Opportunities And Threats For Penetrating In New Market Segments Value Proposition Analysis Price Structure PDF
How attractive is the value proposition via-a-vis competitors. Deliver an awe inspiring pitch with this creative opportunities and threats for penetrating in new market segments value proposition analysis price structure pdf bundle. Topics like product quality, packaging, ease of use, price, effectiveness can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

Environmental Assessment STEP Analysis For Opportunity And Threat Evaluation Ppt Gallery Templates PDF
This slide shows STEP analysis to analyze likelihood, importance and influence of political, economic, social and technological factors on organizational activities Deliver an awe inspiring pitch with this creative environmental assessment step analysis for opportunity and threat evaluation ppt gallery templates pdf bundle. Topics like economic, technological, social can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
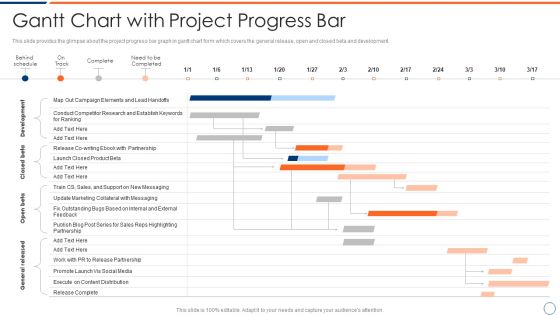
How To Intensify Project Threats Gantt Chart With Project Progress Bar Elements PDF
This slide provides the glimpse about the project progress bar graph in gantt chart form which covers the general release, open and closed beta and development. Deliver an awe inspiring pitch with this creative how to intensify project threats gantt chart with project progress bar elements pdf bundle. Topics like development, closed beta, open beta, general released. can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
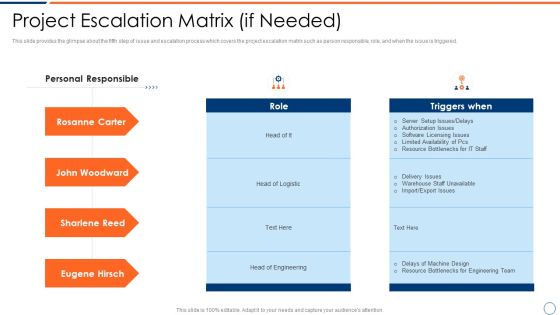
How To Intensify Project Threats Project Escalation Matrix If Needed Introduction PDF
This slide provides the glimpse about the fifth step of issue and escalation process which covers the project escalation matrix such as person responsible, role, and when the issue is triggered. Deliver an awe inspiring pitch with this creative how to intensify project threats project escalation matrix if needed introduction pdf bundle. Topics like project escalation matrix if needed can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
How To Intensify Project Threats Project Performance Tracking And Reporting Structure PDF
This slide provides the glimpse about the fourth step of issue and escalation process which covers the project name, start and finish, work duration, costs, etc. Deliver an awe inspiring pitch with this creative how to intensify project threats project performance tracking and reporting structure pdf bundle. Topics like project name, start and finish, work duration, costs can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

How To Intensify Project Threats Project Validation And Prioritization Brochure PDF
This slide provides the glimpse about the second step of issue and escalation process which covers the project validation and prioritization along with the features and different projects initiatives. Deliver and pitch your topic in the best possible manner with this how to intensify project threats project validation and prioritization brochure pdf. Use them to share invaluable insights on strategic fit, economic impact, feasibility and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

How To Intensify Project Threats Delay And Over Run Cost In The Projects Topics PDF
This slide provides the glimpse about the delay and over run project costs graph wherein the number of projects has been monitored, along with delayed projects and cost overrun. Deliver an awe inspiring pitch with this creative how to intensify project threats delay and over run cost in the projects topics pdf bundle. Topics like monitored, delayed projects, cost overrun can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
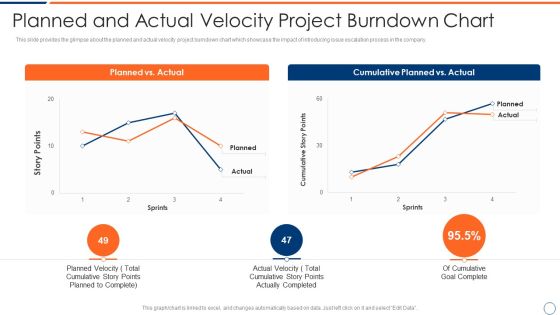
How To Intensify Project Threats Planned And Actual Velocity Project Burndown Chart Summary PDF
This slide provides the glimpse about the planned and actual velocity project burndown chart which showcase the impact of introducing issue escalation process in the company. Deliver an awe inspiring pitch with this creative how to intensify project threats planned and actual velocity project burndown chart summary pdf bundle. Topics like planned vs actual, cumulative planned vs actual can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.

How To Intensify Project Threats Project Issues Management Dashboard Clipart PDF
This slide provides the glimpse about the project issues wherein focus is on number of reported issues, unresolved issues and issues allocated per resources. Deliver and pitch your topic in the best possible manner with this how to intensify project threats project issues management dashboard clipart pdf. Use them to share invaluable insights on project issues management dashboard and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Competitive Advantage Real Time Assessment Of Security Threats SIEM Pictures PDF
This slide covers the competitive advantage scoring for security information and event management based on different factors such as value, deployment, ease of use, support, etc. Deliver an awe inspiring pitch with this creative competitive advantage real time assessment of security threats siem pictures pdf bundle. Topics like siem competitive advantage can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
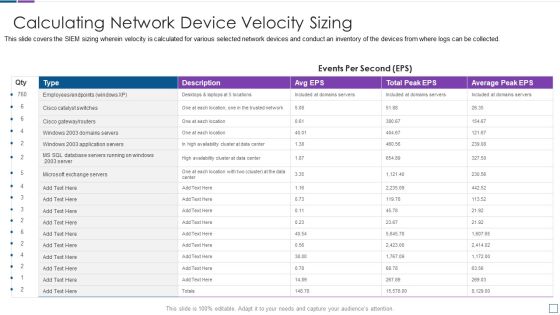
Real Time Assessment Of Security Threats Calculating Network Device Velocity Sizing Portrait PDF
This slide covers the SIEM sizing wherein velocity is calculated for various selected network devices and conduct an inventory of the devices from where logs can be collected. Deliver an awe inspiring pitch with this creative real time assessment of security threats calculating network device velocity sizing portrait pdf bundle. Topics like calculating network device velocity sizing can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
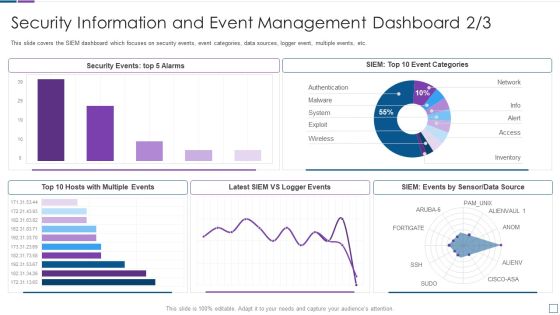
Real Time Assessment Of Security Threats Security Information And Event Management Dashboard Infographics PDF
This slide covers the SIEM dashboard which focuses on security events, event categories, data sources, logger event, multiple events, etc. Deliver an awe inspiring pitch with this creative real time assessment of security threats security information and event management dashboard infographics pdf bundle. Topics like security information and event management dashboard can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
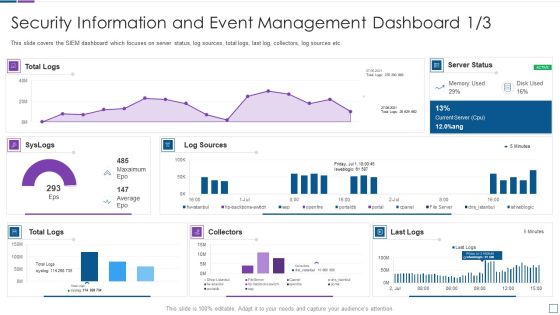
Real Time Assessment Of Security Threats Security Information And Event Management Microsoft PDF
This slide covers the SIEM dashboard which focuses on server status, log sources, total logs, last log, collectors, log sources etc. Deliver and pitch your topic in the best possible manner with this real time assessment of security threats security information and event management microsoft pdf. Use them to share invaluable insights on security information and event management dashboard and impress your audience. This template can be altered and modified as per your expectations. So, grab it now.

Real Time Assessment Of Security Threats Various SIEM Cost Plans Offered By Our Company Topics PDF
This slide covers the different costs plan offered by our company such as basic, intermediate, advanced, learning model costs. Deliver an awe inspiring pitch with this creative real time assessment of security threats various siem cost plans offered by our company topics pdf bundle. Topics like annual costs of tools, annual cost of personnel, one time cost can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
Real Time Assessment Of Security Threats Estimating Total Cost Of Ownership Of SIEM Icons PDF
This slide covers the total cost of ownership incurred by SIEM services which focuses on the costs of hardware, software, infrastructure, and support.Deliver an awe inspiring pitch with this creative real time assessment of security threats estimating total cost of ownership of siem icons pdf bundle. Topics like hardware, infrastructure, software, support can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
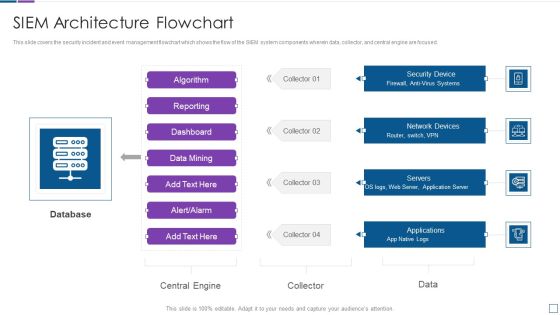
Real Time Assessment Of Security Threats SIEM Architecture Flowchart Sample PDF
This slide covers the security incident and event management flowchart which shows the flow of the SIEM system components wherein data, collector, and central engine are focused. Deliver an awe inspiring pitch with this creative real time assessment of security threats siem architecture flowchart sample pdf bundle. Topics like database, network devices, security device, servers, applications can be discussed with this completely editable template. It is available for immediate download depending on the needs and requirements of the user.
